Mobile Security
Vulnerability in Apple iCloud puts billion users at risk
Security of over a billion iPhone owners and users of popular instant messengers is at risk due to a vulnerability…
Unofficial fixes released for 0-day issue in Windows Mobile Device Management Service
Unofficial fixes released for 0-day issue in Windows Mobile Device Management Service Access to Work or School. The problem is…
Ukrainian law enforcement officers arrested members of the hacker group Phoenix
The Security Service of Ukraine (SBU) announced the arrest of five members of the international hacker group Phoenix, which specializes…
NUCLEUS: 13 Problems Threat to Medical Devices, Automobiles and Industrial Systems
Forescout and Medigate Labs issued a report on NUCLEUS:13 problems – A Set of 13 vulnerabilities which affect Siemens Software…
Expert hacked 70% of Wi-Fi networks in Tel Aviv for research
CyberArk specialist Ido Hoorvitch hacked 70% of Wi-Fi networks in his native Tel Aviv, seeking to prove that home networks…
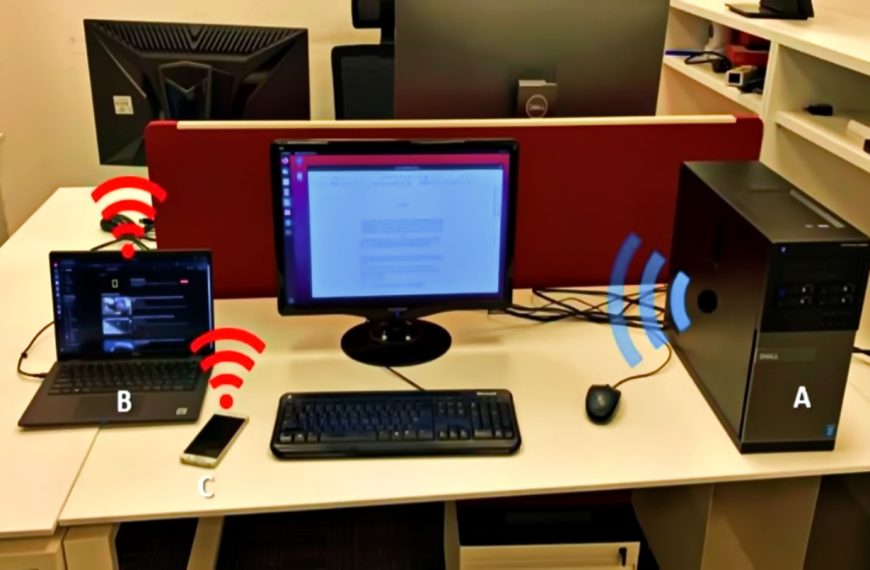
AIR-FI attack turns RAM into a makeshift Wi-Fi signal source
Experts from Israel’s Ben-Gurion University have demonstrated the AIR-FI attack,…
SolarWinds was hacked because its credentials were publicly available on GitHub
Earlier this week was reported a massive attack on the…
Heavy ad blocker started working in the Google Chrome
Earlier this year, Google Chrome developers announced about adding of…
5G and it’s possible effect on our lives
5G networks are declared as an amazing technology that can…
Cybercriminals started using Google services more often in phishing campaigns
Security researchers have reported an increase in cyberattacks using Google…
Microsoft urges users to opt out of multi-factor authentication via phone
Microsoft experts have once again raised the issue of the…
Platypus attack allows stealing data from Intel processors
A group of scientists from the Technical University of Graz…
MalLocker ransomware easily tricks Russians, pretending to be a screen lock from the police
Microsoft experts talked about the new Android ransomware AndroidOS/MalLocker. (hereinafter…
Cellmate men’s chastity belts are vulnerable to attacks and dangerous for users
Pen Test Partners analysts have studied an extremely unusual device:…
Google recruits a team of experts to find bugs in Android applications
ZDNet reports that a number of new positions have been…
Attackers can bypass TikTok multi-factor authentication through the site
Journalists of the ZDNet publication, citing one of their readers,…
Microsoft left open one of the internal servers of the search engine Bing
Ata Hakcil, cyber security specialist at WizCase, discovered that Microsoft…