Specialists from the cybersecurity company Symantec reported attacks by the cybercriminal group Shuckworm (Armageddon or Gamaredon) on Ukrainian organizations using a new version of the Pteredo (Pteranodon) custom backdoor.
The group, linked by experts to Russia, has been carrying out cyber-espionage operations against Ukrainian government organizations since at least 2014.
According to experts, the group carried out more than 5 thousand cyberattacks on 1.5 thousand public and private enterprises in the country.
By the way, we talked about the fact that hacker groups split up: some of them support Russia, others Ukraine.
Pteredo has its origins in hacker forums, where it was acquired by Shuckworm in 2016. Hackers began active development of the backdoor, adding DLL modules to it for data theft, remote access, and penetration analysis.
In addition to Pteredo, Shuckworm has also used the UltraVNC remote access tool and Microsoft’s Process Explorer to process DLL processes in recent attacks.
Note: Let me remind you that even before the escalation of hostilities, Microsoft discovered the WhisperGate wiper attacking Ukrainian users.
If we compare Shuckworm attacks on Ukrainian organizations since January 2022, we can conclude that the group has hardly changed its tactics. In previous attacks, variants of Pteredo were downloaded to the attacked systems using VBS files hidden inside the document attached to the phishing email.
7-Zip files are unzipped automatically, which minimizes user interaction (the same files were used in the January attacks).
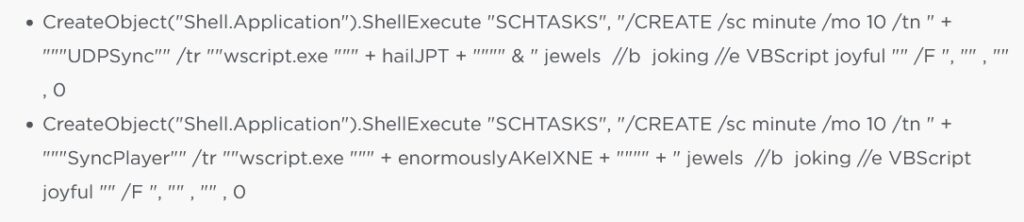
For example, one variant of Pteredo is a modified self-extracting archive containing obfuscated VBScripts that can be decompressed with 7-Zip. It then adds them as a scheduled task to ensure persistence:
The script also copies itself to [USERPROFILE]\ntusers.ini file.
The two newly created files are more obfuscated VBScripts.
- The first is designed to gather system information, such as the serial number of the C: drive, and sends this information to a C&C server.
- The second adds another layer of persistence by copying the previously dropped ntusers.ini file to another desktop.ini file.
Although Shuckworm is a highly professional group, its infection tools and tactics have not improved over the past few months, making it easier to detect and simplify methods of protection.
Currently, Pteredo is still actively developed, which means that hackers can work on a more advanced, powerful and undetectable version of the backdoor, as well as modify their attack chain.