Since 2020, some information security specialists have helped victims, as individuals and companies affected by the Zeppelin ransomware. The fact is that a number of vulnerabilities were found in the encryptor, which were used to create a working decryptor.
Let me remind you that we talked that Microsoft Links Hacker Group Vice Society to Several Ransomware Campaigns (including using Zeppelin malware), and also that Azov Ransomware Tries to Set Up Cybersecurity Specialists.
The publication Bleeping Computer says that the authors of this decoder were specialists from the consulting information security company Unit221b. Back in 2020, they prepared a report on vulnerabilities in the ransomware, but eventually delayed its publication so that attackers would not know about the possibility of free file decryption.
Unit221b experts decided to try to hack Zeppelin when it was discovered that malware operators were attacking charitable and non-profit organizations and even homeless shelters.
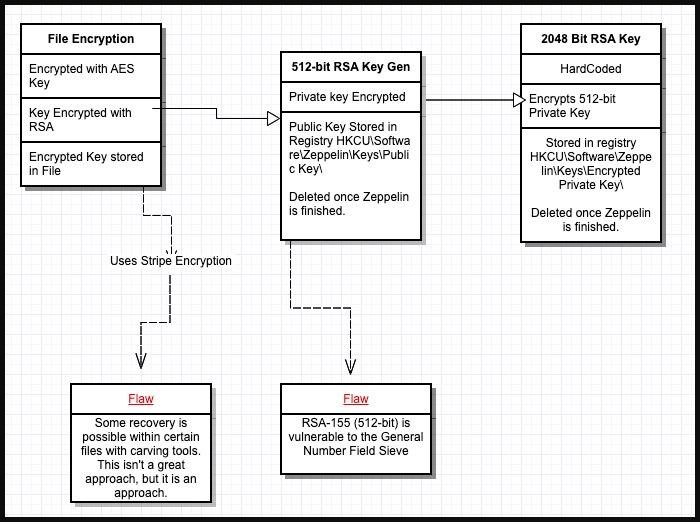
Starting with a 2019 BlackBerry Cylance report, the researchers found that Zeppelin uses an ephemeral RSA-512 key to encrypt an AES key that blocks access to encrypted data. At the same time, the AES key was stored in each encrypted file, that is, cracking the RSA-512 key would allow decrypting the data and not paying a ransom to attackers.
How Zeppelin encryption works
While working on this version, the experts found that the public key remains in the registry of the infected system for about five minutes after data encryption is completed. We managed to extract it by “cutting” it from the file system, Registration.exe memory dumps and directly from NTUSER.Dat in the /User/[user_account]/ directory.

An Obfuscated key
The resulting data was obfuscated using RC4, and to deal with this problem, the experts used the power of 800 CPUs on 20 servers (each with 40 CPUs on board), which eventually cracked the key in six hours. After that, it remained only to extract the AES key from the affected files.
Unit221b founder Lance James told reporters that the company has now decided to go public with the details of the work done, as the number of Zeppelin victims has dropped significantly in recent months. The last major campaign using this ransomware was the attacks by the Vice Society, which abandoned Zeppelin a few months ago.
According to James, the data decryption tool should work even for the latest versions of Zeppelin and will be available to all victims free of charge, upon request.
Emsisoft, who often release their own free decryptors, told reporters that the need for a lot of computing power to recover keys, unfortunately, hinders the creation of a free tool for companies.




