AstraLocker ransomware operators have announced that the malware is ending its work and have uploaded data decryption tools to VirusTotal. The hackers say that they do not plan to return to ransomware in the future, but intend to switch to cryptojacking.
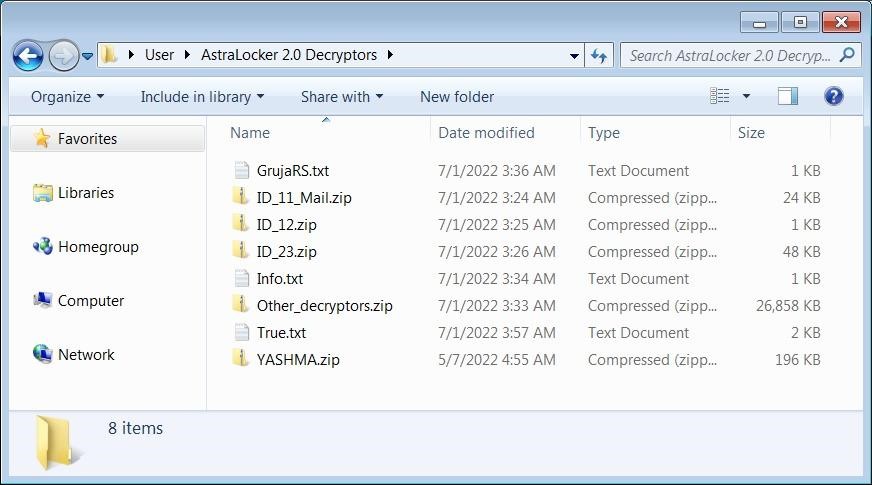
The Bleeping Computer reports that it has already studied the archive published by the attackers and confirms that the decryptors are real and really help to decrypt the affected files.
Let me remind you that we also said that Free decryptor for BlackByte ransomware was published, and also that Cybersecurity specialists released a free decryptor for Lorenz ransomware.
Journalists note that they tested only one decryptor, which successfully decrypted files blocked during one of the AstraLocker campaigns. The other decryptors in the archive are apparently designed to decrypt files damaged during previous campaigns.
Archive content
The journalists also managed to get a comment from one of the malware operators:
Although the malware developer did not say why AstraLocker suddenly stopped working, journalists believe that this may be due to recently published reports by security experts who studied the malware. This could bring AstraLocker to the attention of law enforcement.
Emsisoft, a company that helps ransomware victims recover data, is currently developing a universal decryptor for AstraLocker, which should be released in the near future.
What will we no longer see in the criminal world?
Threat intelligence firm ReversingLabs recently reported that AstraLocker used a somewhat unusual method of encrypting its victims’ devices compared to other strains of ransomware.
Instead of first compromising the device (hacking it or buying access from other attackers), the AstraLocker operator will directly deploy the payload from email attachments using malicious Microsoft Word documents.
The honeypots used in the AstroLocker attacks are documents that hide an OLE object with a ransomware payload that will be deployed after the target clicks “Run” in the warning dialog displayed when the document is opened.
Before encrypting files on a compromised device, the ransomware will check to see if it is running on a virtual machine, terminate processes, and stop backup and antivirus services that could interfere with the encryption process.
Based on analysis by ReversingLabs, AstraLocker is based on the leaked source code of Babuk Locker (Babyk) ransomware, a buggy yet still dangerous strain that came out in September 2021.
Also, one of the Monero wallet addresses in the AstraLocker ransom note was also linked to the operators of the Chaos ransomware.




