Recently malicious actors started using malvertising to spread BlackCat ransomware. They use cloned webpages of popular freeware applications, particularly WinSCP utility. Such downloads result in an infection chain, that consists of a dropper, a backdoor, and, finally, the ransomware.
Operators Distributing Ransomware Disguised as WinSCP
Researchers acknowledged that BlackCat operators were using malicious ads to distribute fraudulent WinSCP file transfer application installers. In this case, the distribution involved a Web page for the well-known WinSCP application, an open-source Windows file transfer application. In a nutshell, attackers use SEO poisoning to spread malware through online advertisements. They hijack a select set of keywords to display phishing site ads on Bing and Google search results pages. These ads redirect unsuspecting users to a phishing copy of the original web page.
Thus, scammers try to make users download the malware masked as a legitimate app. However, the victim gets a backdoor containing a Cobalt Strike beacon instead of a legitimate WinSCP app. The backdoor, in turn, connects to a remote server for subsequent operations. It also uses legitimate tools like AdFind to facilitate network discovery. Attackers use the access granted by Cobalt Strike to download programs to perform reconnaissance, tallying, lateral movement, antivirus software circumvention, and data exfiltration. That tactic is aimed at infecting corporate users – a pretty unique approach when it comes to ransomware spreading methods.
According to the researchers, the attackers managed to steal top-level administrator privileges, which allowed them to perform post-exploitation actions. In addition, they tried to set up persistence with remote management tools such as AnyDesk and gain access to backup servers. Unfortunately, this is not an isolated case but rather a trend. We’ve already told you how attackers use the Google Ads platform to spread malware.
What Is BlackCat Ransomware?
BlackCat is a dangerous malware strain that emerged in November 2021. It is operated by a Russian-speaking cybercrime group called ALPHV. It is the first significant malware written in the Rust programming language and can attack Windows and Linux systems. BlackCat uses a triple-extortion tactic in its ransomware campaigns, targeting various industries, including finance, manufacturing, and legal services. It has compromised around 200 enterprise organizations between November 2021 and September 2022 and is related to other ransomware variants such as BlackMatter and DarkSide.
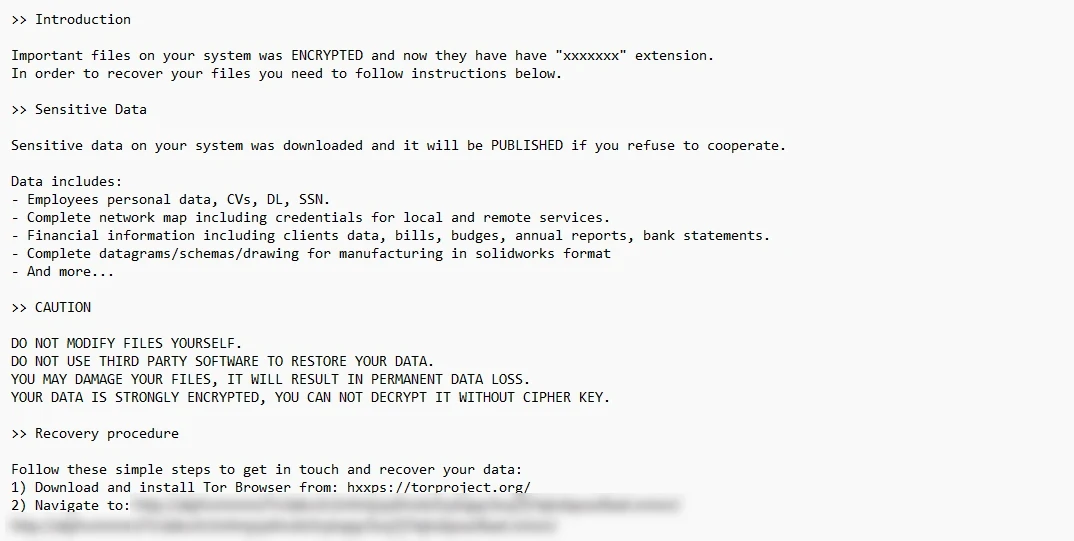
BlackCat gang is known for being pretty radical when it comes to data leaks. Once the company they’ve attacked refuses to pay, hackers open access to all the extracted data. And contrary to other ransomware gangs, ALPHV/BlackCat does this on the clear web website. In the past year, they exposed a huge number of people by publishing data extracted from Allison Resort and University of Pisa.
General recommendations
As for organization-level protection, there’s a whole set of recommendations that organizations that care about security for themselves and their customers take for granted. A detailed understanding of attack scenarios enables organizations to identify vulnerabilities that can lead to compromise and critical damage and take the necessary steps to prevent them. However, what about individual users? Here we recommend following these simple but effective tips:
- Be extremely careful when searching for and downloading necessary programs from the Internet.
- Do not click on advertising links on the search page.
- Use ad blockers
- Use a trusted antimalware program
Following these rules will minimize the chances of compromising personal computers and workstations, or corporate devices.