The Security Blog From Gridinsoft
Fake Sites for Adults Destroy User Data
Experts from the Cyble company have discovered a number of fake adult sites that distribute ransomware. However, a detailed analysis…
Meta Finds over 400 Chinese Apps That Stole Data from 1 million Users
Meta has sued several Chinese companies (including HeyMods, Highlight Mobi and HeyWhatsApp) for developing and using “unofficial” WhatsApp apps for…
Hacker Group XDSpy Distributes Malware in Russia under the Guise of Subpoenas for the Army
In early October, Kaspersky Lab experts recorded a targeted attack on Russian organizations: attackers from the XDSpy hacker group sent…
Hundreds of Microsoft SQL Servers Infected with Maggie Backdoor
Security researchers have discovered a new malware that targets Microsoft SQL servers. The backdoor is dubbed Maggie, has already infected…
Ferrari Has So Far Denied If It Attacked by Ransomware
Sports and racing car maker Ferrari persistently denies it was ransacked. At the same time, the RansomEXX hack group added…
Microsoft stopped RDCMan development due to a bug
Microsoft has stopped development of the Remote Desktop Connection Manager…
Two new malware can steal cookies from Android apps
IS experts discovered two new malware for Android (recognized as…
Modern RAM is still vulnerable to Rowhammer attacks
Recently, I wrote all about the vulnerabilities of Intel and…
Intel processors need hardware fixes due to new LVI attack
Security experts discovered a new attack on Intel processors called…
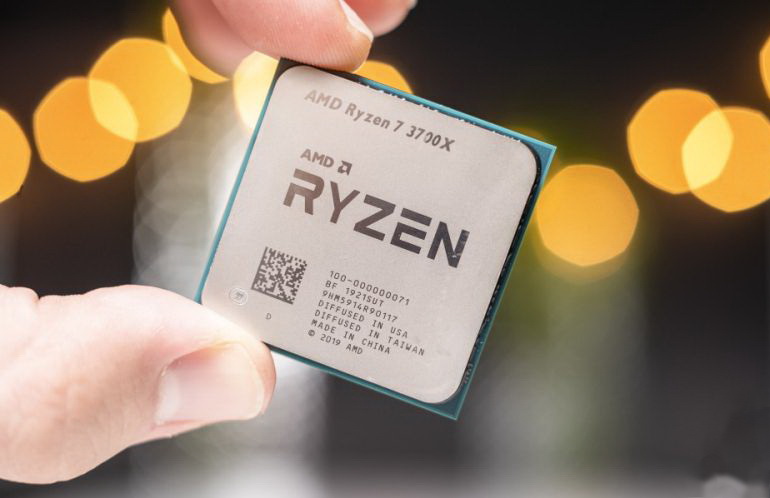
Information security experts said that AMD processors are vulnerable to two attacks
A joint group of specialists from the National Center for…
More than 40% of Android users are at risk of cyberattacks
According to a study by Which company, more than 40%…
Researchers found about 700 problematic Microsoft subdomains
Vullnerability researchers found about 700 problematic Microsoft subdomains and captured…
Malicious Ledger Live extension for Chrome steals Ledger wallet data
Harry Denley, Director of Security in MyCrypto discovered the malicious…
Chinese coronavirus detection app transmits data to the police
Last month, Chinese authorities released the Alipay Health Code coronavirus…
Cyberattack with the use of ransomware forced Epiq Global to shut down its systems
Epiq Global, a large international law firm, has become the…
Vulnerability in OAuth Protocol Allows Hacking Any Facebook Account
The vulnerability is contained in the Facebook login feature, which…
Hackers scan network for vulnerable Microsoft Exchange servers
Information security experts warn that hackers are already scanning the…