Vulnerability Found in Twitter Code That Provokes a “Shadowban” of the Victim
Recently, Twitter fulfilled a promise made by Elon Musk and published on…
Strange Enthusiasts Asked ChaosGPT to Destroy Humanity and Establish World Domination
Enthusiasts launched the ChaosGPT project, based on the open-source Auto-GPT, and AI…
Hackers Infect eFile Tax Filing Service with Malware
The eFile service, used by many Americans to file their tax returns…
Rilide Malware Steals Data from Chromium Browsers
Trustwave SpiderLabs specialists spoke about the new Rilide malware, which steals confidential…
Rorschach’s New Ransomware Is Named the Fastest to Date
Check Point analysts have discovered a new ransomware, Rorschach ransomware that has…
SFX Archives Can Sneakily Launch PowerShell
CrowdStrike warns that hackers are adding malicious functionality to self-extracting SFX archives…
Blogger Forced ChatGPT to Generate Keys for Windows 95
YouTube user Enderman demonstrated that he was able to force ChatGPT to…
Russian-Speaking Hack Group Winter Vivern Attacks Governments in Europe and Asia
The Russian-speaking hack group Winter Vivern (aka TA473 in the Proofpoint classification)…
The aCropalypse Vulnerability Poses a Threat Not Only to Pixel, but Also to Windows
Information security experts have discovered that the aCropalypse vulnerability, which allows restoring…
Attackers target .NET Developers with Malicious NuGet Packages
JFrog experts warned that attackers are targeting .NET developers through malicious packages…
ChatGPT Users Complained about Seeing Other People’s Chat Histories
Some ChatGPT users have reported on social media that their accounts show…
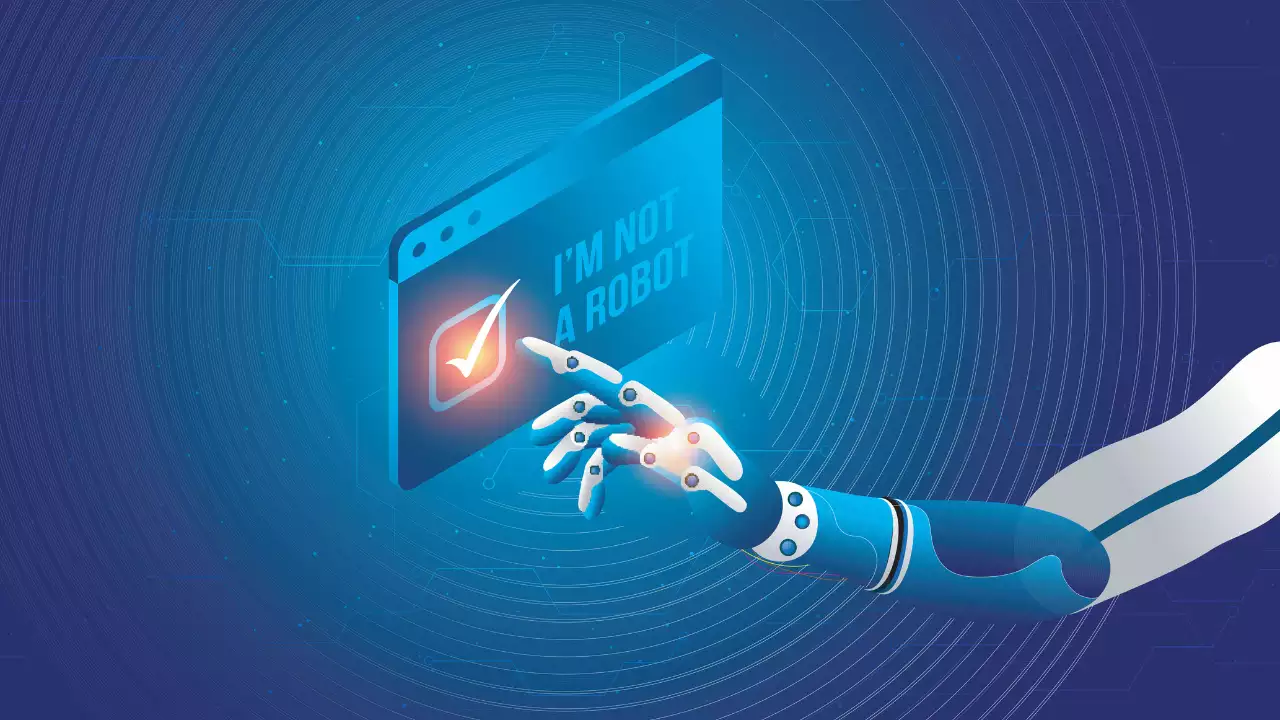
GPT-4 Tricked a Person into Solving a CAPTCHA for Them by Pretending to Be Visually Impaired
Prior to the launch of GPT-4 earlier this week, the researchers ran…