The NoReboot spy method allows intercepting the iPhone restart and shutdown process and prevent them from ever happening.
ZecOps has developed a new method to simulate restarting or shutting down the iPhone and thereby prevent the removal of malware from it, with which hackers can secretly track the victim through the microphone and phone camera.
As a rule, in order to remove malware from an iOS device, simply restart it. The method developed by ZecOps specialists allows to intercept the process of reboots and shutdowns and make it so that they never happen. This way the malware gains persistence on the system as it never actually shuts down.
To restart iPhone, user needs to press and hold the power button or volume control until a slider appears with the option to restart. Then he should wait 30 seconds for the process to complete.
When the iPhone is turned off, the screen goes blank, the camera turns off, the long press does not respond, the ringtone and notification sounds fade and there is no vibration. ZecOps has developed a PoC Trojan capable of injecting special code into three iOS daemons to simulate shutdown by disabling all of these indicators.
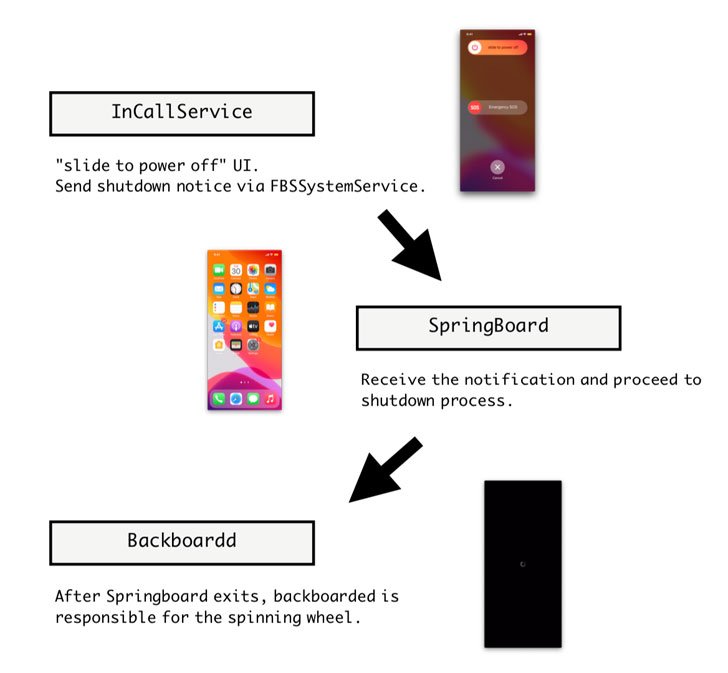
The Trojan interrupts the shutdown event by intercepting the signal from the SpringBoard application that is responsible for interacting with the user interface. Instead of the expected signal, the Trojan sends a code that forcibly terminates SpingBoard, causing the device to stop responding to user actions. It looks like the iPhone is turned off.
The BackBoardd daemon, which logs physical button presses and timestamped screen touches, is then instructed to display a spinning wheel to indicate that the device is turned off. The user thinks that the iPhone has turned off, releases the button ahead of time, and the actual shutdown process never starts.
The video below shows the NoReboot attack in action. Judging by the video, with its help you can very easily convince the victim that her phone is turned off.
You might also be interested to know that Cybersecurity expert created an exploit to hack iPhone via Wi-Fi, and that Vulnerabilities allowed access to cameras on Mac, iPhone and iPad.