A dangerous vulnerability called ProxyToken has been discovered in Microsoft Exchange. An attacker can exploit this problem by making requests to the Exchange Control Panel (ECP) web services and stealing messages from the victim’s mailbox.
Initially, the problem was discovered by a VNPT ISC specialist, who reported it to Trend Micro Zero-Day Initiative (ZDI) experts back in March 2021.
As I mentioned, over 2000 Exchange Servers Hacked Using ProxyShell Exploit.
ProxyToken received the identifier CVE-2021-33766 and gives unauthenticated attackers access to user mailbox settings, where they can create a mail forwarding rule. As a result, all messages will be delivered not only to the user, but also to the account controlled by the attacker.
As it turns out, the root of the problem is that the Microsoft Exchange front-end site (Outlook Web Access, Exchange Control Panel) basically acts as a proxy for the Exchange Back End to which it passes authentication requests.
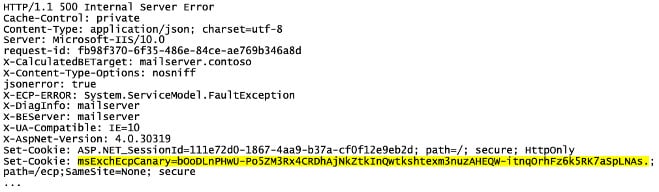
In Exchange installations where Delegated Authentication is enabled, the frontend forwards requests requiring authentication to the backend, and the backend identifies them by the presence of a SecurityToken cookie. If a non-empty SecurityToken cookie is present in the /ecp request, the frontend delegates the authentication decision to the backend.
However, the default Microsoft Exchange configuration does not load the ECP module responsible for delegating the validation process (DelegatedAuthModule) for the backend.
As a result, requests containing a non-empty cookie named SecurityToken that are redirected from the frontend to the backend are not authenticated, and responses with an HTTP 500 error expose the Exchange Control Panel canary token.
Microsoft released a patch for the ProxyToken problem back in July, and even then the vulnerability was recognized as non-critical, because for a successful attack an attacker needs an account on the same Exchange server where the victim is located.
However, the Zero-Day Initiative has now revealed the technical details of the issue and note that some Exchange administrators configure their servers in such a way that it is possible to create a rule to forward mail to an arbitrary location, and in such cases an attacker would not need credentials.
Although the technical details of ProxyToken were only released now, attempts to exploit the vulnerability were recorded three weeks ago. Rich Warren of the NCC Group said he witnessed many attempts to exploit the problem on August 10.
Let me remind you that I also reported that LockFile ransomware adopts ProxyShell and PetitPotam vulnerabilities.