The US Infrastructure and Cybersecurity Agency (CISA) warned that a vulnerability in the Windows Print Spooler component, patched by Microsoft in February 2022, is being actively exploited by hackers.
The issue in question is tracked as CVE-2022-22718 (CVSS score of 7.8) and, according to Microsoft, affects all versions of Windows.
At the same time, the company did not disclose almost any technical details of the bug, it was only reported that attackers can use the vulnerability locally, in attacks of low complexity and without any user interaction.
It is worth recalling that last year, Microsoft fought for a long time (and not always successfully) with various bugs in Print Spooler, including a critical PrintNightmare vulnerability that allows remote arbitrary code execution. Then, after accidentally leaking the technical details of the bug and PoC exploit, CISA experts warned administrators that they urgently needed to disable the Print Spooler service on domain controllers and systems not used for printing in order to block potential attacks.
Now, the nature of the attacks on CVE-2022-22718 and the identities of the perpetrators behind them are almost unknown, as the authorities are apparently trying to prevent further exploitation of the problem by other hack groups.
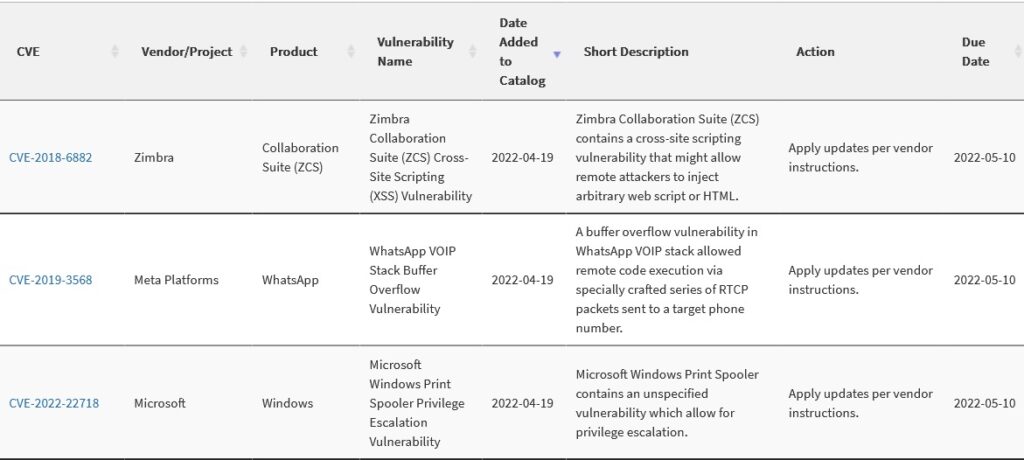
In addition, this week two other issues were added to the CISA catalogue of known exploited vulnerabilities, although they date back to 2018 and 2019:
- CVE-2018-6882 (CVSS score 6.1) – XSS Vulnerability in Zimbra Collaboration Suite (ZCS)
- CVE-2019-3568 (CVSS score of 9.8) is a stack buffer overflow vulnerability in WhatsApp VOIP.




