Operation Magnus Disrupts Infrasturcture of RedLine, META Stealers
On October 28, 2024 Dutch cyber police launched a website reporting a…
Malicious CPU-Z Copy Is Spread In Google Search Ads
Attackers are again abusing the Google Ads platform to distribute malicious advertising…
Redline and Vidar Stealers Switch to Ransomware Delivery
Cybercriminals who stand behind RedLine and Vidar stealers decided to diversify their…
Infostealers: How to Detect, Remove and Prevent Information-Stealing Malware in 2025
Information is one of our most valuable assets in today's digital world,…
Over 100k ChatGPT Accounts Are For Sale on the Darknet
According to a new report, over the past year, over 100k ChatGPT…
RedLine Stealer Issues 100,000 Samples – What is Happening?
Throughout the entire early May 2023, GridinSoft analysts team observed an anomalous…
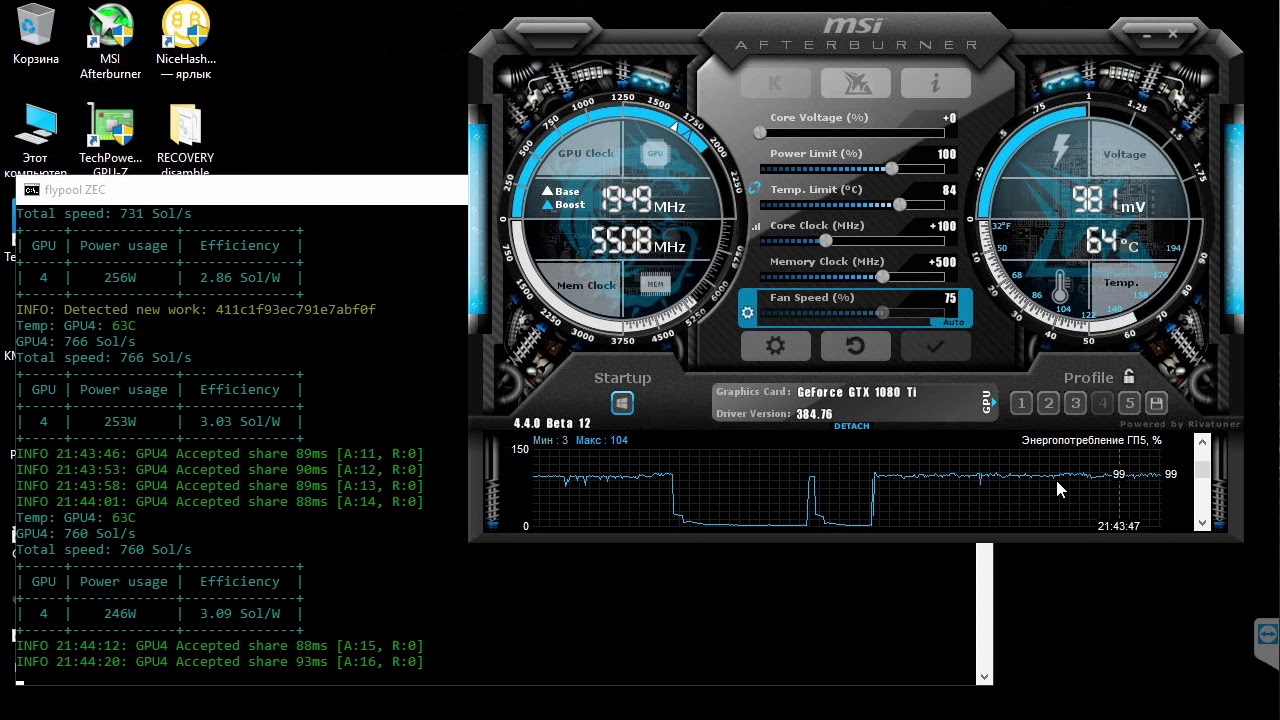
Fake MSI Afterburner Infects Users’ Machines with Miners and Stealers
According to cybersecurity specialists from Cyble, attackers distribute miners and the RedLine…
Magnat campaigns delivering fake installers
Cyber security specialists warn of the Magnat malicious distribution waves targeted at…