VirusTotal analysts presented a report on the methods that malware operators use to bypass protection and increase the effectiveness of social engineering.
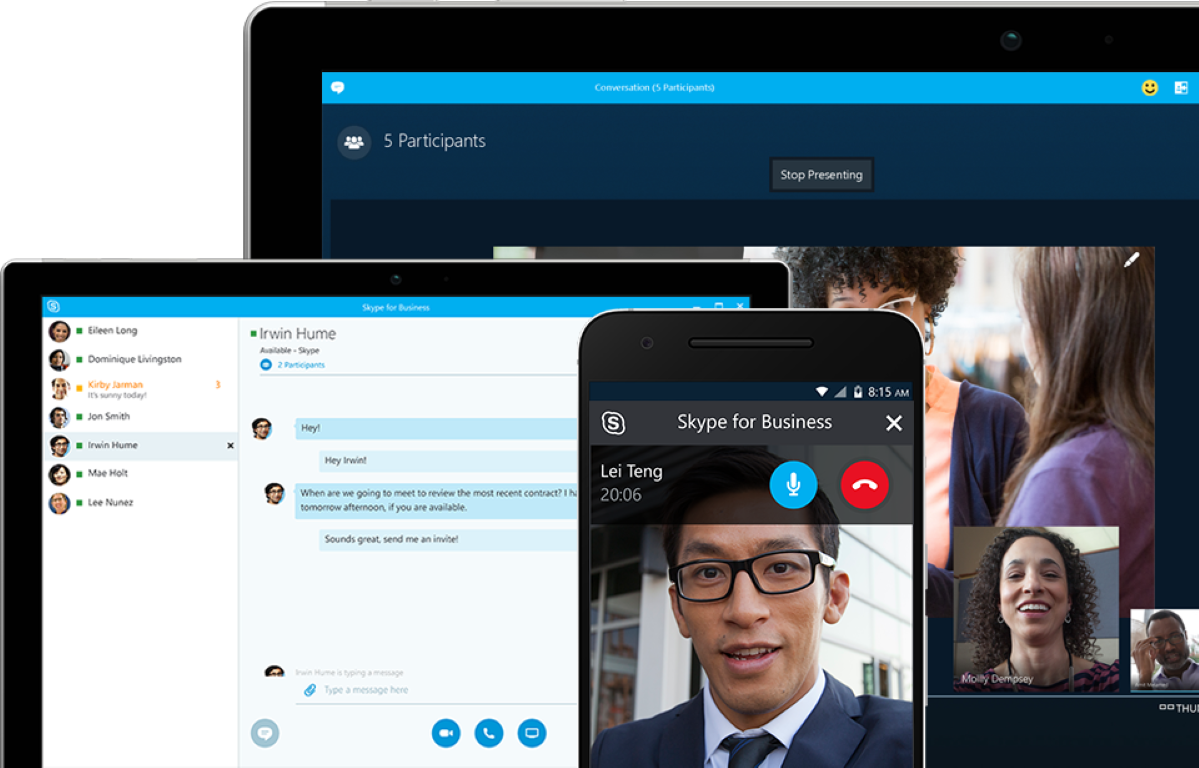
The study showed that attackers are increasingly imitating legitimate applications such as Skype, Adobe Reader and VLC Player to gain the trust of victims.
Let me remind you that we also wrote that Scammers spread malware under the mask of the Brave browser, and also that Hackers majorly use Microsoft and DHL brands in phishing attacks.
Attackers use various approaches to compromise endpoints by tricking users into downloading and running seemingly harmless executable files. Researchers report that in addition to Skype, Adobe Reader and VLC Player, hackers often disguise their programs as 7-Zip, TeamViewer, CCleaner, Microsoft Edge, Steam, Zoom and WhatsApp.
Such deception, among other things, is achieved through the use of legitimate domains in order to bypass firewall protection. Some of the most commonly abused domains are discordapp[.]com, squarespace[.]com, amazonaws[.]com, mediafire[.]com, and qq[.]com.
In total, the experts found at least 2.5 million suspicious files downloaded through 101 domains included in the list of 1000 best sites according to Alexa.
Another commonly used tactic is signing malware with valid certificates, usually stolen from software developers. Since January 2021, VirusTotal has detected over a million malware samples, of which 87% had a legitimate signature when they were first uploaded to the database.
VirusTotal also reports that it found 1,816 malware samples that disguised themselves as legitimate software, hiding in the installers of popular programs, including products such as Google Chrome, Malwarebytes, Zoom, Brave, Mozilla Firefox and Proton VPN.