Sophos experts told about an interesting case when an unnamed auto parts manufacturer was attacked by three different ransomware in a row, in just two weeks.
Let me remind you that we also wrote that New RedAlert Ransomware Targets Windows and Linux VMware ESXi Servers, and also that Hackers Launched LockBit 3.0 and Bug Bounty Ransomware.
Hackers from the LockBit, Hive and ALPHV (BlackCat) groups gained access to the victim’s network on April 20, May 1 and May 15 this year.
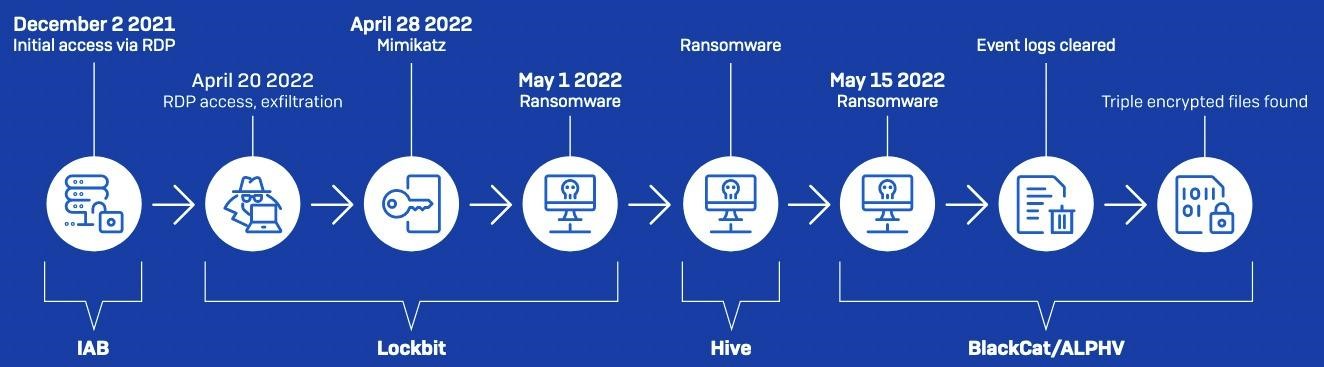
The researchers write that it all started back in December 2021, when the company’s network was compromised by a hacker, apparently an initial access broker. An attacker used a misconfigured firewall to hack into a domain controller server using RDP.
Apparently, after that, the hacker sold access to the victim’s network to other attackers, since three attacks in a row hit the company in the spring.
On May 1, 2022, LockBit and Hive ransomware payloads almost simultaneously spread across the victim’s network using legitimate PsExec and PDQ Deploy tools, and more than a dozen systems were encrypted as a result of each of the attacks. Previously, back in April, LockBit operators managed to steal the company’s data and uploaded it to the Mega cloud storage.
Just two weeks later, on May 15, 2022, while the IT team of the affected company was restoring encrypted systems, hackers from the BlackCat (aka ALPHV) group also connected to the server, previously compromised by their “colleagues” from LockBit and Hive.
Using a legitimate remote access tool (Atera Agent), they gained a foothold in the network and stole data from the company. Half an hour later, BlackCat operators delivered a ransomware payload to the victim’s network using PsExec and encrypted six machines after traversing the network sideways using compromised credentials.
In addition, in the end, BlackCat attackers deleted all shadow copies and cleared event logs on compromised systems, which significantly complicated recovery attempts and incident investigations conducted by Sophos experts.
And although the latest hackers destroyed a lot of evidence, Sophos specialists eventually found files on the affected systems that were encrypted three times with Lockbit, Hive and BlackCat, as well as three different ransom notes.


