ZDNet reports that on November 1, 2020, Ragnar Locker ransomware operators attacked the Italian beverage manufacturer Gruppo Campari, which owns such brands as Campari, Cinzano, SKYY vodka, Epsolon, Wild Turkey, Grand Marnier and Appleton.
Hackers write that they stole about 2 TB of information from the company. They have already posted screenshots of the stolen data on their website and are demanding about $ 15,000,000 in ransom for restoring the information and removing the stolen data.
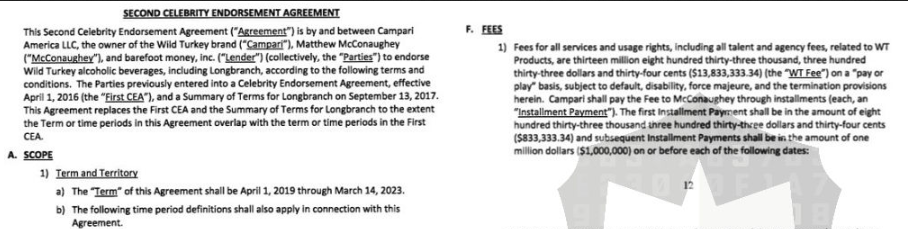
As mentioned above, to prove their words, the hackers published screenshots from the Campari intranet, as well as corporate documents on their darknet site. Among these files, for example, can be find a copy of the contract signed by Campari with the American actor Matthew McConaughey, who advertised Wild Turkey bourbon.
Judging by the chat that Ragnar Locker operators open for their victims, representatives of Gruppo Campari have not yet contacted the ransomware.
According to a short press release from the company, Gruppo Campari chose not to pay the hackers $15 million, but independently restore the damaged data from backups and work on “a gradual restart in safe mode.”
In the same press release, representatives of Gruppo Campari write that they discovered the attack almost immediately and immediately isolated the affected systems, so that the incident should not have a significant impact on the company’s financial position.
However, journalists point out that even now, five days after the attack, Gruppo Campari’s websites, mail servers and telephone lines are still not working.
Let me remind you that researchers from Coveware have provided statistics that ransomwares does not always delete the data it have stolen and made recommendations to potential victims.




