Emotet malware operators have fixed a bug due to which, after opening a malicious document the system was not infected, and launched a phishing campaign again.
Let me remind you, by the way, that at the end of last year we wrote that Microsoft patches Windows AppX Installer vulnerability that spreads Emotet malware.
Emotet’s main vector of distribution is spam emails with malicious attachments. When a victim opens a malicious document, malicious macros or scripts are loaded onto their system with the Emotet DLL.
Once downloaded, the malware looks for and steals email addresses for use in future phishing campaigns and downloads additional payloads like Cobalt Strike or other malware, including ransomware.
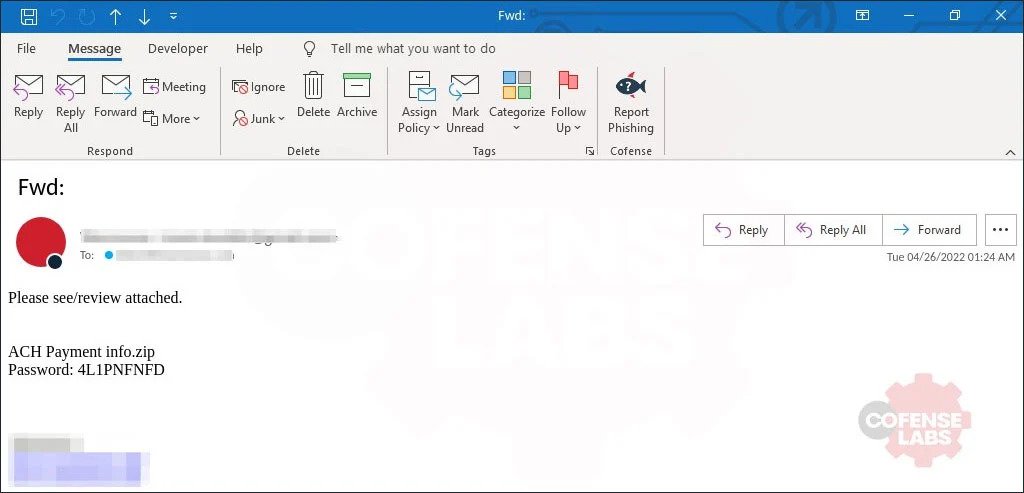
On Friday, April 22, Emotet operators launched a new spam operation with a password-protected ZIP file attached. It contained a Windows LNK (Quick Access Link) file disguised as a Word document.
After double-clicking on the shortcut link, a search command was executed in the file for a special string with Visual Basic Script code. This code was then added to a new VBS file that ran on the system.
As Cryptolaemus researcher Joseph Roosen told BleepingComptuer, Emotet operators stopped the new operation on Friday night when they discovered that the system was not infected due to a bug. However, they quickly fixed the bug and started spamming again on Monday.
This time, the shortcut link contains the actual file name, the command is executed, and the VBS file is created as expected. Emotet is freely loaded and executed on the attacked system.




