In July 2021, the infrastructure of REvil (Sodinokibi) was turned off without explanation, but now the information security specialists have noticed that the REvil servers are back online.
It was about a whole network of conventional and darknet sites that were used to negotiate a ransom, leak data stolen from victims, as well as the internal infrastructure of the ransomware.
Not long before that, in early July of this year, REvil operators carried out a large-scale attack on the customers of the well-known MSP solution provider Kaseya. For the attack, the hackers used 0-day vulnerabilities in the company’s product (VSA).
The problem was that most of the affected VSA servers were used by MSP providers, that is, companies that manage the infrastructure of other customers. This means that the cybercriminals have deployed the ransomware in thousands of corporate networks.
After this attack, the hackers demanded a ransom of $70 million, and then promised to publish a universal decryptor that can unlock all computers. The group soon “lowered the bar” to $50 million.
In addition, shortly before the attack on customers, Kaseya REvil hit the front pages of many publications as it attacked JBS, the world’s largest supplier of beef and poultry, as well as the second largest producer of pork. The company operates in the USA, Australia, Canada, Great Britain and so on, serving clients from 190 countries around the world. And also REvil attacked the electronics manufacturer Acer.
Since it has long been known that REvil is a Russian-speaking hack group, US President Joe Biden in a telephone conversation asked Russian President Vladimir Putin to stop the attacks of ransomware hackers operating from the territory of the Russian Federation. Biden said that if Russia does not take action after that, the United States will be forced to take it on its own.
After shutting down the entire infrastructure of the hack group, many experts believed that the group had broken up and will now rebrand, in an attempt to confuse law enforcement agencies and information security companies in the United States.
At the same time, Kaseya somehow obtained a universal key to decrypt its customers’ data. Then some experts suggested that Russian law enforcement officers received the decryption key from the attackers and handed it over to the FBI as a gesture of goodwill.
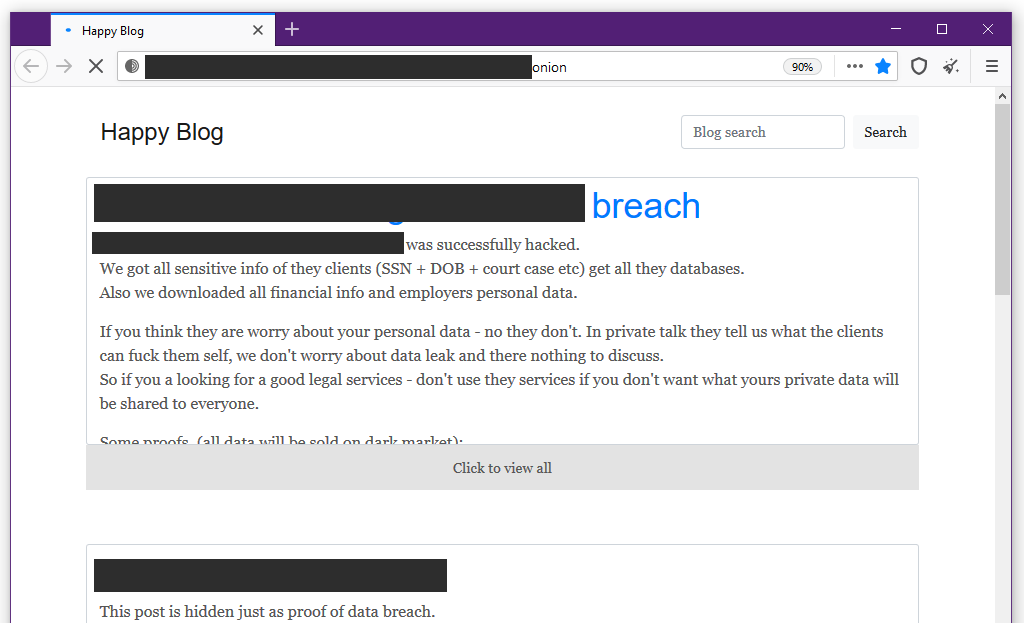
Now, almost two months after the shutdown, experts at Recorded Future and Emsisoft have noticed that the group’s blog and site where REvil operators used to post lists of victims who refused to negotiate and pay the ransom are back online.
The last update on the site was dated July 8, 2021, that is, no new data and messages were published. It is currently unknown if this means that the hack group is back to work, the servers were turned on again by mistake, or if it has something to do with the actions of law enforcement agencies.
Let me also remind you that I talked about the fact that REvil spokesman boasts that hackers have access to ballistic missile launch systems.