Snappy Tool Helps Avoid Fraudulent Wi-Fi Hotspots
Trustwave has created a Snappy tool that will make it easy to…
What Is an Evil Twin Attack? How Does It Work?
How often do we connect to free Wi-Fi networks in public places?…
WiFi-Hacking by Neighbours is Rampant in the UK, Research Says
WiFi-Hacking by Neighbors is Rampant in the UK, Research Says The research…
Expert hacked 70% of Wi-Fi networks in Tel Aviv for research
CyberArk specialist Ido Hoorvitch hacked 70% of Wi-Fi networks in his native…
Manufacturers release patches for Frag Attacks problems
Manufacturers of various Wi-Fi-enabled equipment and software developers for this equipment release…
Any Wi-Fi enabled devices are vulnerable to Frag Attacks issues
The well-known information security expert Mathy Vanhoef reported the discovery of a…
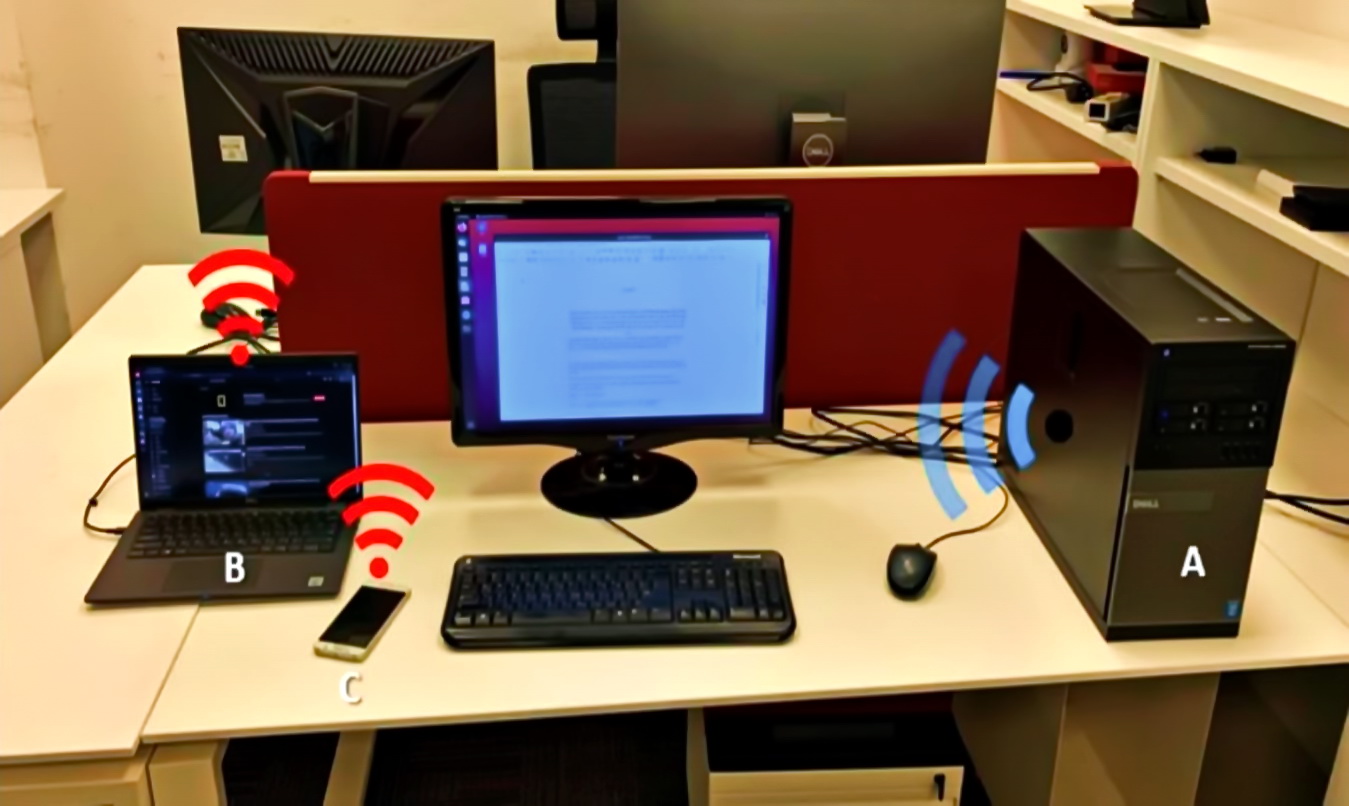
AIR-FI attack turns RAM into a makeshift Wi-Fi signal source
Experts from Israel's Ben-Gurion University have demonstrated the AIR-FI attack, which turns…
How To Use Public Wi-Fi Safely: Risks To Watch Out For
In a world where almost everything comes with a price it's sometimes…
How can hackers crack your router?
Do you think that you are protected from hackers? Of course, you…