Cisco Talos has discovered a new botnet, Prometei, which was active since March 2020 and focused on mining the Monero (XMR) cryptocurrency. The researchers note that the Prometei botnet intensively uses the SMB protocol for distribution.
The malware mainly attacks users from the USA, Brazil, Pakistan, China, Mexico and Chile. During four months of activity, the botnet operators “earned” about $5,000, that is, an average of about $1,250 per month.
Do you know who else is focused on mining Monero and manipulates a variety of exploits? Lucifer! (don’t be alarmed – this is such malware)
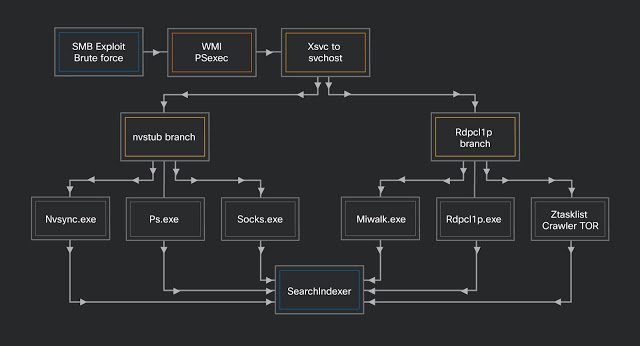
“The malware uses several techniques for distribution, including LOLbins (living off the land) to use legitimate Windows processes to execute malicious code (including PsExec and WMI), SMB exploits (including EternalBlue), and stolen credentials”, – write Cisco Talos experts.
In total, the researchers counted more than 15 ingredients in Prometei. All of them are controlled by the main module, which encrypts (RC4) the data before sending it to the management server via HTTP.
Auxiliary modules can be used to establish communication over Tor or I2P, collect system information, check open ports, spread via SMB, and scan the infected system for any cryptocurrency wallets.
For example, a botnet steals passwords using a modified version of Mimikatz (miwalk.exe), and then passwords are passed to the spreader module (rdpclip.exe) for analysis and authentication via SMB. If that doesn’t work, the EternalBlue exploit is used for propagation.
The final payload delivered to the compromised system is SearchIndexer.exe, which is simply an XMRig version 5.5.3.
However, experts write that Prometei is not just a miner, the malware can also be used as a full-fledged Trojan and info-stealer.
“The botnet is split into two main branches: the C ++ branch is dedicated to cryptocurrency mining operations, and the .NET-based branch focuses on credential theft, SMB attacks and obfuscation. At the same time, the main branch can work independently from the second one, since it can independently communicate with the control server, steal credentials and engage in mining”, – say the researchers.
Cisco Talos experts point out that Prometei is unlike most mining botnets. Its authors not only divided their tools according to their purpose, it also “taught” malware to avoid detection and analysis. In particular, even in earlier versions, you can find several layers of obfuscation, which have become much more difficult in later versions.




