Brett Callow, a cybersecurity analyst at Emsisoft, shared information on his Twitter about the broadened tactics the LockBit ransomware group applies to its victims.
Imagine a firm gets attacked by ransomware. It is not a novelty that, besides encrypting the data belonging to the company (to demand ransom for giving the data back,) the crooks also steal the data before its encryption. They can sell the data afterward. It is called a double-extortion scheme.
LockBit Weaponizes Its Victim’s Clients
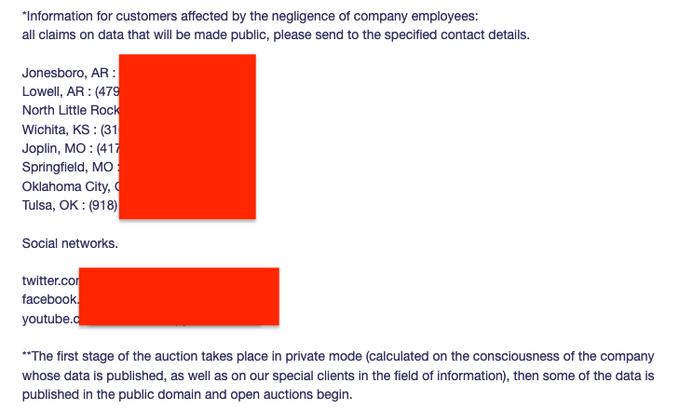
However, if the enterprise administration doesn’t negotiate with the racketeers, they have thought up a way to make them do so. They contact the clients, partners, and employees of the victimized company and notify them about the company’s total neglect of the safety of data that has to do with people who trust the company and deserve its responsible care. Ransomware group thus encourages affected individuals to push the companies to do something about the leak.
Callow calls it ‘weaponizing’ clients (not only clients, though.) Ransomware gangs share links to specially created web pages where alleged victims can check whether their data ended up in the possession of the malefactors. Sometimes crooks allow paying for excluding an individual’s information from the total pile of the stolen data, while sometimes, it is impossible. However, there is no guarantee that such a procedure is technically possible since ransomware must have the relevant architecture to allow partial decryption of specified data alongside full decoding.
In the LockBit case, clients of victimized companies are warned about auctions that are going to take place before the personal data (including names, addresses, social security numbers, phone numbers, emails, etc.) is published.
Brett Callow notes that LockBit is not the first ransomware gang to practice such ‘client weaponizing.’ ALPHV and Cl0p operators did the same thing earlier this year and last year, respectively.
How do Auctions Look?
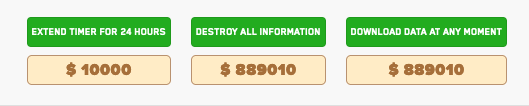
Even more interesting is that the LockBit victim companies, while being possibly pushed by their employees and customers, have a chance to play a game of patience on the auction: they are allowed to destroy all the malefactors-controlled data at once by paying a certain amount of money. At the same time, anyone can pay the same amount to download all the information. Both options get cheaper and cheaper simultaneously. On the one hand, nobody forces company administrators to pay the initial amount. On the other hand, as soon as the price gets low enough, someone might want to buy the data to download it. And that’s it!




