Dutch company Tesorion has released a free decryptor for data affected by Lorenz ransomware attacks.
Now some files can be recovered for free, without paying the ransom.
Rijnders said the decrypter is not universal and will work only “in some cases.” However, this is more of a chance than many Lorenz victims have at recovering their files without paying hundreds of thousands of US dollars to the Lorenz gang.
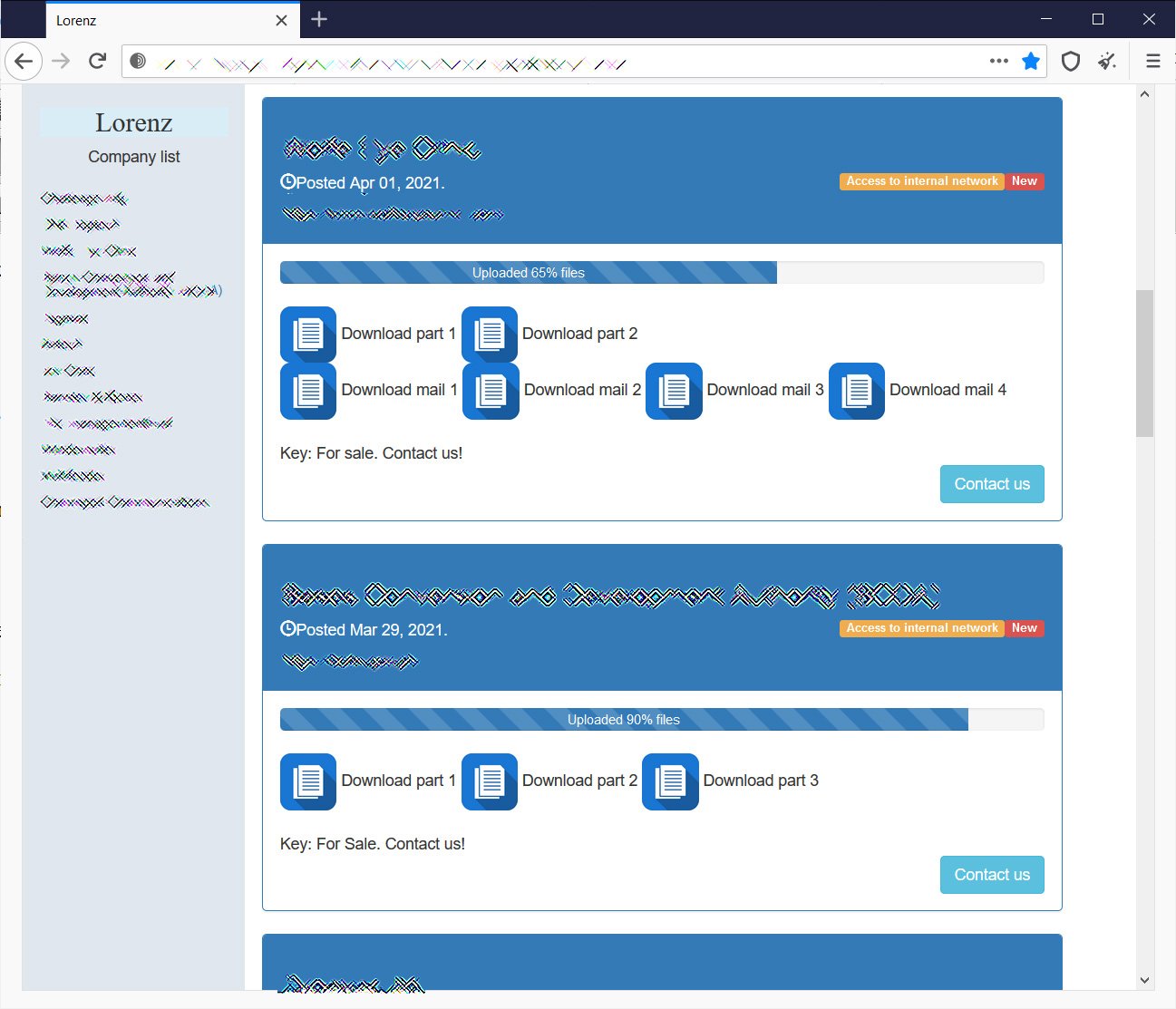
Lorenz ransomware has been “operational” since April 2021 and attacked only corporate targets. During this time, on the website of its operators was published the data of twelve victims, whose information was stolen by hackers.
According to cybersecurity researchers, the ransomware code is based on the code of the old ThunderCrypt and SZ40 malware families.
The decoder created by Tesorion can be downloaded from the NoMoreRansome website. Unlike other similar tools that usually work with the actual decryption key, this decryptor works differently and will only help you recover certain types of files.
In particular, it is possible to decrypt files with well-known structure, including Office documents, PDF files, and some types of images and movies. Unfortunately, Tesorion will not cope with files of unknown types or with an unusual structure.
The researchers also published information on the encryption technique that Lorenz uses.
The company’s blog says that an error was discovered in the hackers’ code that could lead to data loss and prevent files decryption, even if a ransom was paid to the attackers.
Let me remind you that I also talked about the fact that FonixCrypter ransomware stopped working and published a key to decrypt data.