The FBI and NSA claim that a group of Russian government hackers are brute-forcing companies and organizations around the world.
The NSA, the Department of Homeland Security (DHS CISA), Cybersecurity and Infrastructure Protection Agency, the FBI and the UK National Cybersecurity Center (NCSC) issued a joint statement warning that the Russian “government hack group from APT28 (aka Fancy Bear, Pawn Storm, Sednit, Strontium) actively brute-force the resources of public and private companies and organizations around the world.
If the brute-force was successful, the APT28 hackers used the compromised accounts to move laterally within the affected organizations’ networks. Specifically, the agencies say APT28 used compromised credentials along with various exploits for vulnerabilities in Microsoft Exchange, including RCE issues CVE-2020-0688 and CVE-2020-17144, combining them to gain access to internal mail servers.
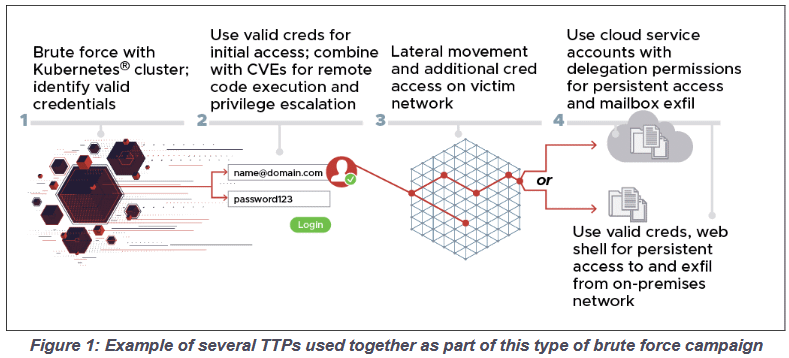
These attacks reportedly went largely unnoticed as APT28 masked brute-force attacks via Tor or commercial VPN services including CactusVPN, IPVanish, NordVPN, ProtonVPN, Surfshark, and WorldVPN, and used Kubernetes clusters. Typically, brute-force was performed using a variety of protocols, including HTTP (S), IMAP (S), POP3, and NTLM, so attacks did not always go through the same channels.
The NSA states that between November 2020 and March 2021, hackers carried out attacks without using anonymization services, and as a result, the following IP addresses were identified:
- 158.58.173[.]40
- 185.141.63[.]47
- 185.233.185[.]21
- 188.214.30[.]76
- 195.154.250[.]89
- 93.115.28[.]161
- 95.141.36[.]180
- 77.83.247[.]81
- 192.145.125[.]42
- 193.29.187[.]60
APT28 attacks allegedly targeted cloud resources for a wide range of targets, including government organizations, think tanks, defense contractors, energy, logistics, legal companies, and so on.
Law enforcement officers do not disclose details about the victims.
Let me remind you that I also talked that NATO experimented with deceptive techniques to combat Russian hackers.




