Browser extensions are convenient little utilities that may adjust browsing experience and make it more comfortable for you personally. However, such a convenient shell – an applet to the legitimate program – could not have been ignored by malicious actors. In this post, I will uncover about malicious browser extensions, their nature and potential harm.
Can extensions be malicious?
Yes, extensions can be malicious, but the harm they can cause is quite specific. In terms of severity, a browser extension is not on par with full-fledged malware. Since extensions cannot go beyond the environment of a browser, they cannot infect the system, modify or delete system files, or directly manipulate the operating system (except for cases with vulnerabilities). However, some extensions can collect personal data, such as browsing history, passwords, and other confidential information, and transmit it to third parties without your consent. This makes them close to spyware and infostealers.
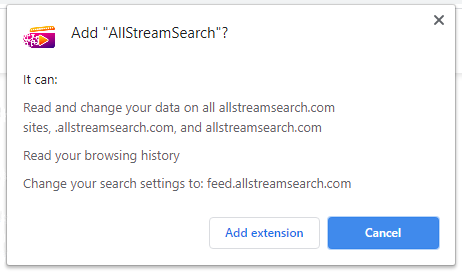
Depending on the type of extension, they can act differently and thus have distinct malicious potential: For example, some can open pop-up ads, redirect users to phishing sites or inject ads into websites where they are initially not present. Some extensions may contain malicious code that can initiate the download of other malicious programs. They can also change your browser settings without your knowledge, alter your homepage or search engine.
It is worth noting that a malicious browser extension these days is a rare find, unless you source them from official websites. Browser extensions are usually distributed through extension stores – platforms that have moderation and requirements, although they are not always effective for stopping malicious stuff. Should their system detect malicious activity or get a well-backed feedback on malignant behavior, the extension’s listing will cease to exist.
Main ways for dodgy extensions to spread are far away from the common routes of the Internet. Usually, they appear from a redirection made by a shady website that trades its traffic to random traffic brokers online. Upon redirection, the user will see an offer to install a “recommended extension” – to enhance security or to display the content. Sure enough, neither of these really happen after the installation.
Browser Hijacker
A browser hijacker is perhaps the most common type of malicious extension. Once installed, this extension changes your homepage and search engine. Even if the user navigates to google.com and performs a search, the extension redirects the query to its search engine. It also adds a special token to each search query, which modifies the search results. In the end, instead of relevant results, the user receives sponsored links that may not even match the query.
The primary risk of such extensions lies in the collection of personal information. The redirection that happens in the process throws the user through a selection of data broker sites, and each of them gathers whatever data they want. Aforementioned alteration of search results can casually throw the user to a phishing page. In some cases, this can result in the download of malicious software.
Adware
Adware extensions, as the name suggests, add advertisements to all the websites a user visits. Typically, these extensions disguise themselves as something useful or basic, such as extensions for finding discounts and promo codes. Notably, similar functionality is already present in Microsoft Edge. In practice, these extensions are useless; instead, they bombard the user with ads. Considering that adware does not do anything beyond the actions I’ve just mentioned, malicious browser extensions may be just an adware specimen.
Typical result of activity of adware browser extensions is hard to ignore. The browser starts to run slowly; clicking on any element on a page opens multiple tabs with ads, some of which may be malicious. Certain sites can automatically initiate the download of malicious software. Overall, the extension can seriously degrade the user experience and pose a threat to privacy.
Fake Cryptocurrency Wallet Extension
Fake cryptocurrency wallet extensions pose as legitimate crypto wallets, but their goal is to steal users’ credentials and funds. As I mentioned earlier, moderation in app stores is far from perfect, and sometimes malicious actors manage to place harmful extensions in official extension stores. These extensions may be disguised as popular wallets but have no actual affiliation with them.
When a user enters their credentials, such as private keys, mnemonic phrases, or passwords, the extension transmits this information to the malicious actors. This info allows the attackers to access the user’s real cryptocurrency wallets. Once they have access to the account, the attackers can transfer the funds to their accounts, leading to a complete loss of cryptocurrency for the user.
How to Stay Safe?
Malicious browser extensions are a type of threat you should not underestimate the dangers of. I have a few recommendations that can help you minimize the risks associated with malicious extensions. Firstly, try to avoid installing unnecessary extensions. I would recommend avoiding extensions from unverified sources altogether.
While most of us tend to click “next” to speed up the installation process when installing an extension from a store, I suggest paying attention to the developer and reading the reviews. Keep an eye on your installed extensions and promptly remove any that are unnecessary. Pay special attention when installing extensions related to cryptocurrency wallets. And finally, consider using decent anti-malware software that will notify you about the malicious activity that comes from such an extension.