Check Point specialists spoke about a dangerous bug they discovered in the WhatsApp image processing function, which could lead to the disclosure of user data.
The problem helped to disable the application, in addition, by applying certain filters to a specially created image and sending it to a potential victim, an attacker could exploit the vulnerability and gain access to confidential information from WhatsApp memory.
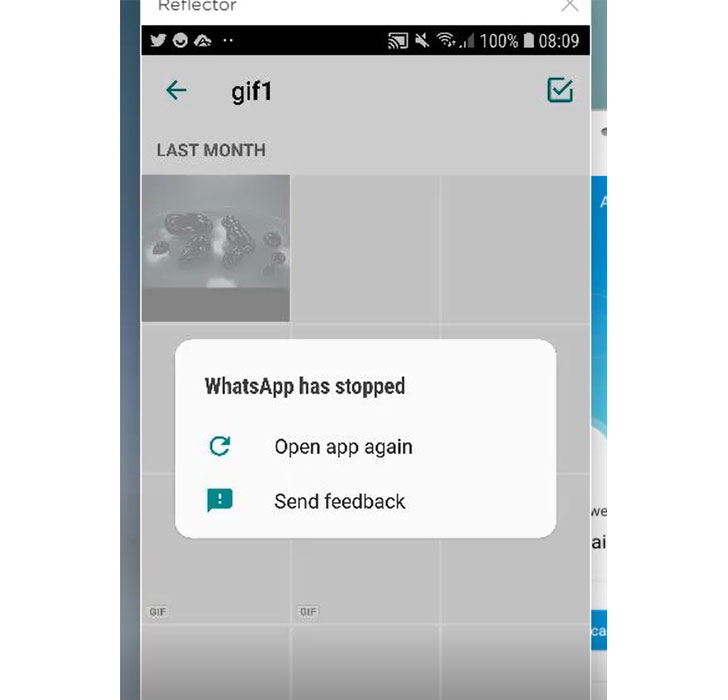
Back in November 2020, experts found out that switching between different filters in specially prepared GIFs caused WhatsApp to crash.
The researchers identified one of the failures as a violation of the integrity of information in memory and immediately reported the problem to the developers, who assigned the problem ID CVE-2020-1910 (7.8 on the CVSS scale), detailing it as a read/write vulnerability out of range (out-of-bounds read-write).
As a result, in February 2021, the WhatsApp developers released a revised version of the app (2.21.1.13), which introduced two new checks for original and modified images.
The root of the problem lies in the “applyFilterIntoBuffer ()” function, which works with image filters: it takes the original image, applies the filter selected by the user to it, and then copies the result to the buffer.
By reverse engineering the libwhatsapp.so library, the researchers found that the vulnerable function works based on the assumption that the original and modified images are the same dimensions and the same RGBA colour format.
Given that each RGBA pixel is stored as 4 bytes, a malicious image with only 1 byte per pixel can be used to gain out-of-bounds memory access as the function tries to read and copy four times as much data from the buffer.
Let me remind you that I also reported that Dangerous vulnerabilities in WhatsApp allowed compromising millions of users.