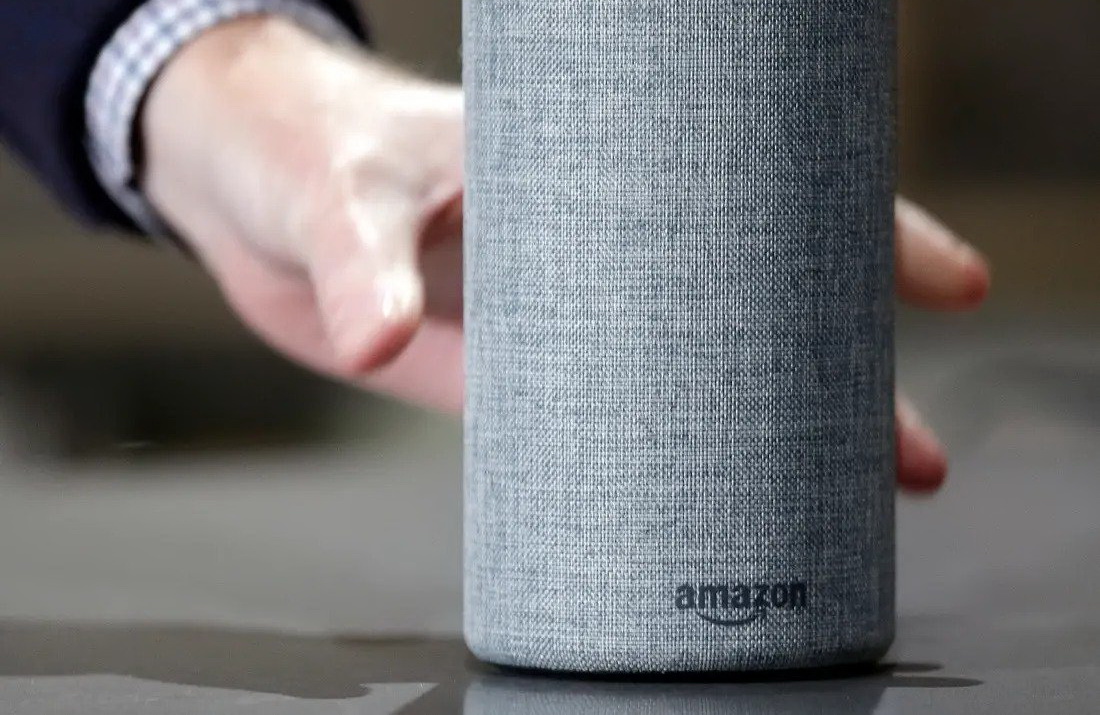
In June this year, researchers from Check Point discovered a number of dangerous vulnerabilities that opened for attacks the Amazon Alexa virtual assistant and its users.
The problem was in CORS and XSS bugs, which affected several Amazon subdomains, and in configuration issues.
By exploiting these bugs, attackers could gain access to personal data (usernames, phone numbers, home addresses, voice history) and perform various actions on behalf of victims (for example, delete and install Alexa skills).
“It took just one click on a link, specially created by an attacker, to successfully exploit [the problems]”, — write the researchers.
For successful attack, the attacker needed only to create a malicious link that would direct the user to amazon.com and send it to the victim (by somehow forcing the user to click on it).
The researchers suggested using the vulnerable track.amazon.com for these purposes – this page is not associated with Alexa, but is used to track parcels from Amazon, and previously it could have been injected with malicious code.
Next, the attacker sent an Ajax-request with the user’s cookies received to amazon.com/app/secure/your-skills-page, which allowed him to get a list of the skills installed for this Alexa account.
The response to such a request also contained a CSRF token, which an attacker could use to remove one skill from the list. The attacker could then install his own malicious Alexa skill on the device in the same way. Replacing a remote skill with his own opened up many opportunities for the criminal, depending on the skills installed on the user’s device.
For example, it was possible to access the victim’s voice history, and then usernames, phone numbers, home addresses, banking data (Alexa does not record banking login credentials, but records other interactions).
“Smart speakers and virtual assistants seem so unremarkable that, at times, we lose sight of their role in managing a smart home, as well as how much personal data they store. For this reason, hackers view these applications as entry points into people’s lives, through which they can access personal data, eavesdrop on conversations and perform other malicious activities without the user’s knowledge”, — says Oded Vanunu, head of the vulnerabilities research department at Check Point Software Technologies.
Currently, Amazon engineers have already patched all discovered vulnerabilities. Additionally, company representatives stated that they were not aware of any use of these problems or disclosure of any information about customers.
We have already many times talked about vulnerabilities in IoT devices, for example, that Kr00k problem threatens devices with Qualcomm and MediaTek Wi-Fi chips. The Internet of Things is becoming a part of everyday life and it is full of new dangers.