Earlier this week, manufacturer of electronics and navigation equipment Garmin suffered a cyberattack and was forced to temporarily shut down a number of services. Now the company said that ransomware attack caused Garmin’s four-day services outage.
At the same time, the incident affected not only wearable gadgets and related services, but also flyGarmin and Garmin Pilot – solutions that support the company’s line of aviation navigation equipment.
From the very beginning, cybersecurity specialists believed that Garmin suffered from the WastedLocker ransomware attack, and now the manufacturer has issued an official statement confirming that the incident indeed was connected with a ransomware attack.
“Garmin Ltd. (NASDAQ: GRMN), today announced it was the victim of a cyber attack that encrypted some of our systems on July 23, 2020. As a result, many of our online services were interrupted including website functions, customer support, customer facing applications, and company communications”, — says the statement.
However, the company’s representatives have not yet named the specific type of malware used in this attack.
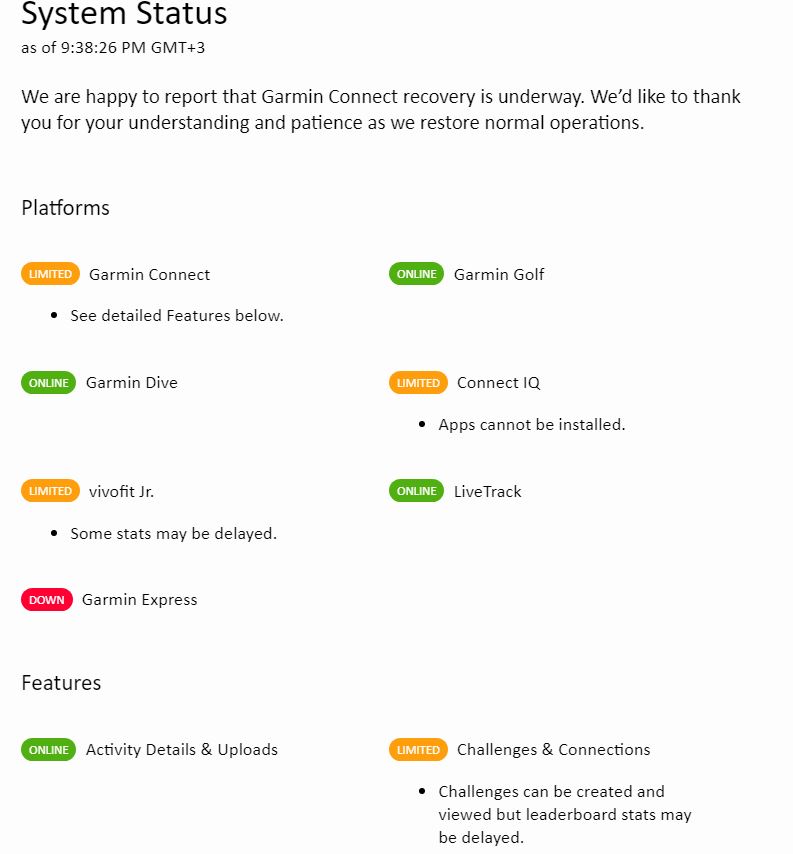
The company says it gradually returns its services to the system. In particular, Garmin Connect and aviation services are already operational (although some are still functioning with restrictions). You can follow the progress of the restoration on a special page.
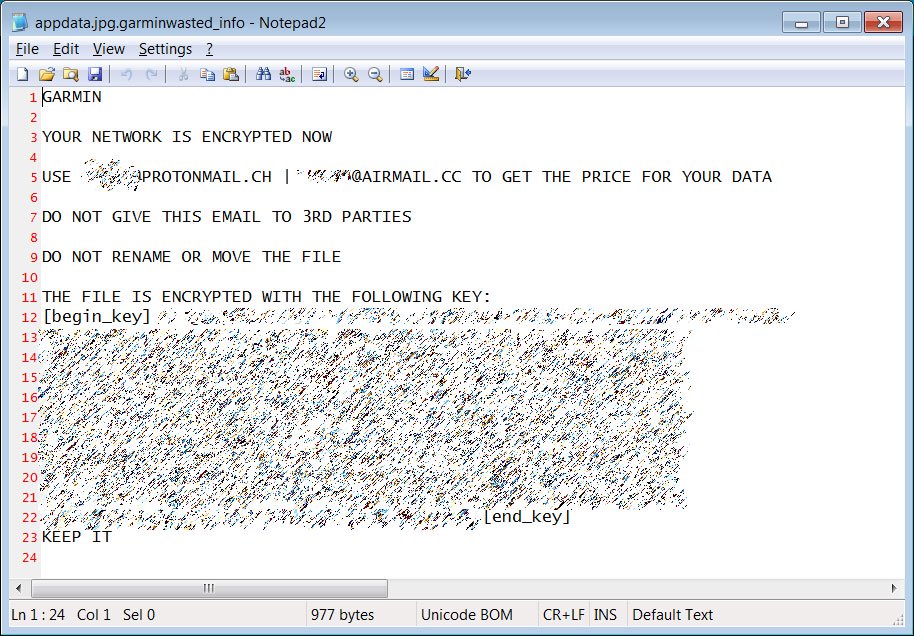
Bleeping Computer, citing its own sources, confidently states that the WastedLocker operators stand behind the attack. For example, journalists had at their disposal a screenshot showing a list of encrypted files on the affected machine. To the filenames has been added the .garminwasted extension .
Soon, researchers were able to find the same WastedLocker strain as used in the attack on Garmin. It turned out that this version of the ransomware actually adds the .garminwasted extension to the files and creates a ransom note addressed specifically to Garmin.
According to Bleeping Computer, the attack on Garmin began with the company’s Taiwan division, and the attackers demanded a ransom of $10,000,000 for decrypting the files.
Let me remind you that WastedLocker activity began in May 2020, and the authorship of this malware is attributed to the Evil Corp group, which is often associated with the Russian special services.
Previously, the ransomware was used exclusively against American companies, and the ransom amounts that Evil Corp demanded from the victims are estimated at millions of dollars. For example, cybersecurity researchers know about a case when hackers asked a company for $10,000,000. In June 2020, analysts wrote that at least 31 American organizations and companies were affected by WastedLocker attacks.





bro, My all files encrypted. My all files extension change in .avdn .How we can solve this problem.
La batería se recalienta y se agota mui rápido ,si mucho gasto de datos moviles ,anuncios invasivos y la pantalla se bloquea ….Sospecho de que otras personas en mi smartphone ben lo que yo veo en mi pantalla,ben mi ubicación GPS ,espían por el micrófono y cámara y incluso controlan la cuenta de Google……
Que puedo acer?
Que antivirus profesional me puedo descargar en Google Play efectivo???