According to cybersecurity specialists from Cyble, attackers distribute miners and the RedLine infostealer using download sites for the fake MSI Afterburner utility. Over the past three months, more than 50 such fake resources have appeared on the network.
Let me remind you that we also talked that Djvu Ransomware Spreads via Discord, Carrying RedLine Stealer, and also that IS Specialists Discovered a New Version of Malware from Russian Hackers LOLI Stealer.
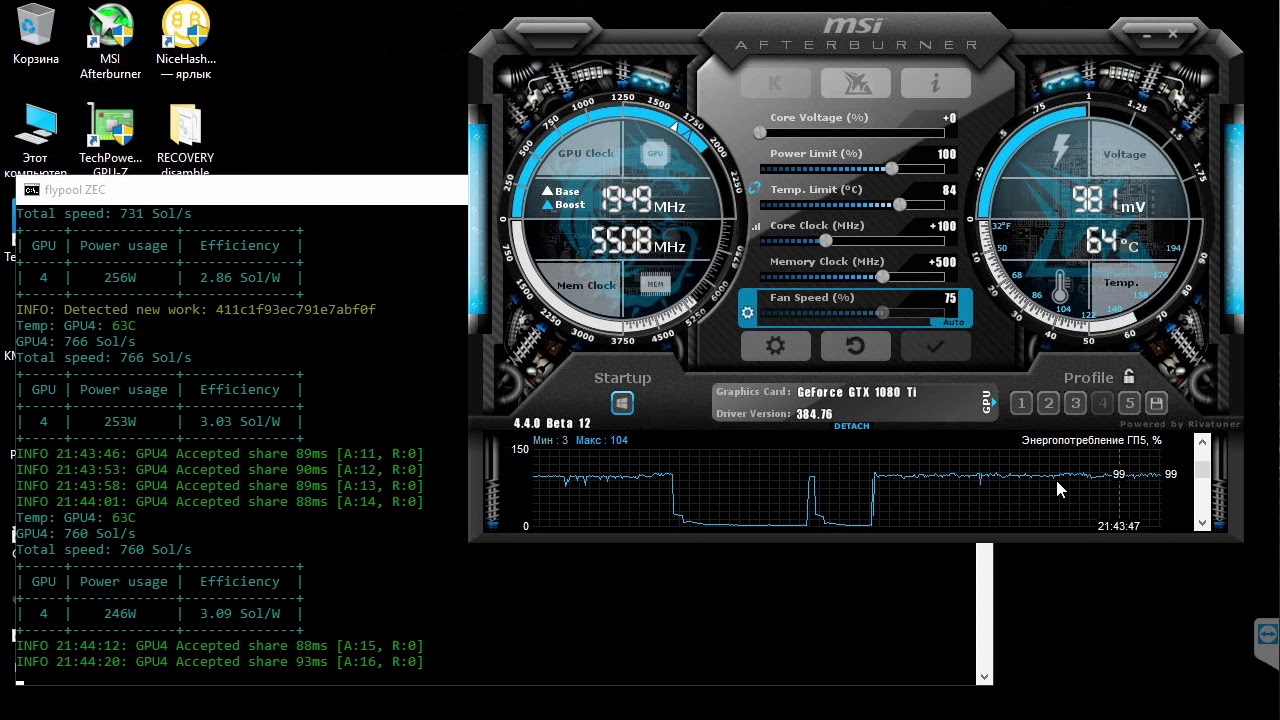
MSI Afterburner is the most popular GPU overclocking, monitoring and fine-tuning tool that can be used by owners of almost any video card, and thanks to this, it is quite naturally used by millions of gamers around the world.
Alas, the popularity of the utility has made it a good target for cybercriminals who abuse the fame of MSI Afterburner to attack Windows users with powerful graphics cards that can be used for cryptocurrency mining.
The researchers say that the campaign they found used various domains that could be mistaken by users for the official MSI website (besides, such resources were easier to promote using “black hat SEO”). Some of these domains are listed below:
- msi-afterburner–download.site
- msi-afterburner-download.site
- msi-afterburner-download.tech
- msi-afterburner-download.онлайн
- msi-afterburner-download.store
- msi-afterburner-download.ru
- msi-afterburner.download
- msafterburners.com
- msi-afterburnerr.com

Fake site
In other cases, the domains did not attempt to imitate the MSI brand and were likely promoted directly through private messages, forums, and social media:
- git[.]git[.]skblxin[.]matrizauto[.]net
- git[.]git[.]git[.]skblxin[.]matrizauto[.]net
- git[.]git[.]git[.]git[.]skblxin[.]matrizauto[.]net
- git[.]git[.]git[.]git[.]git[.]skblxin[.]matrizauto[.]net
Running the fake MSI Afterburner setup file (MSIAfterburnerSetup.msi) from these sites installed the real Afterburner. But at the same time, the installer silently downloaded and launched the RedLine malware, which specializes in data theft, and the XMR miner on the victim’s device.
Once installed, the miner connects to its pool using a hard-coded username and password, and then collects and transmits basic system data to attackers. In this case, the value of CPU max threads is set to 20, exceeding the number of threads even for the most modern processors. That is, the malware is configured to capture all the available power of the infected machine.
At the same time, the malware starts mining cryptocurrency only 60 minutes after the processor goes into standby mode, that is, it makes sure that the infected computer does not perform any resource-intensive tasks and, most likely, was left unattended.
In addition, the miner uses “-cinit-stealth-targets”, which allows it to pause activity and clean up GPU memory when running certain programs listed in the stealth targets section. These can be process monitors, antivirus software, device hardware resource viewers, and other tools that can help the victim detect a malicious process. Experts write that the miner hides in Taskmgr.exe, ProcessHacker.exe, perfmon.exe, procexp.exe and procexp64.exe.
While the miner quietly uses the resources of the victim’s system to mine Monero, the RedLine stealer works in the background, stealing passwords, cookies, browser information and data from any cryptocurrency wallets.
The Cyble report notes that so far, the components of this fake MSI Afterburner are poorly detected by antiviruses. For example, according to VirusTotal, the malicious installation file MSIAfterburnerSetup.msi is detected by only three security products out of 56, and the browser_assistant.exe file by only two products out of 67.