At the USENIX conference, a group of German scientists announced the discovery of more than 40 vulnerabilities in STARTTLS implementations in popular mail clients and servers, including Apple Mail, Gmail, Mozilla Thunderbird, Claws Mail, Mutt, Evolution, Exim, Mail.ru, Samsung Email, Yandex and KMail.
Exploitation of these issues allows an attacker to steal credentials, intercept emails, and so on.
While the entire STARTTLS negotiation process was not very robust and error prone, STARTTLS came at a time when there was still no massive support for encrypted connections in mail clients and servers.
Since there were no better alternatives at the time, most users and administrators chose to enable STARTTLS as a temporary solution until TLS became more widespread.
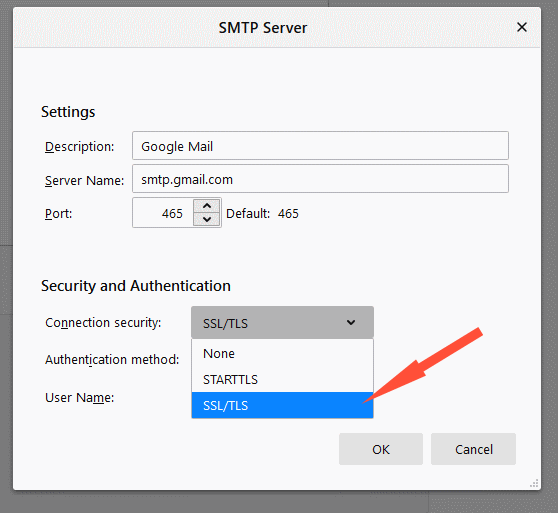
Now everything has changed: almost all mail clients and servers support TLS-only mode, in which all old protocols, including POP3, IMAP and SMTP, by default operate over an encrypted channel that protects email from hacking or eavesdropping, and mail clients refuse to send emails if a secure TLS connection cannot be established. However, there are still millions of mail clients and hundreds of thousands of mail servers where STARTTLS is supported and is still enabled.
Now experts report that they have discovered over 40 vulnerabilities in client and server implementations of STARTTLS. Problems can be abused to downgrade STARTTLS connections to plain text, intercept emails, steal passwords, and so on.
Although to implement such attacks, an attacker must first carry out a MitM attack (in order to be able to interfere with the STARTTLS negotiation process, that is, the attacker must interfere with the connection established between the mail client and the mail server, and must also have credentials to log into the account on the same server), the research team insists that “these vulnerabilities are so widespread that we recommend that you avoid using STARTTLS whenever possible.” That is, users and administrators are advised to update their clients and servers as soon as possible, and switch to using TLS-only.
Over the past few months, researchers have been actively collaborating with the developers of mail clients and servers to fix 40 bugs they discovered. Although users now can install the resulting patches and continue using STARTTLS, researchers still advise switching to TLS-only.
Let me remind you that I talked about the fact that Hackers used Firefox extension to hack Gmail.