Google analysts studied the 0-day vulnerabilities they discovered in 2020, and concluded that almost a quarter of the problems are new variations of already known bugs that had previously received patches.
The authors of the report write that many problems could have been avoided if the developers immediately corrected their products more thoroughly.
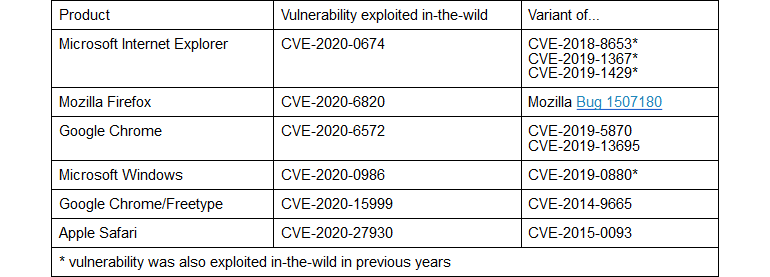
In 2020, thanks to the work of the Google Project Zero team, were identified 24 zero-day vulnerabilities, which were actively exploited by hackers. Six of them (in Chrome, Firefox, Internet Explorer, Safari and Windows) turned out to be new versions of previously known vulnerabilities. Supposedly, attackers carefully studied the old bug reports, figured out the original problems, and then created new versions of exploits for them.
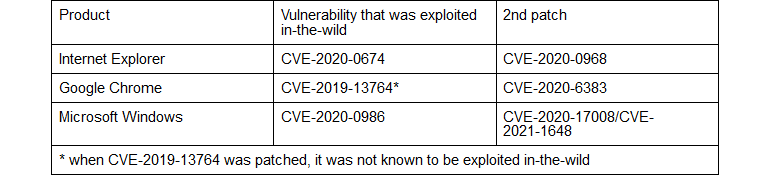
In addition, three other issues that were discovered last year and affected Chrome, Internet Explorer and Windows were not fully fixed, that is, they eventually required additional patches. In fact, if hackers carefully studied the released fixes, they could discover a way to allow them to continue exploiting bugs and attacks.
Google Project Zero experts advise their colleagues to analyze 0-day vulnerabilities deeper and learn to work with such problems. Once the Google Project Zero team was created specifically to search and research zero-day vulnerabilities, and now its experts say that 0-day bugs are a kind of “window” that allows looking into the heads of attackers, learn as much as possible about possible attack vectors , classes of problems and how to deal with them.
Let me remind you that in the fall Google Project Zero discovered a 0-day vulnerability in the Windows kernel.