Researchers at F-Secure hacked a home Bluetooth COVID-19 test and were able to fake the test result.
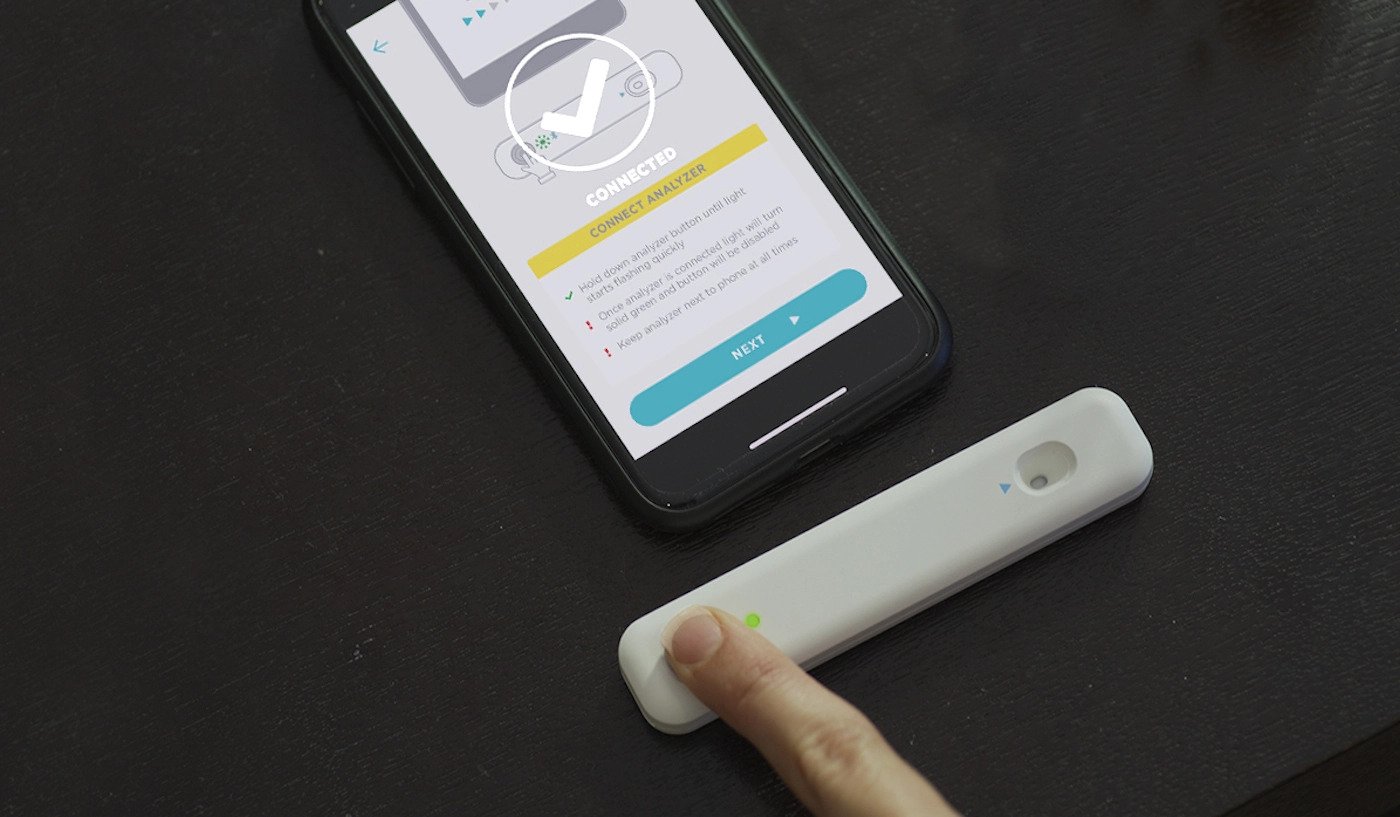
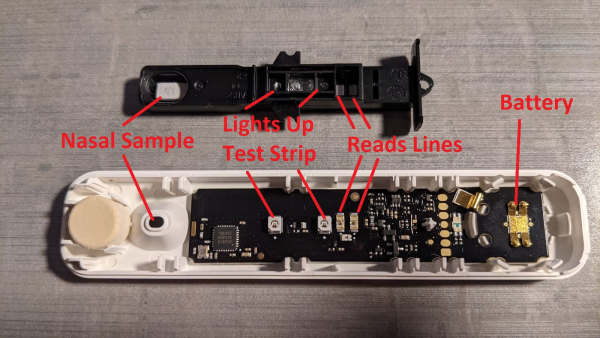
For testing, the experts took the Ellume COVID-19 Home Test device, which uses an analyzer that connects to a smartphone via Bluetooth and works in tandem with the corresponding companion application.
During tests, researchers noticed activity com.ellumehealth.homecovid.android/com.gsk.itreat.activities.BluetoothDebugActivity. It turned out that users with root access can run it to “help interact with the analyser via Bluetooth.”
Further investigation revealed two types of Bluetooth traffic associated with the transmission of test results. The researchers write that they were able to intervene in traffic as follows:
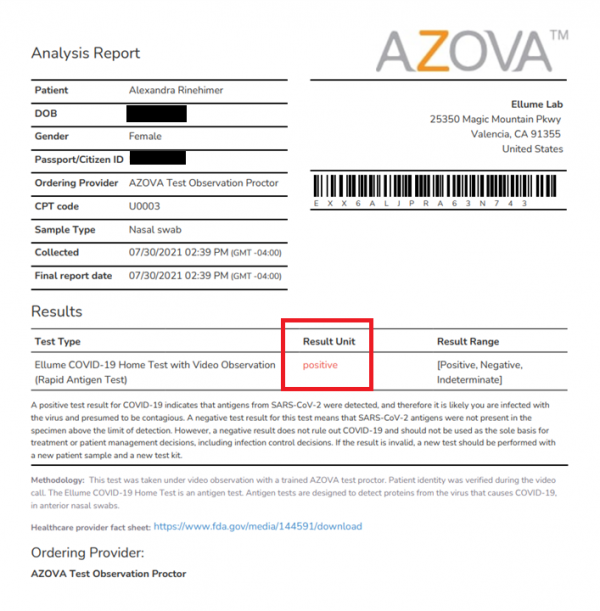
Worse, the fake data provided by Ellume has been successfully accepted by Azova, which certifies COVID test results so that travellers can enter the United States.
Also, the F-Secure report details how one of the company’s employees used the Ellume device to check for COVID, the test turned out negative, but the experts applied the aforementioned methods to change the result.
Researchers from F-Secure shared their best practices on GitHub.
Fortunately, the problem has now been fixed. The specialists notified the Ellume developers of their findings, and they made changes to their product. In particular, additional obfuscation and OS checks were introduced in the Android application, and now additional analysis of test results is being carried out, which is designed to identify fake data.
Let me remind you that I also talked about various fraudulent operations speculating on the COVID-19 topic. For example, that Fake COVID-19 contact tracking apps install banking trojans, and that Cybercriminals attacked UCSF, the US leading COVID-19 vaccine developer. For example, Qatar obliged citizens to install “spyware” for containing COVID-19 pandemic.