ChatGPT Users Complained about Seeing Other People’s Chat Histories
Some ChatGPT users have reported on social media that their accounts show other people's chat histories. Let me remind you that we also wrote that Russian Cybercriminals Seek Access to…
Financial Assistance Department Email Scam to call (855)-XXX-XXXX
Email is one of the oldest ways to exchange information over the Internet. So, email scams are the most common type of scam that originated, as it is believed, back…
BreachForums is down. Things got worse?
Recently, one of BreachForums administrators nicknamed PomPomPurin was arrested by the FBI. That event took place on March 17, 2023, and since then, another administrator of that forum assured that…
5 Tips to Improve Your Privacy on the Web
Nowadays, online privacy is a crucial concern that we should all be aware of, especially when it comes to using a web browser. It contains all the information about our…
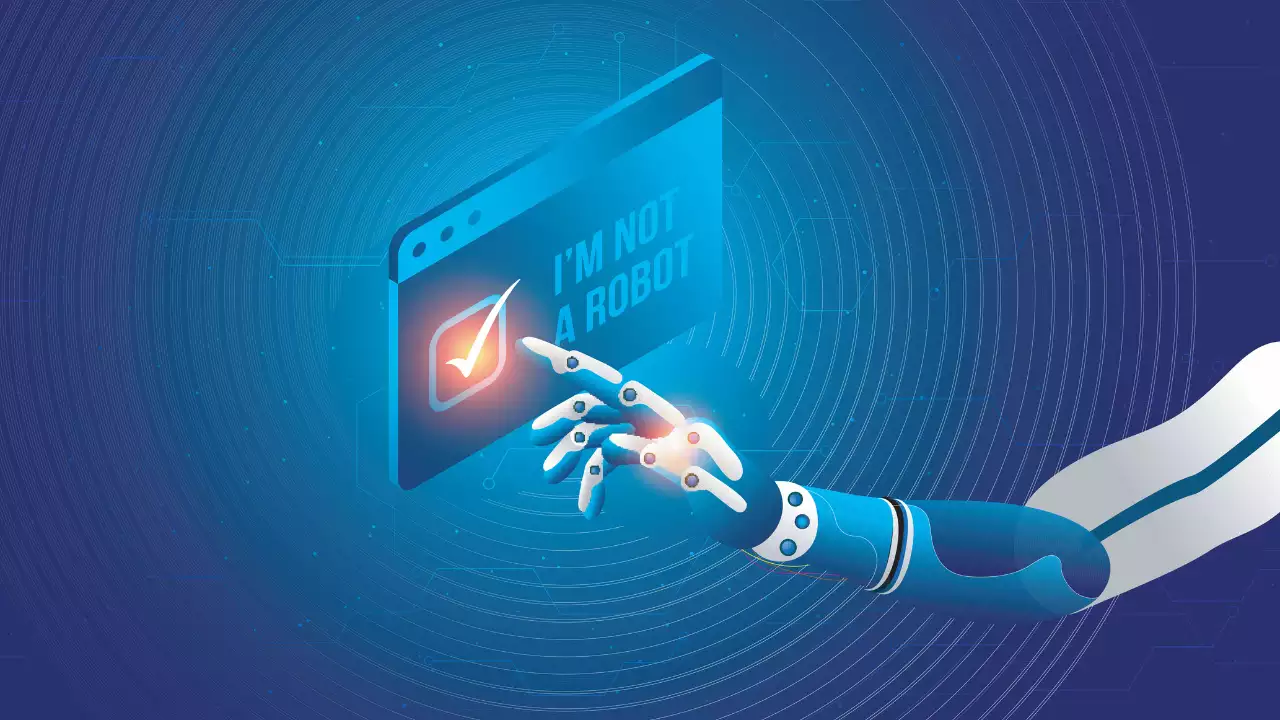
GPT-4 Tricked a Person into Solving a CAPTCHA for Them by Pretending to Be Visually Impaired
Prior to the launch of GPT-4 earlier this week, the researchers ran a lot of tests, such as whether the latest version of OpenAI's GPT could demonstrate freedom, desire for…
New Microsoft SmartScreen Bypass Technique Causes Concerns
Microsoft SmartScreen proved to be an effective way of approving the legitimacy of the application – by checking one’s certificate. With time, Microsoft did a lot of work making it…
The FBI Said That the Damage from Cyberattacks in 2022 Exceeded $10 Billion
The FBI's Internet Fraud Complaint Center (IC3) has released its annual 2022 Internet Crime and Cyber Attack Damage Report. During the year, the FBI reportedly received more than 800,000 cybercrime-related…
North Korean Hackers Attack Cybersecurity Specialists by Offering Them Jobs via LinkedIn
Mandiant experts noticed that North Korean hackers have focused their attention and attacks on information security specialists. Attackers try to infect researchers with malware in the hope of infiltrating the…
Incoming Silicon Valley Bank Related Scams
Mind-bending globe-scale events always attract a lot of attention. Newsmakers, politicians and simple rubbernecks pay a lot of attention to such a loud events, and a recent Silicon Valley Bank…
Mobile Malware Threat Landscape — 2022 Summary
Today, a smartphone is much more than just a way to reach someone on the phone. Our smartphones contain valuable information, such as private photos, logins, and passwords for online…
Emotet Has Resumed Activity after a Three-Month Break
Experts noticed that this week Emotet resumed its activity and after a three-month "rest" began to send malicious spam again. So far, information security specialists have not found any additional…
Acronis Breached, Internal Data Leaked
Acronis, a Swiss-based information technology company that provides file recovery services for hacked companies was breached earlier this month. The breach became public on March 9, 2023, when a hacker…