Experts have discovered a Python-based Legion hacking tool that is sold via Telegram and is used as a way to hack into various online services for further exploitation.
Let me remind you that we also wrote that Microsoft Told How To Detect The Installation Of The BlackLotus UEFI Bootkit, and also that Experts discovered ESPecter UEFI bootkit used for espionage.
Attacks with Legion Hacker Tool
According to Cado Labs researchers, the Legion malware has modules for enumerating vulnerable SMTP servers, conducting remote code execution (RCE) attacks, exploiting unpatched versions of Apache, brute force cPanel and WebHost Manager (WHM) accounts, as well as interacting with the Shodan API and abusing AWS services.
The researchers say the malware shares similarities with another malware family, AndroxGh0st, which was first discovered by cloud security provider Lacework in December 2022.
Last month, SentinelOne published an analysis of AndroxGh0st, which showed that the malware is part of the AlienFox toolkit, which is offered to criminals to steal API keys and secrets from cloud services.
In addition to using Telegram to extract data, Legion is designed to hack web servers with CMS, PHP, or PHP-based frameworks such as Laravel.
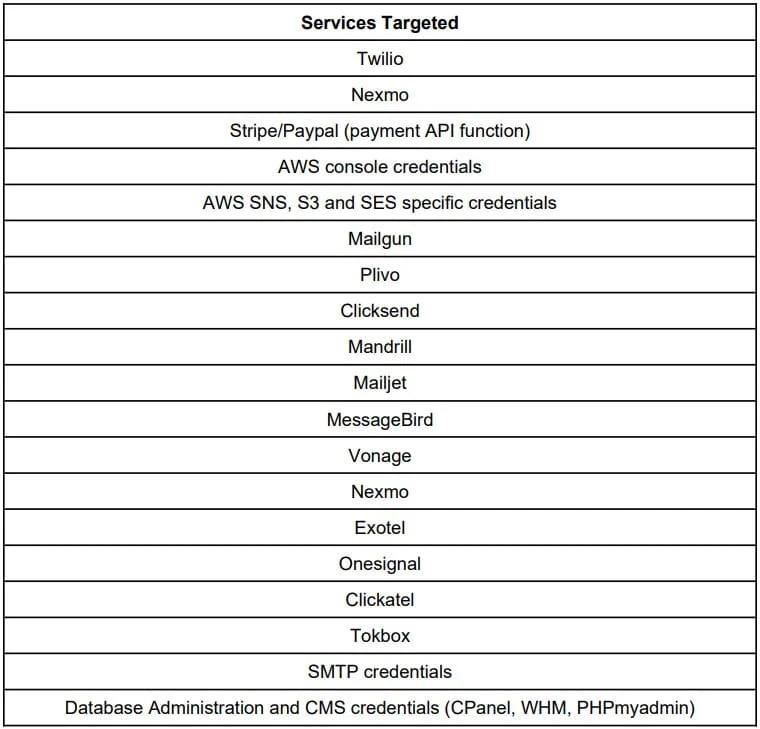
Other targeted services include SendGrid, Twilio, Nexmo, AWS, Mailgun, Plivo, ClickSend, Mandrill, Mailjet, MessageBird, Vonage, Exotel, OneSignal, Clickatell, and TokBox.
In addition, Legion extracts AWS credentials from insecure or misconfigured web servers and sends spam SMS to users of US operators, including AT&T, Sprint, T-Mobile, Verizon, and Virgin.
What’s the matter?
The main goal of the malware is to use the infrastructure of hijacked services for subsequent attacks, including bulk spam mailings and opportunistic phishing campaigns.
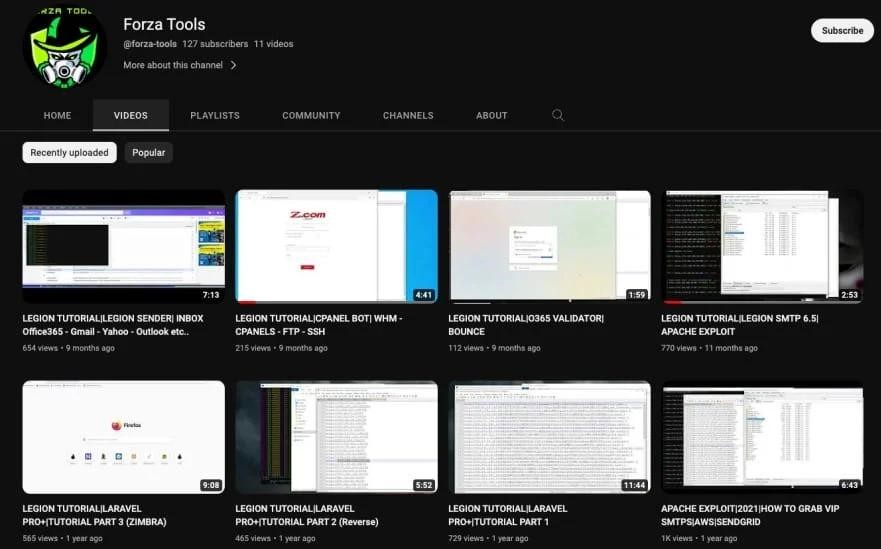
The researchers also discovered a YouTube channel (created June 15, 2021) containing tutorial videos on Legion. Experts conclude that “the tool is widespread and most likely is paid malware.”
The location of the creator of this tool, who uses the Telegram nickname forzatools, remains unknown, although the presence of comments in Indonesian in the code indicates that the developer may be Indonesian or located in that country.




