The Security Blog From Gridinsoft
Hot Topic Data Breach Exposes of 350 Million Customers
Data breach of a known US retailer Hot Topic leaks a selection of personally identifiable information of 350 million chain’s…
Roundcube Webmail Vulnerability Exploited in Real-World Attacks
Vulnerability in Roundcube Webmail service appears to be exploited in real-world attacks. The flaw that falls under designation of stored…
Kaspersky Returns with UltraAV and UltraVPN: Are They Safe?
Kaspersky, an infamous Russian antivirus brand, is now back on the US market with its off-branded software, UltraAV antivirus and…
Spring Framework Vulnerability Leads to Data Leaks, Fix Now
Spring Framework has released an update that fixes the CVE-2024-38819 vulnerability, which potentially enables attackers to exploit HTTP requests for…
USDoD Hacker Arrested by Federal Police of Brazil
A hacker known under the moniker USDoD was arrested in Brazil on October 16, 2024. The Federal Police of Brazil…
Tortilla (Babuk) Ransomware Decryptor Available
On January 9, 2024, Avast and Cisco Talos announced the…
OAuth2 Session Hijack Vulnerability: Details Uncovered
A sophisticated exploit targeting Google’s OAuth2 authentication system was uncovered…
xDedic Marketplace Members Detained In International Operations
The infamous xDedic Marketplace, known for its illicit trade in…
Verified X/Twitter Accounts Hacked to Spread Cryptoscams
The trend of hacking official accounts to promote cryptocurrency fraud…
SMTP Smuggling is a New Threat to Email Security
A new SMTP Smuggling technique reportedly has the potential to…
Mandiant Account in X Hacked to Spread Cryptocurrency Scams
The Twitter account of Google’s Mandiant cybersecurity service has been…
Qualcomm RCE Vulnerabilities Expose Millions of Users
Vulnerability in several Qualcomm chipsets allows for remote code execution…
Black Basta Ransomware Free Decryptor Available
SRLabs researchers published a free decryptor for BlackBasta ransomware. They…
Seven Common Types of Malware – Analysis & Description
In the intricate landscape of cybersecurity, comprehending the various forms…
DLL Search Order Hijacking Technique Bypasses Protection
A new DLL (Dynamic Link Library) Search Order Hijacking variant…
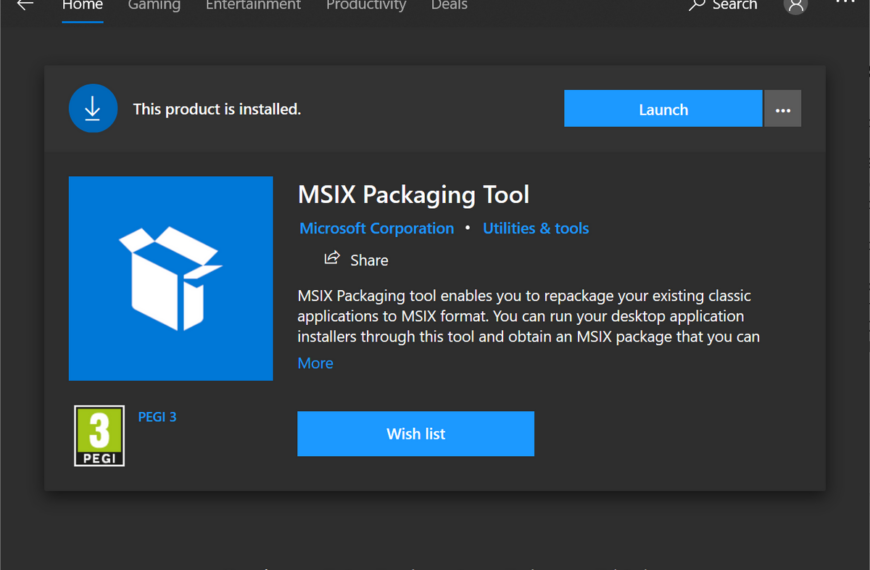
Microsoft Disables MSIX App Installer Protocol
Microsoft reportedly disabled MSIX installer protocol in Windows, due to…
Novice Rugmi Loader Delivers Various Spyware
The threat landscape meets a new player – Rugmi Loader.…