Microsoft continues to investigate the supply chain attack that SolarWinds and its customers have suffered this year. Microsoft analysts reported that SolarWinds hackers were hunting for access to cloud resources.
Let me remind you that unknown hackers attacked SolarWinds and infected its Orion platform with malware.
Among the victims were such giants as Microsoft, Cisco, FireEye, as well as many US government agencies, including the State Department and the National Nuclear Security Administration.
Let me remind you that SolarWinds was hacked because its credentials were publicly available on GitHub.
A new blog post on Microsoft 365 Defender does not contain new technical details, but experts write that they seem to have identified the ultimate goal of the hackers: after infiltrating companies ‘networks using the SUNBURST (or Solorigate) backdoor, hackers sought to gain access to victims’ cloud resources.
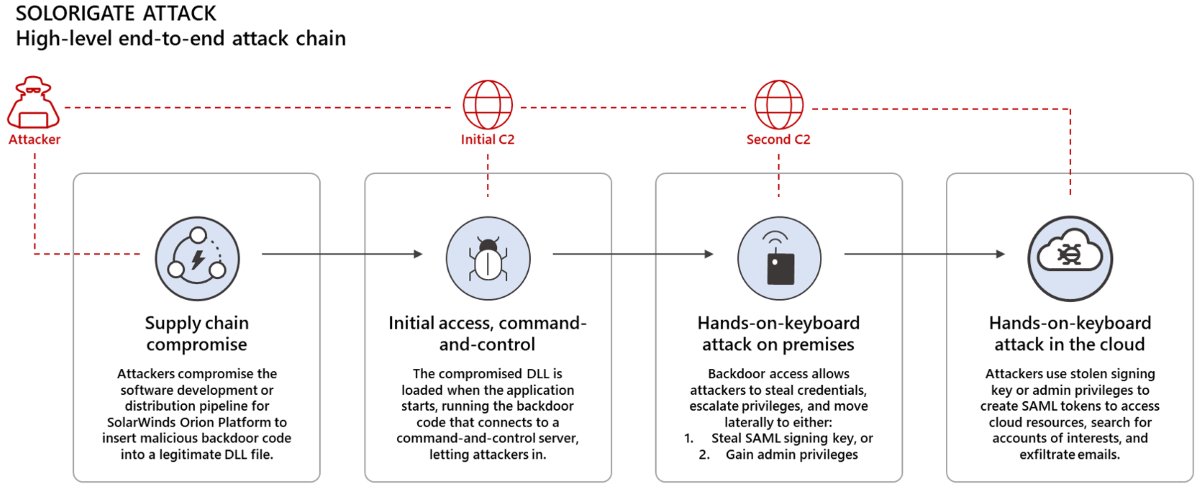
This attack is an advanced and stealthy campaign with the ability to blend in, which could allow attackers to stay under the radar for long periods of time before being detected.
Microsoft experts note that the end goal of the hackers, apparently, was the creation of SAML (Security Assertion Markup Language) tokens in order to forge authentication tokens that provide access to cloud resources. Thus, hackers were able to extract emails from the accounts of interest.
Microsoft detailed the tactics that attackers used to gain access to cloud resources of their victims:
- Using a compromised SolarWinds DLL to activate a backdoor that allowed remote control and operation of the device;
- Using a backdoor to steal credentials, escalate privileges, and sideways to create valid SAML tokens in one of two ways: steal the SAML signing certificate, add or modify existing federation trusts.
- Using generated SAML tokens to access cloud resources and perform actions leading to theft of emails and retain access to the cloud.
Let me also remind you that SolarWinds hack allowed Russian attackers to infiltrated dozens of US Treasury Department mailboxes.