Information security experts report a hack of the Yanluowang hacker group, which compromised Cisco this summer. According to experts, internal chats of the group leaked to the network, showing that Yanluowang consists of Russian-speaking members.
KELA analysts write that the latest leak contains hack group chats dated January-September 2022, all communication in which took place in Russian. This is an interesting nuance since initially many believed that Yanluowang was a Chinese hack group. However, some time ago this opinion began to change, since in September the hackers were already associated with Evil Corp.
Researchers say that in chats you can find conversations of group members known under the nicknames saint, killanas, and stealer. It is believed that the saint leads the group, while killanas is engaged in coding. Moreover, according to some sources, it has already been possible to calculate the pseudonyms of the attackers on various hack forums, and according to other sources, Yanluowang members have already been completely doxed, including their real names, social media accounts, and other details.

Here is what the experts have already managed to find among the “merged” data:
- according to the chat logs, Yanluowang has existed since at least the fall of 2021, and in one of the conversations saint mentions the Nyx malware, which seems to be also used by his team;
- from the conversation between the stealer and the tester under the nickname felix, we can conclude that the version of the Yanluowang malware for ESXi is already in development;
- On May 14, 2022, saint revealed that the group “earned” one million US dollars in 2022 (it’s not clear if this was the total amount of buyouts or the largest of them).
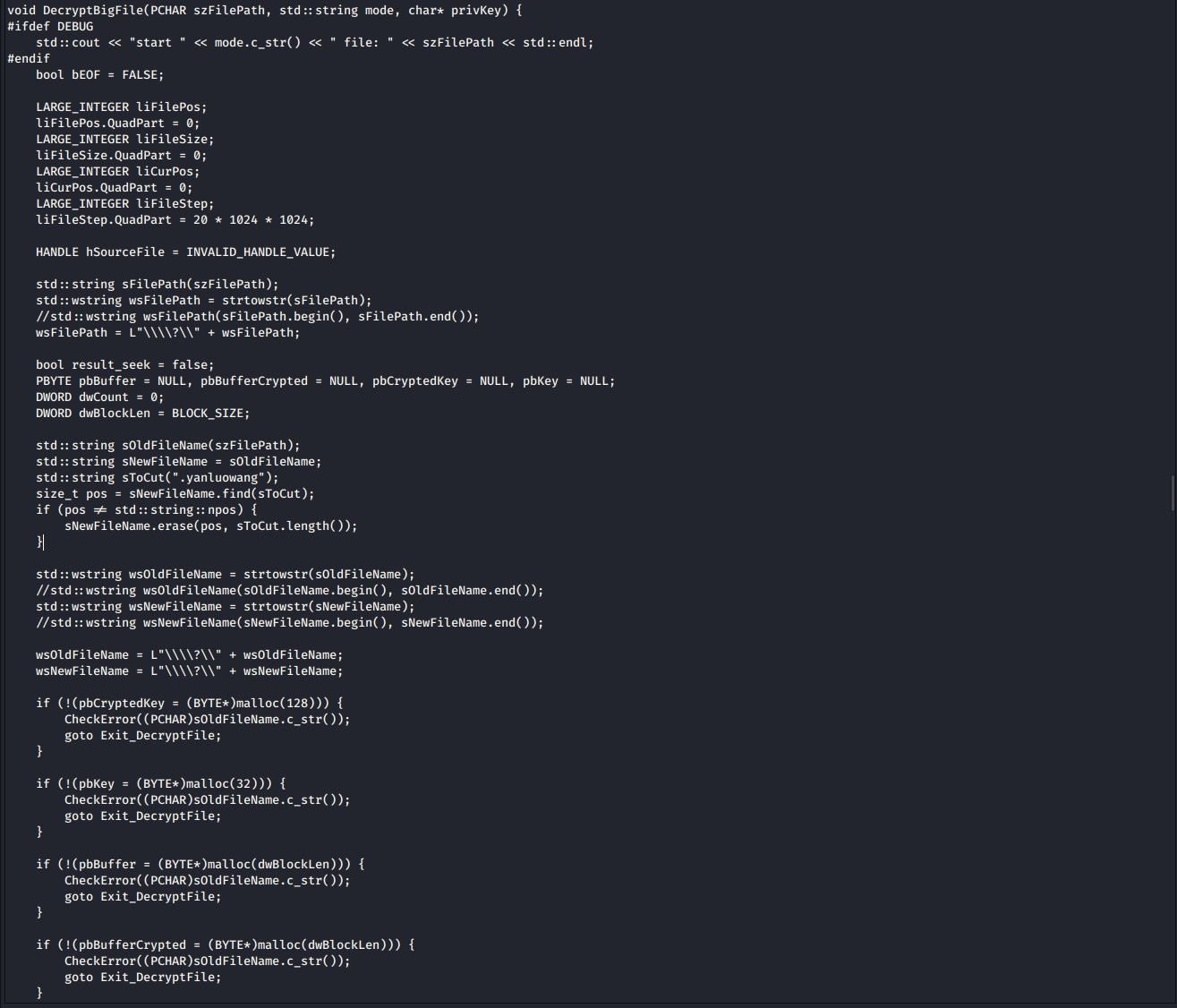
In addition to the logs, you can even find screenshots on the network containing the source code for the decryption procedure for the Yanluowang ransomware.
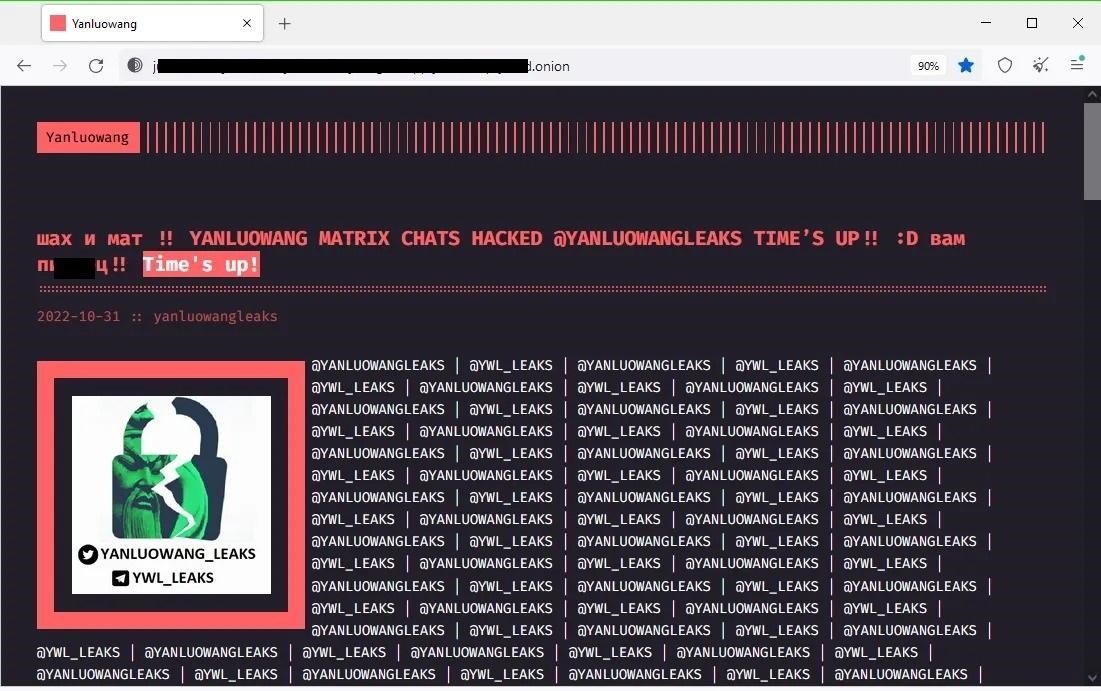
According to Risky Business, this leak appears to be the result of a major hack. Unknown individuals not only took control of the Matrix internal chat server used by the group but also compromised the Yanluowang “leak site” on the dark web. Through the defacement of this resource, the hackers demonstrated their skills, and they posted a new blog entry on the topic. The post contained links to Telegram and Twitch accounts, where links to stolen chat logs were posted.
It is currently unclear who was behind the hack, but there are several theories, ranging from the classic version that it was a disgruntled former member of the group or an unknown information security specialist, and ending with the exotic version that it was the revenge of the Cisco security service for the hack that occurred in May.
Nevertheless, experts are confident that after such a large-scale compromise, Yanluowang operations can be put an end to, as other cybercriminals are unlikely to want to deal with a compromised group whose operational security is in question.