Microsoft fixed more than 120 vulnerabilities this month, including the DogWalk bug, as part of the traditional “Update Tuesday”.
Indeed, one of the most serious issues in the package was the DogWalk zero-day vulnerability (CVE-2022-34713, CVSS score 7.8), which leads to arbitrary code remote execution and is already under attack.
In total, 121 vulnerabilities were fixed in August, 17 of which received critical status because they allow remote code execution or privilege escalation.
Let me remind you that we also wrote that Microsoft Has Already Patched a Vulnerability in Windows RDP Twice, and also that Microsoft Fixed Follina Vulnerability and 55 Other Bugs.
DogWalk
The most serious among the fixed problems is definitely the CVE-2022-34713 vulnerability, which the researchers named DogWalk. This bug is associated with the Microsoft Windows Support Diagnostic Tool (MSDT) and is already being used by attackers who trick users into opening specially crafted files, which eventually leads to code execution. The issue affects all supported versions of Windows, including the latest versions of Windows 11 and Windows Server 2022.

Interestingly, the CVE-2022-34713 bug was originally found back in January 2020 by the information security specialist Imre Rad, but then Microsoft reported that the bug found was not a security issue.
Recently, this bug was discovered again, and this time it was reported by an expert known as j00sean. Then an unofficial patch appeared for the bug, and the company finally decided to pay attention to what was happening.
Now, Microsoft emphasizes that although unauthenticated attackers can exploit this vulnerability, user interaction is still required for a successful attack: you need to force the victim to open a malicious attachment from an email or click on a link to download and run a malicious file.
If the attack is successful, the attacker will be able to install programs, view, change or delete data, and create new accounts in the context of the current user.
Exchange
It is also worth noting that another 0-day vulnerability was fixed as part of this “update Tuesday”, but it has not yet been exploited by hackers. We are talking about the issue CVE-2022-30134 (7.6 points on the CVSS scale), which is associated with information disclosure in Microsoft Exchange and which allows attackers to read other people’s emails.
At the same time, Microsoft engineers explain that some of the bugs in Exchange fixed this month will require more than just patching. Administrators will also have to manually enable Extended Protection (EP) on vulnerable servers, which extends Windows Server authentication and protects against man-in-the-middle and authentication relay attacks.
Such action would have to be taken due to issues CVE-2022-21980, CVE-2022-24477, and CVE-2022-24516, which can be used to escalate privileges if a user can be tricked into visiting a malicious server (using phishing emails or messages).
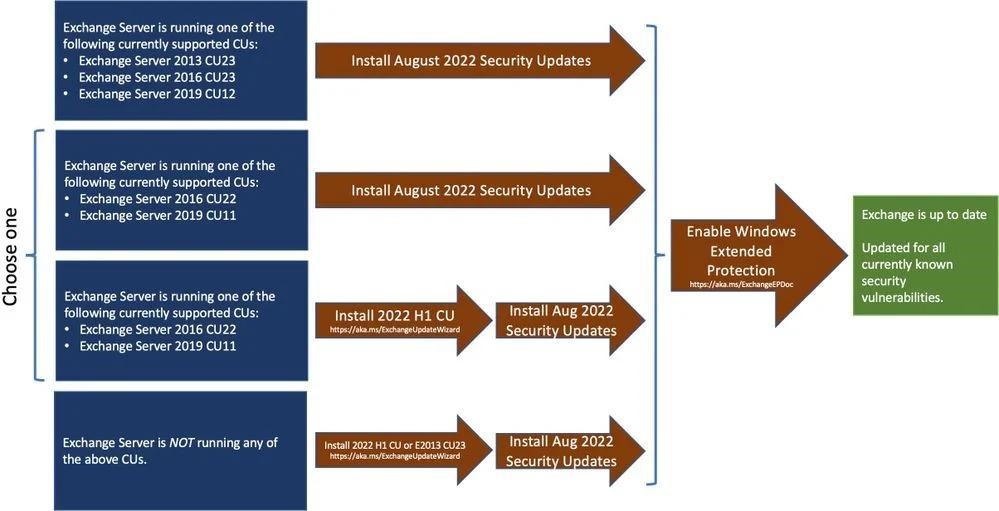
To include the EP, the company provided a special script. However, before activating it, administrators are advised to carefully evaluate their environment and study the potential problems mentioned in the documentation.
Other
Two other critical issues related to remote code execution in the Windows Point-to-Point Protocol, CVE-2022-30133 and CVE-2022-35744, received a CVSS score of 9.8 out of 10. However, Microsoft assures that they can only be used when exchanging data through port 1723. That is, even a simple blocking of traffic through this port is suitable as a temporary protection measure.
It must also be said that not only Microsoft has released updates for its products. So, in August 2022, other important patches were released, including fixes for many Cisco, SAP and VMware products, as well as August updates for Android and Adobe patches that close RCE vulnerabilities in Acrobat and Reader.




