Ivanti, the provider of a wide range of management solutions for corporations, have apparently taken up the baton from Ipswich, the vendor of an infamous MOVEit MFT. Analysts discovered 2 severe vulnerabilities in its EPMM over the last 10 days, and the company released urgent fixes. However, the patch for the CVE-2023-35078 appears to be vulnerable for exploitation through the same pattern.
Ivanti EPMM Vulnerabilities Keep Going
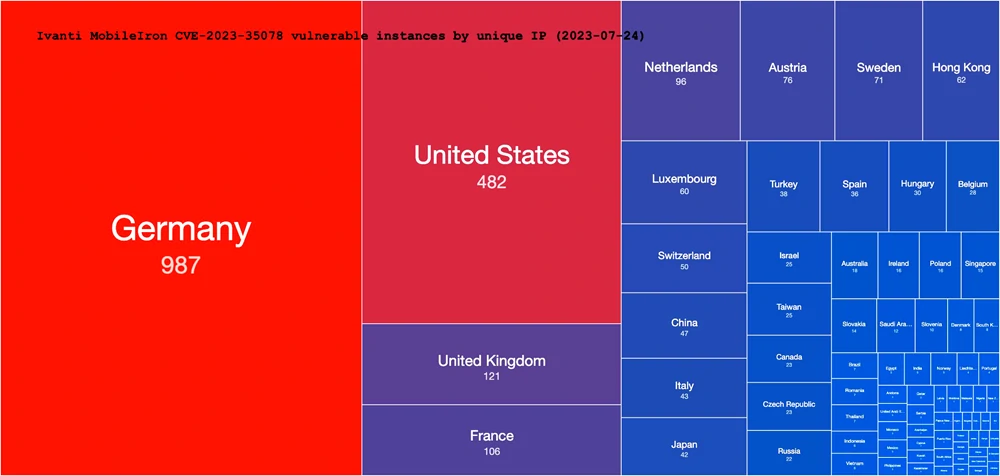
On July 25, 2023 Ivanti released a note regarding the vulnerability in their EPMM device management software. They offered to install a patch to secure the software vulnerability (dubbed CVE-2023-35078) that allowed hackers to bypass authentication and access all the functionality of the app. Obviously, it received a top 10/10 CVSS rating. Bad news here is that the vulnerability was reportedly exploited since April 2023. The patch offered by the company allegedly closes the unauthorised access capabilities.
Soon after, another security loophole was discovered. CVE-2023-35081 is a path traversal vulnerability that allows for unauthorised access to the files stored on the server. Unfortunately, the scale of this breach exploitation is around the same as the previous one – hackers used them along to fulfil different targets within one attack.
Thing is, not everything is ideal for the patched 2023-35078 vulnerability. Researchers found a way to do pretty much the same trick to the patched version as hackers did earlier. The new breach is possible for older versions of the EPMM – 11.2 and below – and received an index of CVE-2023-35082. Even after the patch, applications were not able to provide a sustainable security level. Fortunately, no cases of exploitation of this vulnerability have been discovered yet. But as we know, once 0-day vulnerability becomes an n-day one, its usage becomes much more widespread.
How to protect against CVE-2023-35082?
The only – and the most effective advice there is updating Ivanti EPMM to any of the versions newer than 11.2. It may be troublesome to perform such an update simultaneously in a huge network of devices, though efforts there are much more preferable than efforts on fixing the outcome of a cyberattack. Though, there could be several other solutions – not preventive, but still effective.
Adopt cybersecurity solutions with zero-trust policy. The baddest modern cyberattacks are done through vulnerabilities in trusted software, the only solution is to not trust at all. EDR/XDR solutions that are built around such a conception have their downsides, apparently, but the effectiveness of their protection is undoubted. Either it is a hand-made utility or a program with over 1 million users – it will thoroughly check all the actions it does.
Use UBA and SIEM to improve visibility and response in the environment. The aforementioned zero-trust security systems will greatly appreciate additional sources of information. This is almost essential in large networks that consist of different types of devices. Being aware and being able to respond as quickly as possible is vital in modern cybersecurity, when the count can go on for minutes.





