The grand total of 21 security flaws was discovered in Sierra Wireless AirLink routers firmware. The vulnerabilities allow for remote code injection, unauthenticated access, DoS attacks, and else. As such network devices are commonly used in industrial manufacturing and applications the like, the impact of such attacks may be rather serious.
Sierra AirLink Routers Have 21 Vulnerabilities
As Forescout Vedere researchers describe in their research, the AirLink lineup of devices contains 21 software vulnerabilities. Among them, only one issue got the CVSS score over 9, which is considered critical. RCE vulnerabilities and a couple of ones that may allow for unauthorized access are rated 8.1 to 8.8. Several other noteworthy issues, particularly ones that cause Denial of Service, are rated at CVSS 7.5.
| Vulnerability | Description | CVSS Score |
|---|---|---|
| CVE-2023-41101 | RCE vulnerability in OpenNDS | 9.6 (Critical) |
| CVE-2023-38316 | RCE vulnerability in OpenNDS | 8.8 |
| CVE-2023-40461 | XSS vulnerability in ACEmanager | 8.1 |
| CVE-2023-40464 | Unauthorized Access in ALEOS firmware | 8.1 |
| CVE-2023-40463 | Unauthorized Access in ALEOS firmware | 8.1 |
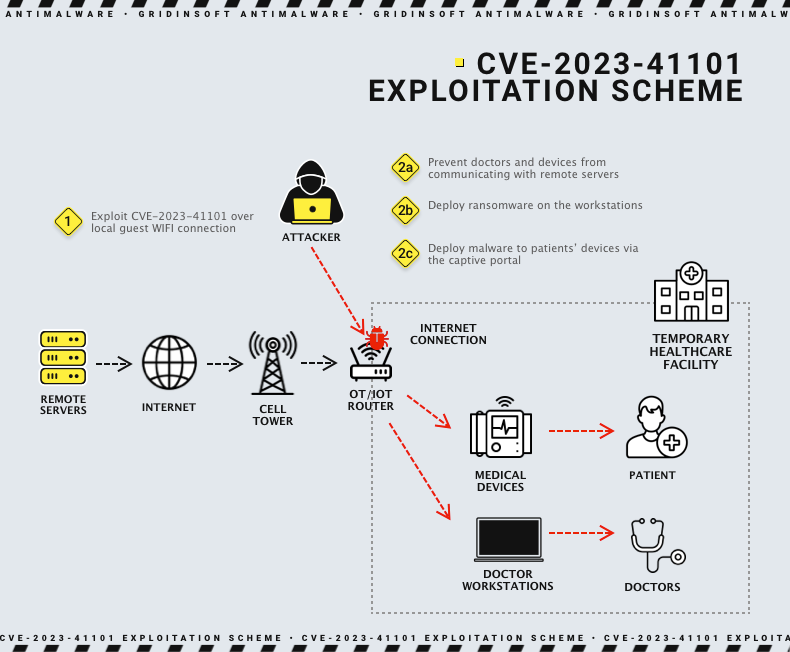
Researchers did a detailed description of the potential exploitation cases for two of the most critical vulnerabilities. For CVE-2023-41101, a hacker can take over the router by overflowing the buffer in OpenNDS captive portal. Using the lack of length limitation in GET requests, it is possible to make the router execute arbitrary code. By controlling the router, adversaries can disrupt the operations related to the mentioned interface.
#2 in the list, CVE-2023-40463, requires an attacker to possess a router similar to the one it tries to attack. By digging through the device’s software elements and applying some hash cracking magic, it is possible to obtain the diagnostic shell password. Further, using a bit of social engineering, adversaries may connect to the actual router and enter its diagnostic interface using the password they’ve obtained earlier. With such access, it is possible to inject malware to the router, force it to malfunction, or execute your commands remotely.
Available Mitigations
Despite such a worrying amount of exploits, all of them allegedly receive a fix in the latest version of the firmware for AirLink devices. ALEOS 4.17.0 should address all the flaws, and, if some incompatibilities are in the way, customers may stick to version 4.9.9. The latter is not vulnerable to named vulnerabilities except for ones that touch OpenNDS captive portals.
Researchers who found all the issues also offer their own mitigation for the vulnerabilities that allow delaying the patch installation. Though, as it usually happens to all the stopgap solutions, they are not ideal and do not guarantee the effect.
- Disable unused captive portals and related services, or put them under restricted access. This reduces the attack surface for vulnerabilities that target OpenNDS.
- Use a web app firewall to filter the requests and block the packets of a suspicious source. This mitigation works against XSS and DoS vulnerabilities.
- Change the default SSL certificates. Forescout recommends doing this to all the routers, not only to Sierra Wireless ones.
- Implement an intrusion detection system that monitors IoT/OT devices as well. This allows for controlling both connections from outside the network and ones within it.
What are Sierra AirLink Routers?
Have you ever wondered, how does the Wi-Fi in a public transport function? Or how all the machinery in a huge workshop is connected and centrally managed even though it is not static? Well, Sierra’s devices are the answer. Their routers are industrial-grade wireless connectivity devices that are used in dozens of industries – starting from public transportation and all the way up to aerospace & defense.
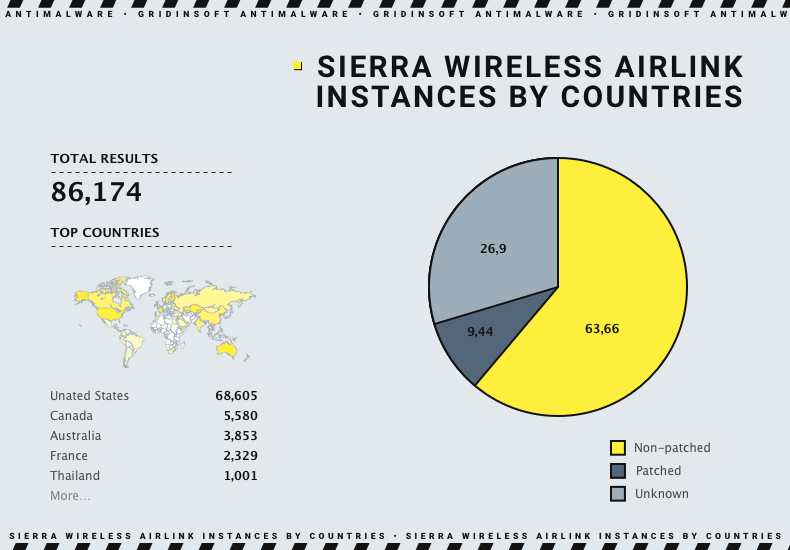
What is particularly concerning for this story is the extensive use of AirLink routers in critical infrastructure. Factories, transportation – they are important, though not as continuously demanded as water treatment, emergency services and energy management. And since IoT more and more often attracts hackers’ attention, the actions should be taken immediately. Considering the extensive use of vulnerable AirLink devices in the US, it may be the perfect Achilles’ heel for cyberattacks that target critical infrastructure and even government.