Microsoft has developed an open source SimuLand lab environment to help testing and improving Microsoft 365, Defender, Azure, and Azure Sentinel protection against a variety of cyberattack scenarios.
SimuLand enables “resources from a variety of data sources, including telemetry from Microsoft 365 Defender security products, Azure Defender, and other integrated sources through Azure Sentinel Data Connectors.”
Simuland will be working under the following basic principles:
- Understand the underlying behavior and functionality of adversary tradecraft.
- Identify mitigations and attacker paths by documenting preconditions for each attacker action.
- Expedite the design and deployment of threat research lab environments.
- Stay up to date with the latest techniques and tools used by real threat actors.
- Identify, document, and share relevant data sources to model and detect adversary actions.
- Validate and tune detection capabilities.
SimuLab is designed to analyze the behavior of cybercriminals, define defenses, accelerate the development and launch of laboratory environments for threat research, inform about the latest technologies and hacker tools, and identify, document, and share relevant data sources for modeling and detecting criminals.
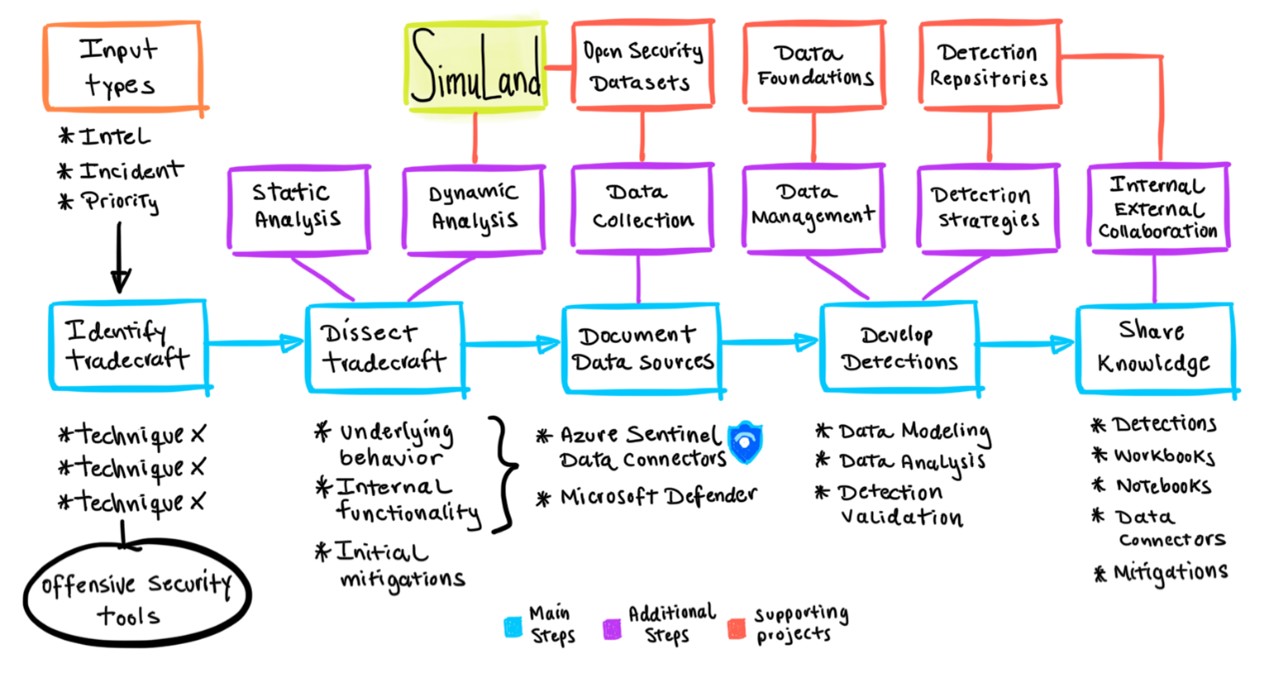
Microsoft aims to integrate SimuLand with threat research methodologies that apply dynamic analysis to end-to-end modeling scenarios.
The image below shows where SimuLand would fit.
Currently, the only open lab environment allows researchers to test and improve protection against Golden SAML attacks, in which attackers forge authentication for cloud applications.
Besides working on adding additional scripts, Microsoft also intends to add attack automation through the Azure Functions service in the cloud, telemetry export and exchange, integration of Microsoft Defender evaluation labs, and infrastructure installation and maintenance using CI/CD with Azure DevOps.
Let me remind you that I talked about the fact that Microsoft warns of the growing number of cyberattacks using web shells.




