The operators of the ransomware BlackCat (aka ALPHV) have published screenshots of Western Digital’s internal emails and video conferences. The hackers appear to have maintained access to the company’s systems even after Western Digital discovered and responded to the attack.
Let me also remind you that we wrote that BlackCat Says It Attacked Creos Luxembourg, European Gas Pipeline Operator, and also that Experts linked BlackCat (ALPHV) ransomware to BlackMatter and DarkSide groups.
Western Digital was hacked at the end of March 2023. Then the attackers compromised the internal network and stole the company’s data. At the same time, ransomware was not deployed on the Western Digital network, and the files were not encrypted.
As a result of this attack, the company’s cloud services, including Cloud, My Cloud Home, My Cloud Home Duo, My Cloud OS 5, SanDisk ibi and SanDisk Ixpand Wireless Charger, as well as mobile, desktop and web applications related to them, did not work for almost two weeks.
Let me remind you that the media wrote that Western Digital My Cloud OS Fixes Critical Vulnerability.
The fact that the incident is most likely related to a ransomware attack was first reported by TechCrunch. According to journalists, the attackers managed to steal about 10 TB of data from the company. The hackers shared samples of stolen data with TechCrunch, including files signed with stolen Western Digital keys, company phone numbers not publicly available, and screenshots of other internal data.

The first statement of hackers about the attack on WD
Although the attackers then claimed that they were not associated with the ALPHV group, soon a message appeared on the hack group’s website that Western Digital’s data would be published in the public domain if the company did not pay the ransom.
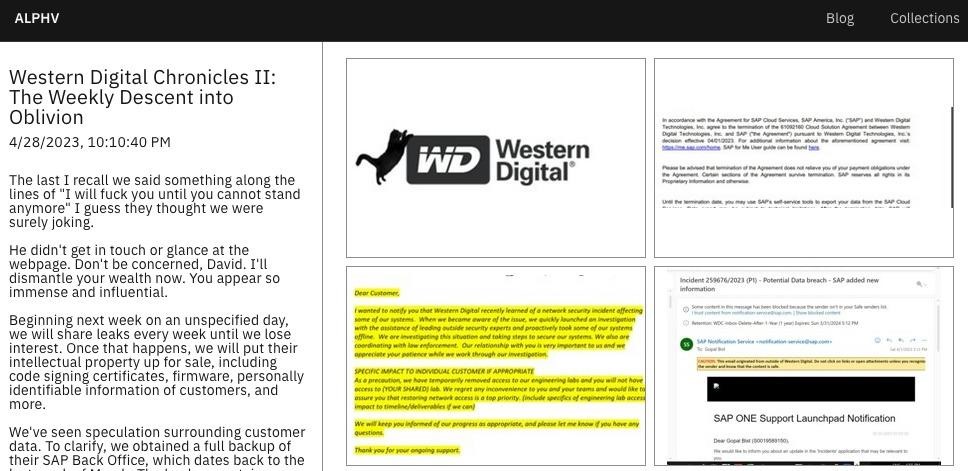
As information security researcher Dominic Alvieri now reports, in an effort to put pressure on the affected company, the hackers released 29 screenshots containing emails, documents and video conferences related to Western Digital’s response to this attack. In this way, the attackers hinted that they retained access to some Western Digital systems even after the hack was discovered (probably until April 1, 2023).
So, one screenshot includes a “media holding statement”, and the other is a letter about employees who “leak” information about the attack to journalists.
A new message from the attackers is also attached to this drain, in which they claim that they have personal information of the company’s customers and a full backup of SAP Backoffice.
The hackers say that if Western Digital does not pay the ransom, they will release the stolen files every week. They also threaten to sell the company’s stolen intellectual property on the black market, including firmware, code-signing certificates, and customers’ personal information.




