The Security Blog From Gridinsoft
Genesis Market Seized by FBI
Genesis Market, a Darknet marketplace for stolen information, was reportedly seized by the FBI on Tuesday, April 4, 2023. The…
Blogger Forced ChatGPT to Generate Keys for Windows 95
YouTube user Enderman demonstrated that he was able to force ChatGPT to generate activation keys for Windows 95. Let me…
Russian-Speaking Hack Group Winter Vivern Attacks Governments in Europe and Asia
The Russian-speaking hack group Winter Vivern (aka TA473 in the Proofpoint classification) has been actively exploiting a vulnerability in Zimbra…
APT43 Funds Cybercrime With Stolen Crypto
Researchers have identified a new state-backed hacker group in North Korea. The group in question is the North Korean hacker…
Ransomware Actors Target IBM’s Aspera Faspex
File transfer utility Aspera Faspex, developed by IBM, became a riding mare of cybercriminals. A vulnerability discovered in the past…
The researcher found that every 142nd password is “123456”
Ata Hakçıl, a Turkish student and independent researcher, has done…
US cyber command warned about dangerous vulnerability in PAN-OS
The US cyber command warned that in PAN-OS was discovered…
Check Point: hackers exploit BLM theme for attacks
Check Point analysts reported that hackers are actively exploiting the…
Lucifer malware uses many exploits, is engaged in mining and DDoS attacks
Palo Alto Networks experts have prepared a report on Lucifer…
Evil Corp returns to criminal activity with WastedLocker ransomware
Fox-IT experts talked about the latest activity of the famous…
Hackers force users to solve CAPTCHA
Microsoft analysts have discovered a malicious campaign, in which hackers…
AMD plans to fix SMM Callout bugs in its processors by the end of June
AMD reports that firmware updates will be released for three…
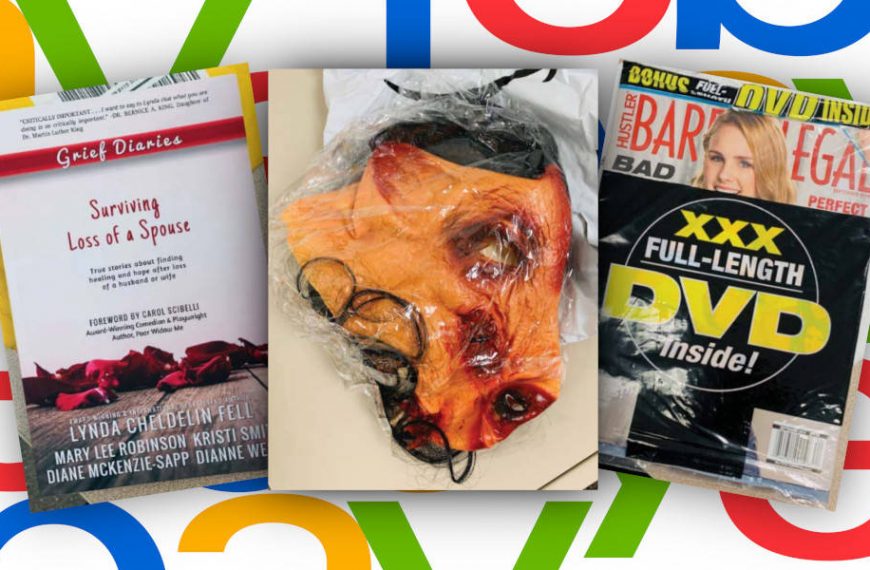
eBay employees organized persecution and intimidation of a family of bloggers
Six former eBay employees became involved in a strange trial.…
Experts discovered Chrome largest spyware installation campaign
Specialists from the company Awake Security reported about currently perhaps…
Vulnerabilities in old GTP protocol could affect 4G and 5G networks
Experts cautioned that vulnerabilities in the old GTP (GPRS Tunneling…
GitHub will replace the term “master” with a more neutral one
Nat Friedman, leading GitHub after acquiring Microsoft in 2018, said…
Italian IT company CloudEyE collaborated with ransomware operators
For about four years, the Italian company CloudEyE was engaged…