Mobile Security
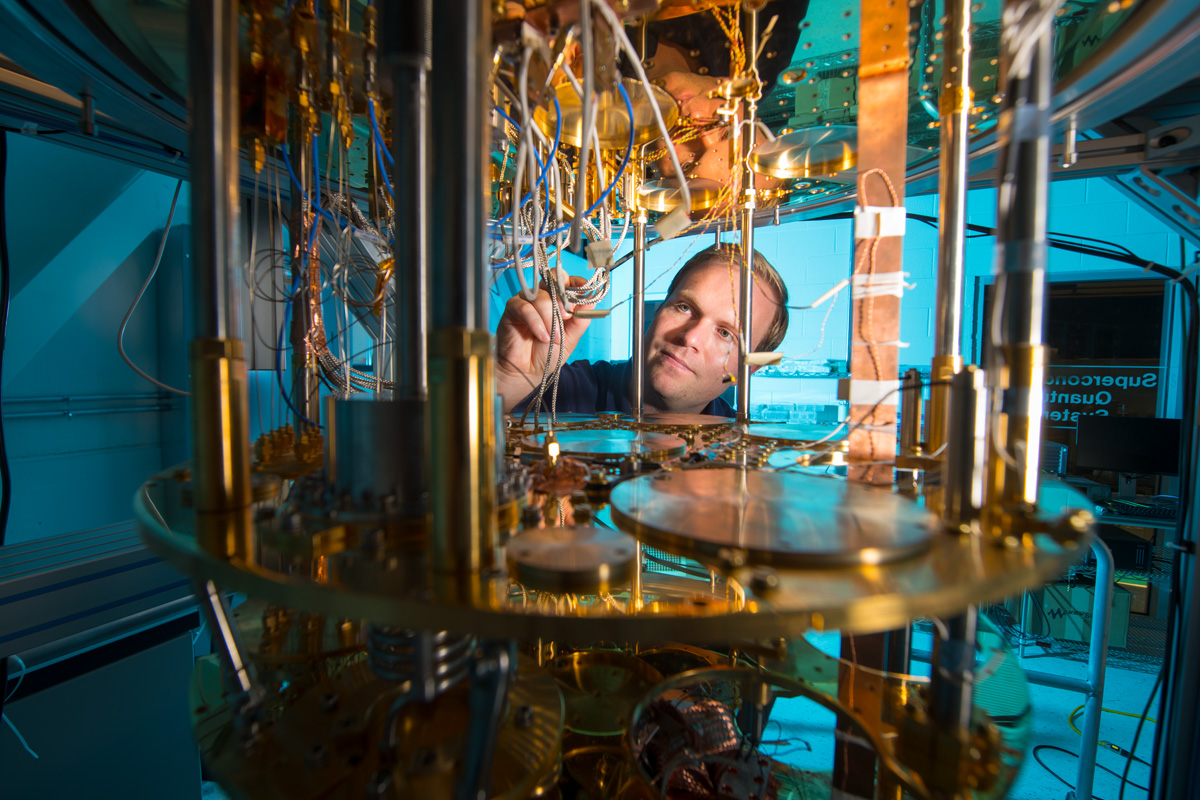
Quantum computers will be able to hack bitcoin wallets
Experts argue that quantum computers will be able to hack bitcoin wallets, but the most advanced cryptographers are in a…
Six 0-day vulnerabilities fixed in Windows, including a commercial exploit issue
As part of June Patch Tuesday, 50 vulnerabilities in Microsoft products were fixed, including six 0-day vulnerabilities in Windows. Vulnerabilities…
NASA has faced 6000 cyberattacks in the past four years
NASA has identified more than 6000 different cyberattacks over the past four years, according to a recent report from the…
Qualcomm Mobile Station Modem vulnerability threatens 40% of smartphones
More than a third of all smartphones in the world have been affected by a new vulnerability in Qualcomm Mobile…
Moxie Marlinspike Demonstrates Cellebrite Tools Vulnerabilities
Signal creator, renowned cryptographer, hacker, researcher and anarchist Moxie Marlinspike studied the products of the famous Israeli cybercriminalistic company Cellebrite…
Malicious Ledger Live extension for Chrome steals Ledger wallet data
Harry Denley, Director of Security in MyCrypto discovered the malicious…
IMP4GT Vulnerability in LTE Threatens Almost All Modern Smartphones
Experts from Ruhr University reported an IMP4GT (IMPersonation Attacks in…
Samsung amends Android kernel that impair security
Jann Horn, Google Project Zero Specialist, studied the Android kernel,…
Xhelper Trojan remains on the device even after resetting to factory settings
Xhelper malware continues to infect Android devices. Moreover, the Xhelper…
Dangerous vulnerabilities in WhatsApp allowed compromising millions of users
Security researcher Gal Weizman from PerimeterX disclosed technical details of…
US authorities can hack iPhone, but may have difficulties with Android
Although the US authorities are persistent in waging a “cryptographic…
97 of the 100 largest airports use vulnerable sites and web applications
Specialists from the Swiss company ImmuniWeb conducted an analysis of…
Government hackers attacked companies more often in 2019
Organizations are more likely to become victims of state-sponsored cybercriminals.…
Greta Thunberg became the most popular character in phishing campaigns
Check Point analysts prepared a traditional monthly report on the…
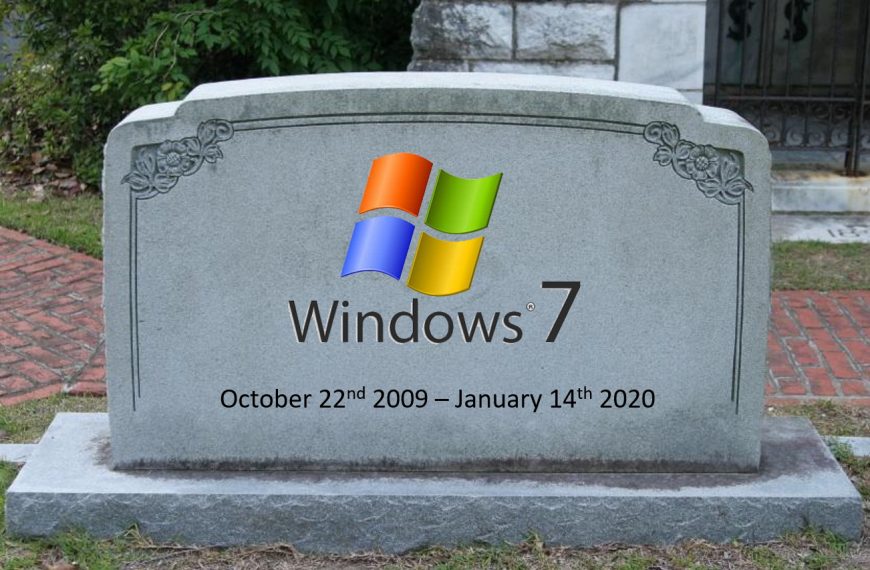
Microsoft released farewell updates for Windows 7 and Windows Server 2008
On January 14, 2020, Microsoft stopped supporting Windows 7 for…
Check Point named the most dangerous malware of November 2019
Check Point Research Team, Check Point® Software Technologies Ltd. (NASDAQ:…
France are looking for LockerGoga ransomware developers in Ukraine
French law enforcement agencies are looking in Ukraine for developers…