The Security Blog From Gridinsoft
Dharma Ransomware Criminals Captured in Ukraine, Europol Reports
On November 28, 2023, Europol claimed successful detainment of ransomware operators, particularly related to Dharma and Hive ransomware. The operation…
InfectedSlurs Botnet Exploits Zero-Days to Spread Mirai Malware
The “InfectedSlurs Botnet,” a sophisticated cyber threat, has been uncovered by the Akamai SIRT in a recent development. This malware…
DarkGate and Pikabot Copy the QakBot Malware
According to researchers, the phishing campaign promoting the DarkGate and PikaBot malware is carried out by the authors or successors…
Phobos Ransomware Mimics VX-Underground Researchers
A new version of Phobos ransomware claims to be developed by VX-Underground, a malware info sharing community. Hackers again disguise…
Welltok Data Breach Exposes More Than 8 million Patients
Welltok, a healthcare Software as a Service (SaaS) provider, has reported unauthorized access to its MOVEit Transfer server, impacting the…
Google Is Trying to Get Rid of the Engineer Who Suggested that AI Gained Consciousness
Blake Lemoine, a senior software engineer at Google’s Responsible AI…
BlackCat Ransomware Attacks Italian University
An Italian university was hit by BlackCat this week. The…
A Bug in the System Allows Adding a new NFC Key for a Tesla Car
Austrian researcher Martin Herfurt has demonstrated a new way to…
Trojan Qbot Took Advantage of the Famous Follina Vulnerability
The researchers warned that the Qbot malware is already exploiting…
Chinese Hacker Group Revealed after a Decade of Undetected Espionage
The New Chinese Spying Threat Actor Identified SentinelLabs, an American…
Information Security Experts Told About The Linux Malware Symbiote That Is Almost Undetectable
BlackBerry and Intezer specialists spoke about the new Symbiote Linux…
Joint Operation: SSNDOB Personal Data Darknet Market Seized
What SSNDOB Was Before Its Servers Were Seized The US…
Beware: New SpaceX Bitcoin Giveaway Scam
Crooks Make Elon Musk a Bait for Wannabe Cryptotraders Scammers…
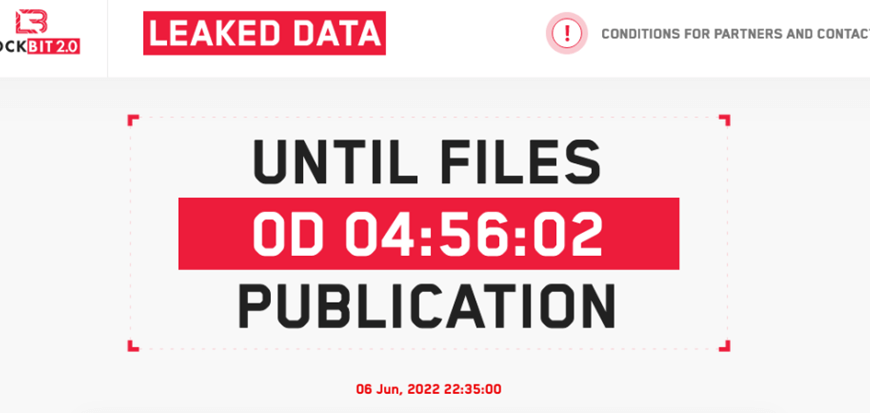
LockBit 2.0 Promises to Leak Mandiant Data
LockBit 2.0 announcement: real thing or vengeful trolling? On June…
Microsoft Is in No Hurry to Fix the Follina Vulnerability, Which Has Become a Real Disaster
Hackers are actively exploiting the critical 0-day Follina vulnerability, which…
Attackers Exploit MSDT Follina Bug to Drop RAT
Security specialists caution users about the exploitation of the recently…
New Cuba Ransomware Variant Involves Double-Extortion Scheme
What’s new in April Variant of Cuba Ransomware The Cuba…