Confiant experts report that malicious ads have been abusing a zero-day vulnerability in WebKit browsers engine (CVE-2021-1801) since last year, and although the patches were released in early February, attacks are still ongoing. Due to this vulnerability, users were sent from trusted resources to fraudulent sites.
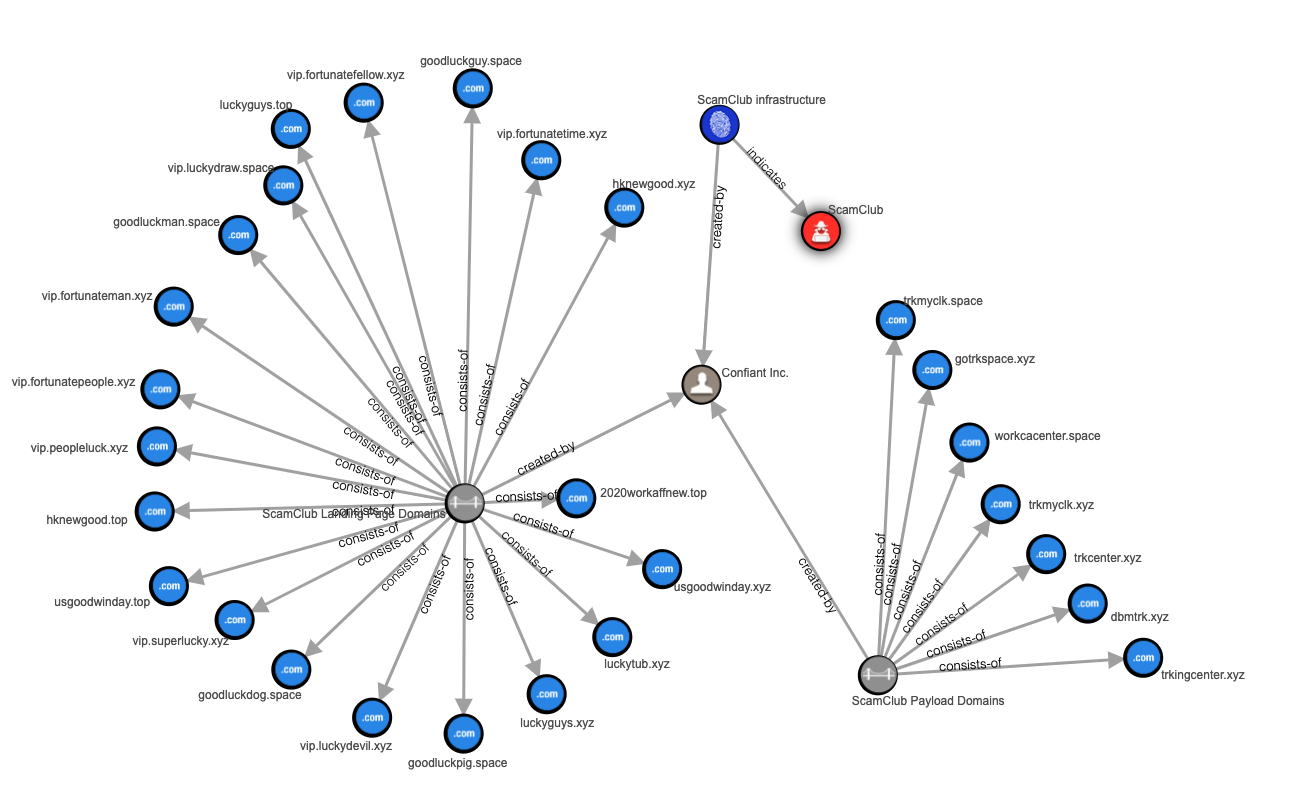
According to researchers, a hack group called ScamClub, active since 2018, is behind the attacks. As previously mentioned by experts, in general the tactics of grouping are simple: usually attackers buy a large number of ad slots on multiple platforms, hoping that at least some of the malicious ads will eventually pass security checks. Even if most of the ads are blocked, the ads that hit the post will eventually be enough for a full-scale campaign.
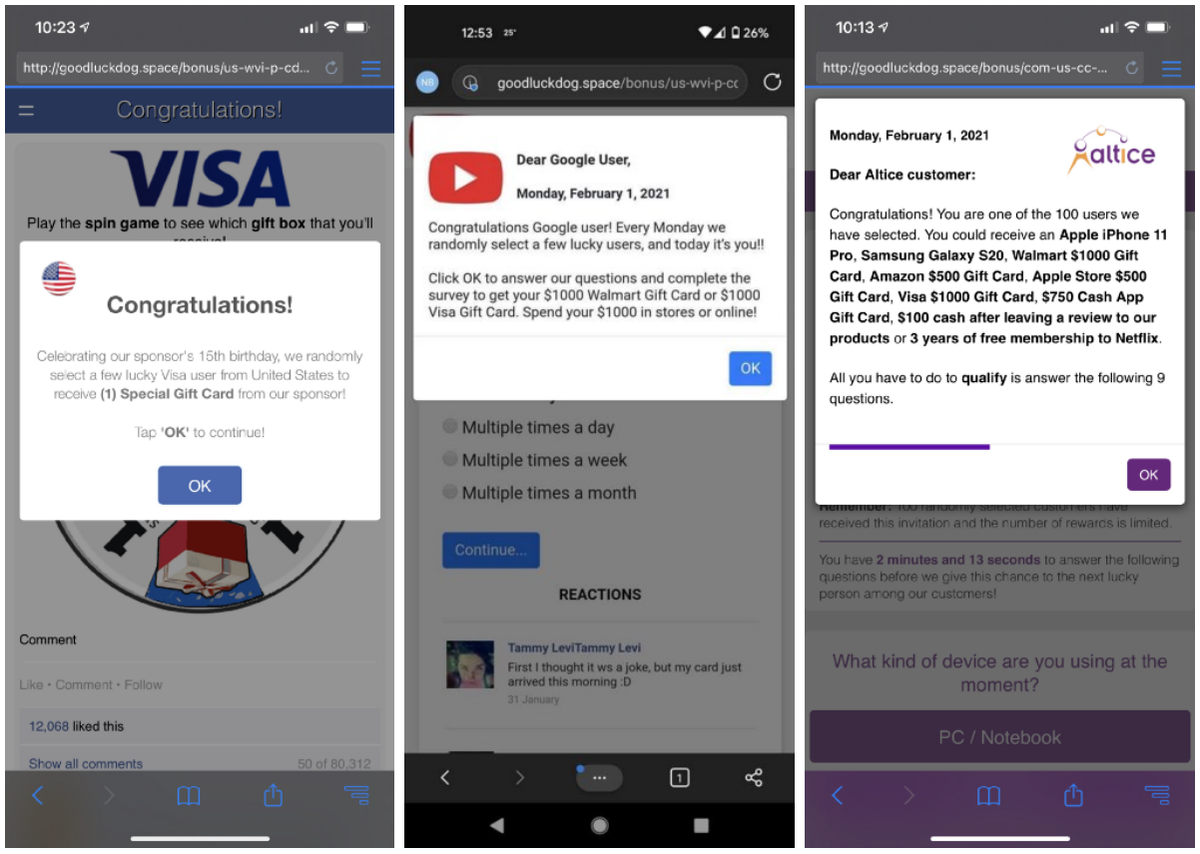
Typically, the group targets iOS users and uses malicious ads to redirect them to fraudulent sites, where they try to steal financial information from victims. Typically, users were informed that they had won a gift card from a well-known brand.
The new ScamClub operation, which started last summer, is based on the same principle, but this time the hackers exploited a vulnerability that allowed malicious code to escape the sandbox of an HTML iframe element. The root of the problem was how Webkit handles JavaScript event listeners. Since the bug was in the WebKit code, Apple Safari and Google Chrome for iOS were affected.
Although researchers notified Apple and Google of the issue last summer, the patch wasn’t released until December, and the fix only reached Safari for macOS and iOS this month.
Confiant specialists have published a list of domains where the ScamClub group hosted their fraudulent sites with fake gift cards, their addresses can be seen in the illustration below.
Let me remind you that I wrote that for iOS was discovered a new exploit, with the help of which China traced the Uyghurs.