Calendar Virus on iPhone
Calendar virus on iPhone is a phenomenon where attackers misuse features of…
Your iPhone Has Been Hacked
“Your iPhone Has Been Hacked” is a fake web browser notification designed…
How to Stop Spam Texts?
The spam texts can include spam emails and spam calls. These are…
Scam Likely Calls: How to block them?
Have you ever glanced at your phone and seen the caller ID…
ChatGPT Causes New Wave of Fleeceware
Artificial intelligence is one of the most significant advances in technology. It…
Was Your Apple ID Hacked? Here’s How To Secure Your Account
Apple's services and products are only accessible through their walled garden. Users…
Calendar Virus Removal on iPhones & Mac
Calendar virus may not sound familiar to most users. What’s likely happening…
Spy method NoReboot allows simulating iPhone shutdown and prying through the camera
The NoReboot spy method allows intercepting the iPhone restart and shutdown process…
Vulnerability in Apple iCloud puts billion users at risk
Security of over a billion iPhone owners and users of popular instant…
Experts showed fraudulent payments from a locked iPhone with Apple Pay and a Visa card
Scientists talked about how to make fraudulent payments using Apple Pay with…
Cybersecurity expert created an exploit to hack iPhone via Wi-Fi
Google Project Zero expert Ian Beer has demonstrated an exploit to hack…
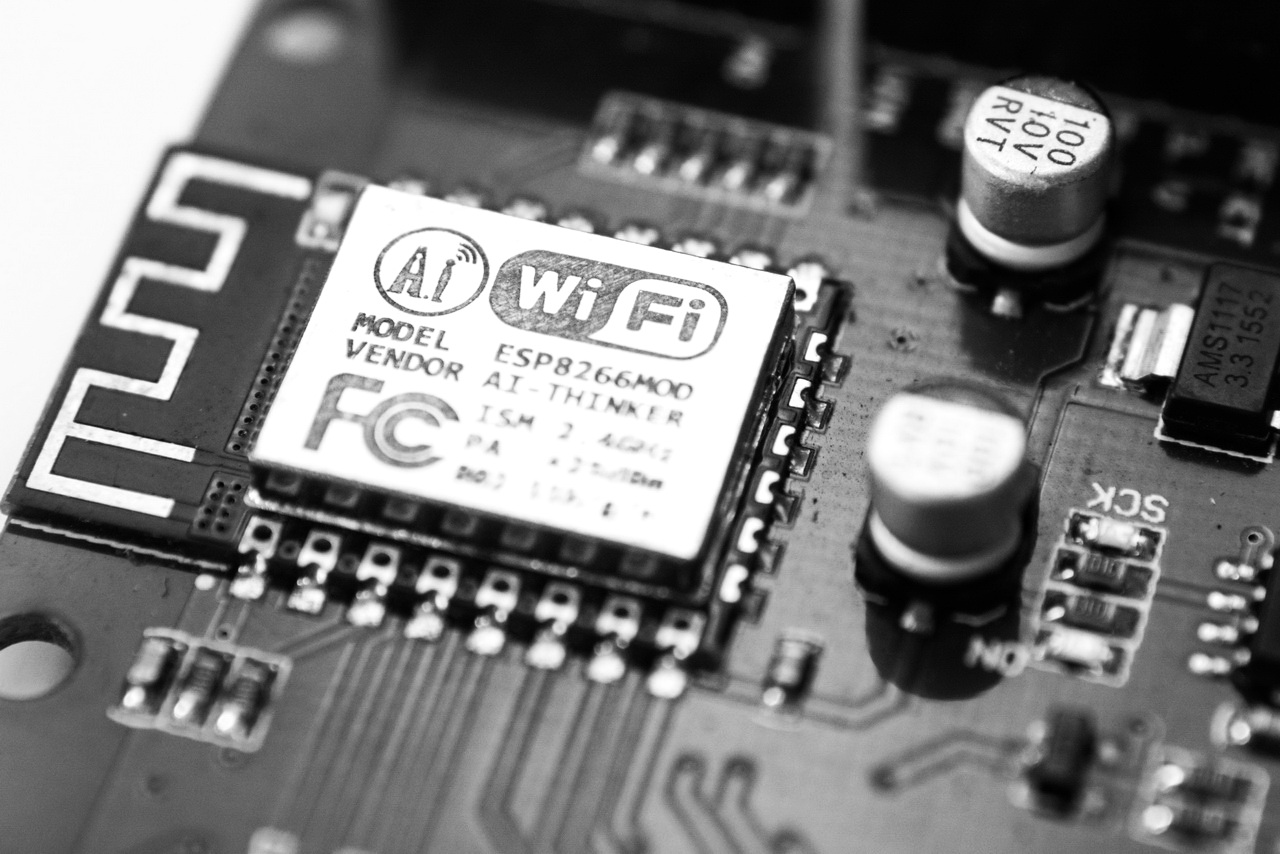
Kr00k problem threatens devices with Qualcomm and MediaTek Wi-Fi chips
In early 2020, ESET experts spoke about the Kr00k vulnerability (CVE-2019-15126), which…