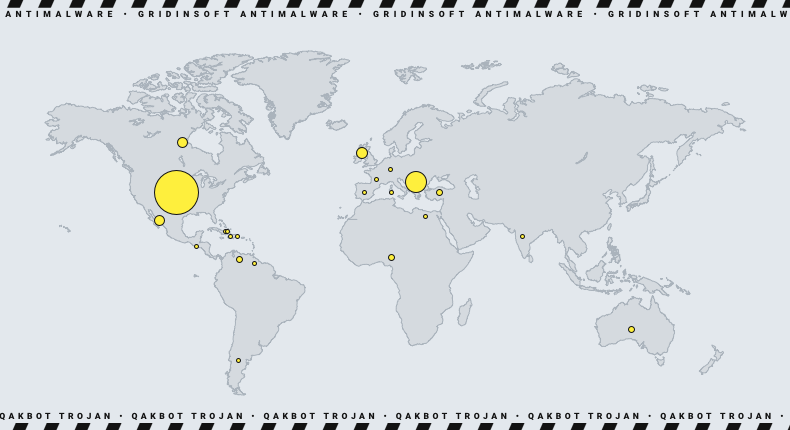
Qakbot, a notorious botnet, has been taken down by a multinational law enforcement operation spearheaded by the FBI, Operation “Duck Hunt”. The botnet, also called Qbot and Pinkslipbot, that considered one of the largest and longest-running botnets to date. According to conservative estimates, law enforcement officials have linked Qakbot to at least 40 ransomware attacks. These attacks targeted companies, healthcare providers, and government agencies worldwide, causing damages of hundreds of millions of dollars. Over the past 18 months, the losses due to these attacks have exceeded 58 million dollars.
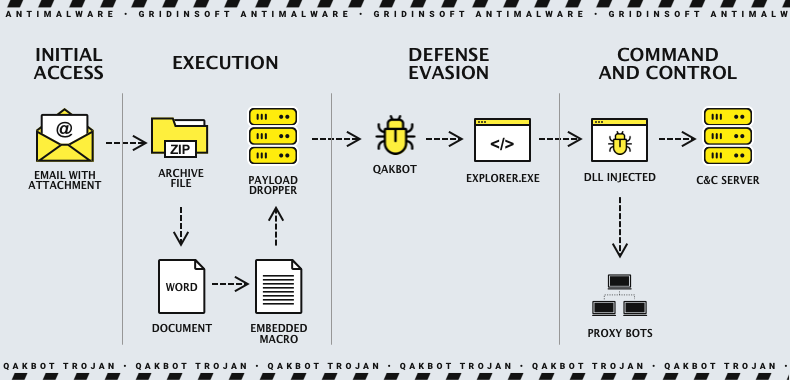
Qakbot has been known to deploy multiple types of malware, trojans, and highly destructive ransomware variants. They also used their affiliates or operators, which include Conti, ProLock, Egregor, REvil, RansomExx, MegaCortex, and most recently, Black Basta. It targets the United States and other global infrastructures, including the Election Infrastructure Subsector, Financial Services, Emergency Services, and Commercial Facilities Sectors.
How has the Qakbot botnet been detected?
The FBI found a number of files related to the operation of the Qakbot botnet on a computer used by one of its administrators. These files included chats between the Qakbot administrators and co-conspirators. Also a directory containing several files that held information related to virtual currency wallets, according to court documents, that included a computer used by one of its admins after it had infected over 700,000 computers, with over 200,000 in the United States.
While searching through the same computer, a separate file called 'payments.txt' was discovered. It contained a list of individuals who had fallen victim to ransomware. It also included information about the ransomware group, details about their computer systems, dates of the attacks, and the amount of BTC paid to the Qakbot administrators in connection with the attacks.
The agency redirected Qakbot traffic to its servers, giving the FBI the access they needed to remove the malware from compromised devices worldwide. This prevented the deployment of any additional malicious payloads.
Victims were not informed when the uninstaller was executed to remove the malware from their systems. Still, the FBI contacted them using IP addresses and routing information collected from their computers during removal.
Recommendations
Organizations must implement the recommendations provided in the joint CSA by CISA and FBI. This will help to lower the risk of QakBot-related activity and make it easier to detect QakBot-facilitated ransomware and malware infections. If you come across any incidents or anomalous activity, please feel free to contact any of the following organizations without any delay:
- CISA, either through the agency’s online tool (cisa.gov/report) or the 24/7 Operations Center or (888) 282-0870.
- FBI via a local field office.
How to prevent botnet attacks?
Using anti-malware software is an important measure to protect your computer from online threats. Cybercriminals can use malware to steal your private information, monitor your online activity, or take over your computer and use it as a botnet. However, dependable anti-malware software can detect and remove malware before it can harm your system. To be proactive in safeguarding your computer, it’s need to regularly update your anti-malware software and carry out full system scans. It’s also crucial to keep your operating system and other software up to date, as software updates often provide security patches that address known vulnerabilities.




How to haking