The Security Blog From Gridinsoft
GPT-4 Tricked a Person into Solving a CAPTCHA for Them by Pretending to Be Visually Impaired
Prior to the launch of GPT-4 earlier this week, the researchers ran a lot of tests, such as whether the…
New Microsoft SmartScreen Bypass Technique Causes Concerns
Microsoft SmartScreen proved to be an effective way of approving the legitimacy of the application – by checking one’s certificate.…
The FBI Said That the Damage from Cyberattacks in 2022 Exceeded $10 Billion
The FBI’s Internet Fraud Complaint Center (IC3) has released its annual 2022 Internet Crime and Cyber Attack Damage Report. During…
North Korean Hackers Attack Cybersecurity Specialists by Offering Them Jobs via LinkedIn
Mandiant experts noticed that North Korean hackers have focused their attention and attacks on information security specialists. Attackers try to…
Incoming Silicon Valley Bank Related Scams
Mind-bending globe-scale events always attract a lot of attention. Newsmakers, politicians and simple rubbernecks pay a lot of attention to…
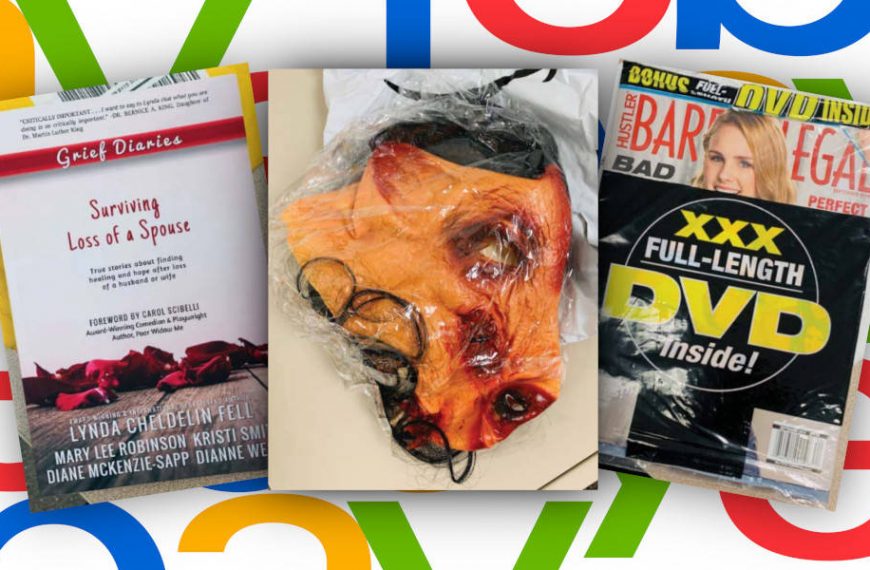
eBay employees organized persecution and intimidation of a family of bloggers
Six former eBay employees became involved in a strange trial.…
Experts discovered Chrome largest spyware installation campaign
Specialists from the company Awake Security reported about currently perhaps…
Vulnerabilities in old GTP protocol could affect 4G and 5G networks
Experts cautioned that vulnerabilities in the old GTP (GPRS Tunneling…
GitHub will replace the term “master” with a more neutral one
Nat Friedman, leading GitHub after acquiring Microsoft in 2018, said…
Italian IT company CloudEyE collaborated with ransomware operators
For about four years, the Italian company CloudEyE was engaged…
SGAxe attack endangers Intel processors
As part of the June “Update Tuesday,” Intel fixed more…
On June “Patch Tuesday” Microsoft fixed 129 vulnerabilities in its products
“Patch Tuesday” this month became the largest in the history…
Tycoon ransomware uses exotic JIMAGE format to avoid detection
BlackBerry experts have discovered an unusual multi-platform (for Windows and…
Hacker forums show growing demand for credentials from YouTube channels
IntSights experts found that recently in the darknet there increased…
Users seldom change passwords even after data leaks
Researchers from Carnegie Mellon University found that users seldom change…
Vulnerability in Indian TikTok clone allows hacking user profiles
The Hacker News reports that Indian security specialist Rahul Kankral…
Octopus Scanner Malware Found On GitHub
GitHub developers have issued a warning about the appearance of…