BlackBerry experts told about the discovery of a group of mercenary hackers called CostaRicto.
This is the fifth group of mercenary hackers identified by experts this year. So, back in the spring, Google Threat Analysis Group experts warned that the number of such groups is growing, and earlier this year, information security specialists have already talked about hired hackers BellTrox (aka Dark Basin), DeathStalker (aka Deceptikons), Bahamut and an unnamed hacker team.
Interestingly, many groups of this kind ended up being associated with India: BellTrox was connected with an Indian company and Bahamut is also suspected of similar connections. In this regard, the BlackBerry report specifically emphasizes that the origin and location of CostaRicto is still unknown.
But experts found that hackers organized attacks around the world, including in different countries of Europe, America, Asia, Australia and Africa. BlackBerry says that South Asia (especially India, Bangladesh and Singapore) is hardest hit by CostaRicto.
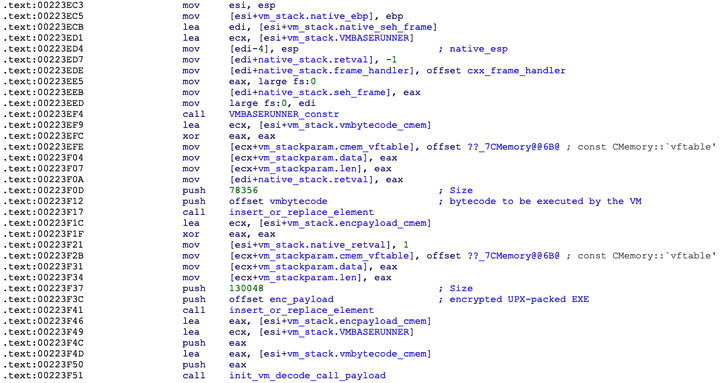
The BlackBerry report states that the CostaRicto group mainly uses specially designed and previously unknown malware, but at the same time does not use any innovative attack methods in its operations. For example, most of their group attacks revolve around stolen credentials or common spear phishing.
These malicious emails usually contain a backdoor Trojan that BlackBerry monitors as Sombra or SombRAT.
This Trojan provides CostaRicto operators with access to infected hosts, helps to detect confidential files on them and steal important documents. The stolen data is usually transmitted to the hacker’s control server, which is hosted on the darknet and is accessible only through Tor. In addition, infected hosts usually connect to attackers’ servers through multiple proxies and SSH tunnels to hide malicious traffic from prying eyes.
All of CostaRicto’s malware samples studied were dated October 2019, although other evidence found on the gang’s servers suggests that hackers may have been active since at least 2017.
The report also notes that the researchers found some similarities between CostaRicto’s attacks and previous campaigns by the Russian-speaking hack group APT28, which is associated with the Russian government. However, BlackBerry writes that this “overlap” was most likely an accident.
Let me remind you that recently Microsoft experts talked about an attack of Iranian hackers on participants of a security conference.




