TrickBot malware has received new features that make it more difficult to investigate and detect — for example, TrickBot has learned to crash the browser when suspicious manipulations are detected.
TrickBot is one of the most famous and “successful” malware to date. The malware was first noticed back in 2015, shortly after a series of high-profile arrests that significantly changed the composition of the Dyre hack group.
Over the years, TrickBot has evolved from a classic banking trojan designed to steal funds from bank accounts to a multifunctional dropper that spreads other threats (from miners and ransomware to infostealers).
In the fall of 2020, a large-scale operation was carried out aimed at eliminating TrickBot. It was attended by law enforcement agencies, specialists from the Microsoft Defender team, the non-profit organization FS-ISAC, as well as ESET, Lumen, NTT and Symantec.
At that time, many experts wrote that although Microsoft managed to disable the TrickBot infrastructure, most likely the botnet would “survive”, and eventually its operators would put new control servers into operation, continuing their activity. Unfortunately, that is exactly what happened. Recently, TrickBot has been linked to the resurgence of the Emotet botnet, Diavol ransomware operations, and Conti ransomware.
IBM Trusteer analysts report that TrickBot now has several new layers of protection designed to bypass antivirus products and protect against scrutiny.
The researchers write that TrickBot developers use several levels of obfuscation and base64 for scripts, including minification, string extraction and replacement, dead code injection, and so-called monkey patching. Currently, TrickBot even has too many levels of obfuscation, which makes its analysis slow and often gives unreliable results.
In addition, during the injection of malicious scripts into web pages (to steal credentials), the injections do not use local resources on the victim’s machine, but rely solely on the servers of the attackers themselves. As a result, analysts cannot extract malware samples from the memory of infected machines. At the same time, TrickBot interacts with its control servers via HTTPS, which also makes it difficult to learn.
In addition, injection requests contain parameters that mark unknown sources, i.e. researchers cannot simply get malware samples from the attackers’ control server from any endpoint.
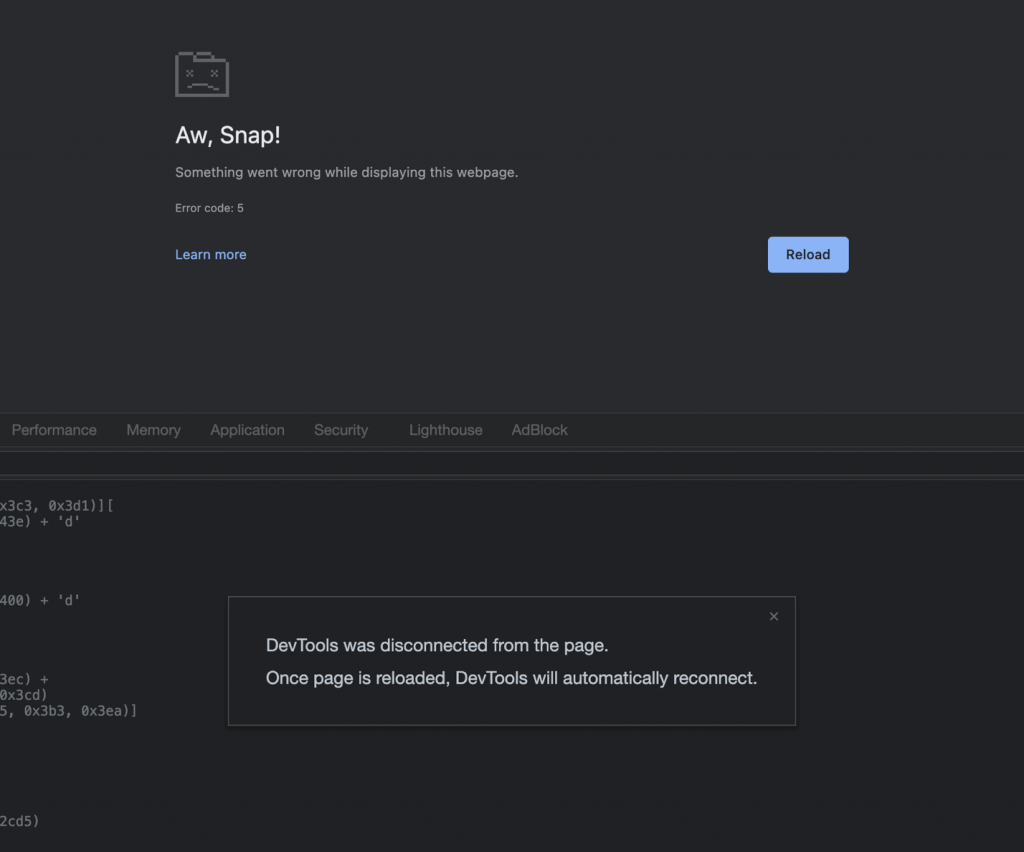
If earlier TrickBot tried to determine if it was being investigated by checking the host’s screen resolution, it now looks for signs of code beautify. This term usually refers to the transformation of obfuscated and other code into content that is easier to read by the human eye and, therefore, it is easier to find what you need in it. So, in the latest versions of TrickBot, regular expressions are used, which allow you to notice if one of the scripts has been “embellished”, because it usually indicates that the information security researcher is analyzing malware. To prevent disclosure TrickBot provokes a crash in the browser.
Let me remind you that we also reported that Microsoft patches Windows AppX Installer vulnerability that spreads Emotet malware.